
The transition to a new security standard always sends ripples through the industry, and the full implementation of PCI DSS 4.0 is no exception. While much of the focus has been on network security and software development, a critical, often overlooked area is undergoing significant change: document handling. It’s no longer enough to just encrypt your database; the new standard takes a much closer look at every file, report, and log that might contain sensitive payment information.
As an engineer who has helped organizations navigate these compliance shifts, I've seen firsthand how seemingly small procedural changes can have a massive impact on security posture. The latest updates from the Payment Card Industry require a more proactive and granular approach to protecting data wherever it resides, especially in documents that are frequently shared, stored, and archived.
Table of Contents
Understanding the Shift to PCI DSS 4.0
The Payment Card Industry Data Security Standard (PCI DSS) has always been the benchmark for protecting cardholder data. Version 4.0 represents the most significant evolution in years, moving from a rigid, prescriptive model to a more flexible, objective-based framework. This change is designed to accommodate the diverse and rapidly evolving technological landscapes of modern businesses.
The Customized Approach Explained
One of the landmark changes is the introduction of the 'Customized Approach'. This allows organizations to meet a requirement's objective using innovative technologies and processes that may not fit the traditional, 'Defined Approach'. However, this flexibility comes with a price: the burden of proof is now squarely on the organization. You must provide extensive documentation, perform rigorous testing, and prove that your custom solution offers security equal to or greater than the prescribed control. For document management, this means you can use a new cloud-native AI-powered tool, but you better be ready to validate its effectiveness thoroughly.
Key Document Handling Changes in Version 4.0

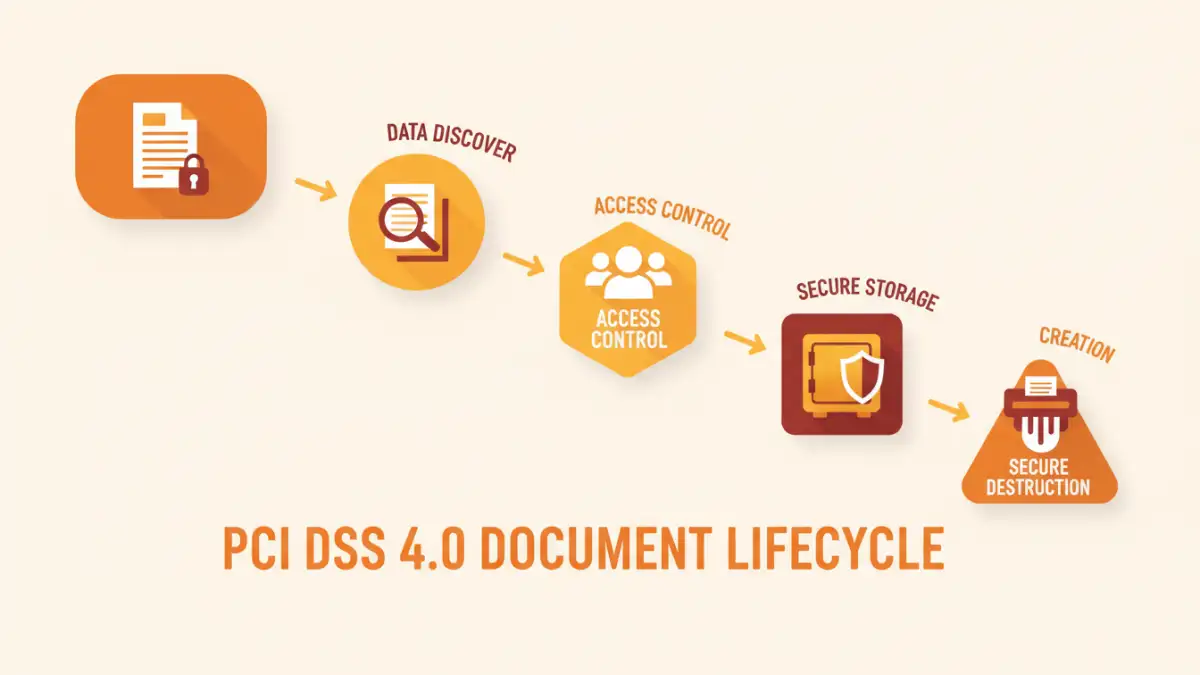
When we talk about pci dss secure documents, we're referring to any file, digital or physical, that contains cardholder data (CHD) or sensitive authentication data (SAD). This includes everything from transaction logs and spreadsheets to customer service records and printed receipts. PCI DSS 4.0 intensifies the scrutiny on how these are managed throughout their lifecycle.
Enhanced Encryption and Data Discovery
Previously, encryption of the Primary Account Number (PAN) was a core requirement, but 4.0 places a stronger emphasis on its implementation. Requirement 3.5.1.2, for example, specifies that hashes used to render PAN unreadable must include the entire PAN. More importantly, the standard pushes for better data discovery processes. You can't protect what you don't know you have. Organizations are now expected to have robust mechanisms for identifying and tracking all locations where cardholder data is stored in documents, which is often more challenging than locating data in structured databases.
Stricter Access Control and Monitoring
The principle of 'least privilege' gets a major boost. Requirement 7 has been updated to demand more granular access controls not just for systems, but for the data itself. For documents, this means implementing Role-Based Access Control (RBAC) within your document management systems is no longer just a best practice—it's essential for compliance. Recently, I worked with a client whose flat file-sharing system had to be completely overhauled to introduce user-specific permissions for accessing financial reports, a direct result of these updated guidelines.
Practical Steps for Compliance
Adapting to these compliance changes can feel daunting, but a structured approach makes it manageable. It starts with a comprehensive understanding of your data landscape.
Conduct a Thorough Data Footprint Analysis
Your first step should be to map every process that creates, touches, or stores documents with cardholder data. This includes automated report generation, manual data entry, customer support logs, and even temporary files. Use data discovery tools to scan file shares, cloud storage, and local drives to build an accurate inventory. This inventory is the foundation of your entire document security strategy.
Update Your Data Retention and Disposal Policies
PCI DSS 4.0 requires clear policies for data retention and disposal. Don't keep documents containing sensitive data longer than necessary for business, legal, or regulatory purposes. Your policy should define minimum and maximum retention periods for different document types. Furthermore, ensure your disposal methods, whether for digital files or physical papers, are secure. This means using cryptographic erasure for digital media and cross-cut shredding or incineration for paper records.
The Role of Technology and Automation
Manual compliance is prone to error and simply not scalable. Leveraging the right technology is key to meeting the new data security standard effectively.
Implementing Data Loss Prevention (DLP)
DLP solutions are invaluable for enforcing your policies automatically. They can be configured to scan outbound emails, monitor file transfers, and block unauthorized movement of documents containing patterns that match cardholder data. A well-configured DLP system can be a safety net, preventing accidental data leakage and helping you prove compliance during an audit.
Leveraging Secure Document Management Systems
Modern Document Management Systems (DMS) come with built-in features that align with PCI DSS requirements. Look for platforms that offer granular access controls, detailed audit trails of who accessed which document and when, and integrated encryption for data at rest. Migrating your sensitive documents from open file shares to a secure DMS is a significant step toward robust financial document security.
PCI DSS 3.2.1 vs. 4.0: Document Handling Comparison
| Requirement Area | PCI DSS 3.2.1 Approach | PCI DSS 4.0 Approach | Key Change/Emphasis |
|---|---|---|---|
| Data Storage & Encryption | Required rendering PAN unreadable wherever it is stored. | More specific requirements for encryption, hashing, and tokenization. Emphasizes protecting PAN everywhere it is stored. | Increased specificity and a push towards stronger, industry-accepted cryptographic methods. |
| Access Control | Access needs to be based on job classification and function ('need-to-know'). | Requires access reviews at least every six months. Mandates assigning access based on the principle of least privilege. | More frequent reviews and a stricter definition of access rights. |
| Data Retention Policy | Required a policy that defined data retention and secure deletion. | Policy must define retention periods for all cardholder data, with explicit requirements for secure deletion. | Greater clarity and enforcement on having a defined, followed policy. |
| Physical Media | Required secure storage and destruction of media containing cardholder data. | Maintains requirements for secure storage and destruction, with added focus on media sent outside the organization. | More attention on the entire lifecycle, including external transit. |
| Monitoring & Logging | Required audit trails for all system components. | Audit logs must be reviewed using automated mechanisms or a combination of manual and automated processes. | Emphasis on automated analysis to detect anomalies faster. |