
I recently helped a colleague who was in a panic. He’d password-protected a critical project archive a few months back and, of course, completely forgot the password. The deadline was looming, and recreating the work from scratch wasn't an option. This scenario is surprisingly common and highlights a critical intersection of security and accessibility. When you're locked out of your own data, you need a way back in.
This is where password cracking methods come into play, not for malicious purposes, but for legitimate recovery. The most well-known, and often misunderstood, of these is the brute force attack. It’s a term that sounds aggressive, and in many ways, it is—a digital sledgehammer trying to break down a lock. But understanding how it works is key to both recovering your own files and protecting them from others.
Table of Contents
What Exactly Is a Brute Force Attack?
At its core, a brute force attack is the simplest possible method for cracking a password. Imagine a combination lock with three dials. You could patiently try every single combination—000, 001, 002, and so on—until the lock opens. That's a brute force attack in the physical world. In the digital realm, specialized software automates this process for an encrypted file, trying every conceivable combination of letters, numbers, and symbols.
The software doesn't think or strategize; it just churns through possibilities relentlessly. It starts with simple, short passwords ('a', 'b', 'c'...) and systematically increases complexity ('aa', 'ab', 'ac'... '1a', '1b'...). This exhaustive approach guarantees that if the password is within the character set being tested, it will eventually be found. The key word here is *eventually*.
The Mechanics of the Digital Sledgehammer
From a technical standpoint, the process involves a program repeatedly attempting to decrypt a small part of the file with a guessed password. If the decryption check succeeds, the password is correct. If it fails, the program discards the guess and immediately moves to the next one in its sequence. This happens at an incredible speed, with modern computers testing thousands or even millions of passwords per second.
Common Password Cracking Methods Beyond Brute Force
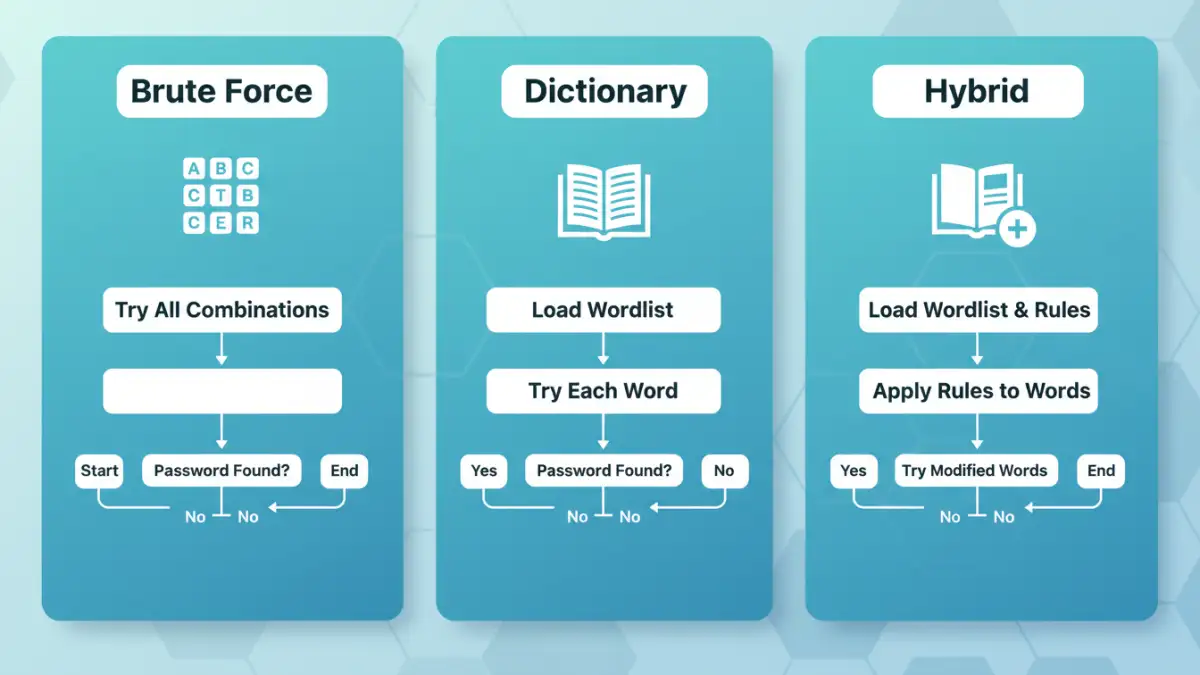
While a pure brute force attack is thorough, it's often inefficient. Because of this, several other password cracking methods have been developed. These are often used in tools designed for legitimate file password recovery to speed up the process.
The Dictionary Attack
Most people don't use truly random passwords like 'xG#7k!zQ'. Instead, they use common words, names, or phrases. A dictionary attack leverages this human tendency. Instead of trying every character combination, it uses a predefined list—or 'dictionary'—of common words, famous names, places, and previously leaked passwords. The software tries each word from the list, which can be dramatically faster than a brute force attempt if the password is simple.
Hybrid and Mask Attacks
A hybrid attack is a clever combination of a dictionary attack and a brute force attack. It takes a word from a dictionary list and then appends or prepends numbers and symbols. For example, it might take the word "password" and try "password123", "Password!", or "2024password". This approach is highly effective because it mimics common password creation patterns.
A mask attack is even more targeted. It's used when you remember parts of the password. For instance, if you know your password was 8 characters, started with 'S', and ended with '23!', you can configure the software to only try combinations that fit that pattern ('S?????23!'). This drastically reduces the number of possibilities and can find the password in a fraction of the time.
Factors That Determine Success (and Failure)
The success of any password cracking attempt hinges on a few critical variables. The difference between a password being found in seconds and one that would take centuries to crack often comes down to these factors.
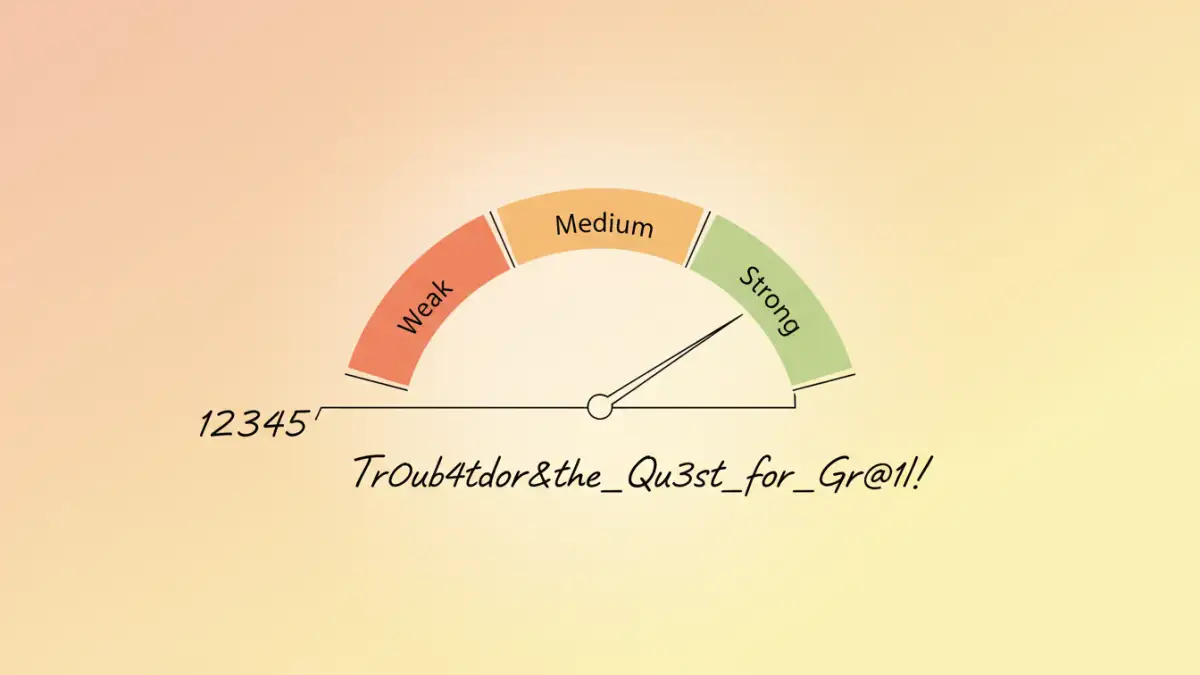
Password Complexity and Length
This is the single most important factor. Each character you add to a password increases the number of possible combinations exponentially. A simple 6-character lowercase password has about 308 million possibilities. An 8-character password using uppercase, lowercase, numbers, and symbols has over 200 trillion. A 12-character password of similar complexity is, for all practical purposes, uncrackable by brute force with current technology.
Hardware Power (CPU vs. GPU)
The speed of the attack is directly tied to the hardware running it. While a standard CPU can test passwords, modern graphics processing units (GPUs) are the real engines of password cracking. A GPU, designed for parallel computations in graphics rendering, can be repurposed to test thousands of password hashes simultaneously. A high-end GPU can be hundreds of times faster than a CPU, turning a year-long task into a day-long one.
Encryption Algorithm Strength
The type of encryption used on the file (e.g., AES-256 for ZIP or RC4 for older PDFs) also plays a role. Stronger, more computationally intensive algorithms slow down the rate at which passwords can be tested, making even simple passwords take longer to crack. However, for most modern files, password complexity remains the primary line of defense.
How to Defend Your Files Against These Attacks
Understanding these attacks gives us the blueprint for defense. The goal is to create a password that makes a brute force or dictionary attack computationally infeasible.
Here are the rules I follow and recommend to everyone:
- Length is King: Aim for a minimum of 12-16 characters. A long, simple passphrase like "MyCorrectHorse-BatteryStaple!" is vastly more secure than a short, complex one like "R#t8!".
- Use a Mix of Characters: Combine uppercase letters, lowercase letters, numbers, and symbols to maximize the number of possible combinations.
- Avoid Dictionary Words: Don't use common words, names, or predictable patterns. If you use a word, modify it significantly (e.g., 'P@55w0rd' is better than 'Password', but a passphrase is still superior).
- Use a Password Manager: The best way to create and manage strong, unique passwords for every file and account is with a password manager. It can generate long, random passwords that are impossible to guess and store them securely for you.
By implementing these strategies, you make the work required for a brute force attack so immense that it's simply not a practical threat for your encrypted file recovery needs or against potential attackers.
Comparison of Password Cracking Methods
| Attack Method | How It Works | Success Rate | Best Against |
|---|---|---|---|
| Brute Force Attack | Tries every possible character combination systematically. | Guaranteed (eventually), but extremely slow for complex passwords. | Short or simple passwords (e.g., '123456' or 'abc'). |
| Dictionary Attack | Uses a list of common words, phrases, and known passwords. | High for common passwords, zero for unique ones. | Passwords based on actual words, names, or simple phrases. |
| Hybrid Attack | Combines dictionary words with numbers and symbols (e.g., 'password' + '123'). | Very high against common user patterns. | Passwords that are slight variations of common words. |
| Mask Attack | Brute forces only a portion of the password based on a known pattern. | Extremely high if parts of the password are known. | Forgotten passwords where the user remembers the structure. |