
Strong document encryption is no longer a luxury; it's a fundamental necessity for protecting sensitive information from unauthorized access and potential breaches. For years, I've worked with teams struggling to balance security with usability, often relying on a patchwork of tools that create more problems than they solve. A simple password on a PDF just doesn't cut it for serious enterprise document security.
That's why our team has been working on a solution that addresses these challenges head-on. Today, I'm thrilled to introduce a comprehensive new suite designed to provide robust, intuitive, and scalable protection for your most critical assets.
Table of Contents
The Evolving Landscape of Document Security
The way we share information has changed dramatically. Collaboration happens across departments, time zones, and even organizations. While this accelerates productivity, it also expands the attack surface for sensitive data. Relying on basic, built-in file passwords creates significant vulnerabilities.
I've seen firsthand how easily these basic protections can be bypassed. A forgotten password can lock a team out of a critical project file, while a simple brute-force attack can expose confidential client data or intellectual property. The need for a more dynamic and intelligent approach to security has never been clearer.
Limitations of Traditional Encryption
Traditional methods often fall short in a modern enterprise environment. They typically lack granular control, meaning you can either lock the entire document or leave it completely open. There's no middle ground for setting different permissions for different users, such as view-only, edit, or print restrictions.
Furthermore, these methods offer no visibility. Once a password-protected file is sent, you lose all control and insight into who is accessing it, when, and from where. This lack of an audit trail makes it impossible to ensure compliance or investigate potential security incidents effectively.
Introducing the Sentinel Encryption Suite

Our new Sentinel Encryption Suite was built from the ground up to provide a holistic solution for modern file security challenges. It's more than just a tool; it's a platform for managing the entire lifecycle of your sensitive documents, from creation to archival.
We focused on three core pillars during development: impenetrable security, seamless usability, and comprehensive administrative oversight. This ensures that protecting your data doesn't come at the cost of your team's productivity. The suite integrates AES-256 bit encryption, the same standard trusted by governments and financial institutions worldwide.
Core File Security Features
The Sentinel Suite is packed with powerful file security features designed for the modern enterprise. Key capabilities include:
- Granular Access Controls: Assign specific permissions (view, edit, print, download) on a per-user or per-group basis. You can even set expiration dates for access or revoke it in real-time.
- Dynamic Watermarking: Automatically apply dynamic watermarks to documents that include the viewer's name, IP address, and timestamp. This deters unauthorized sharing and screenshots.
- Comprehensive Audit Trails: Track every interaction with your secured files. Our dashboard provides a detailed log of who accessed what, when, and from which location, ensuring full accountability.
- Centralized Policy Management: Define and enforce security policies across your entire organization from a single, intuitive admin console. This makes scaling your security efforts simple and consistent.
How Our New Encryption Software Works
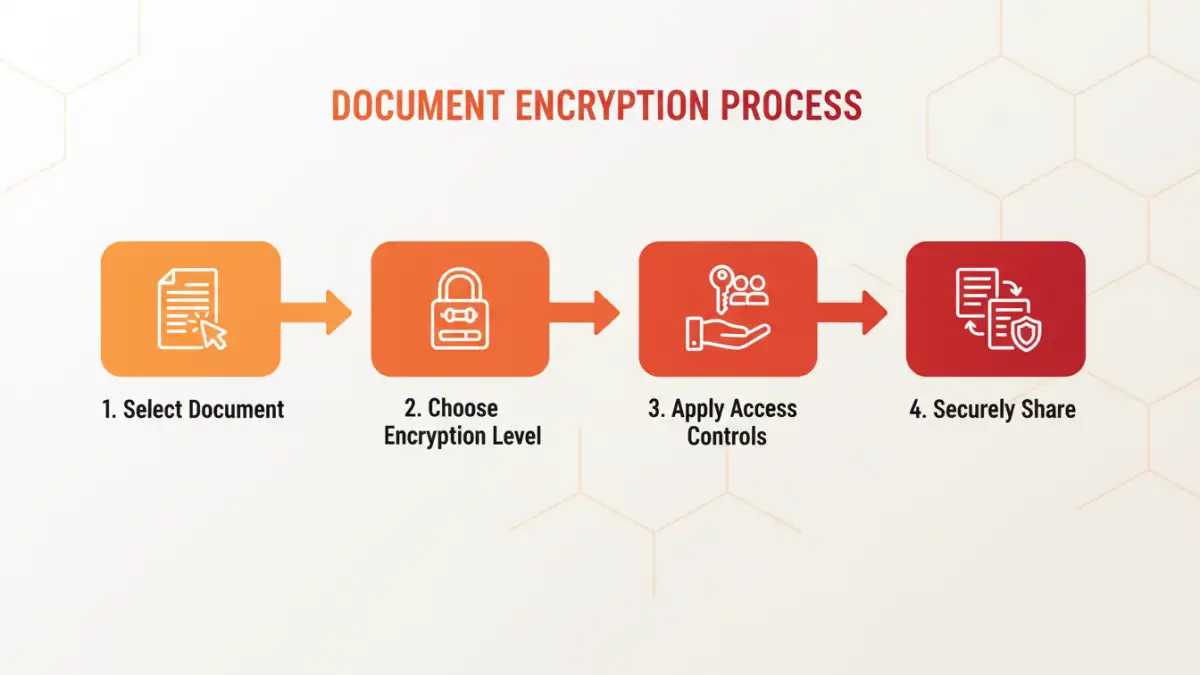
The process is designed to be straightforward. Instead of relying on static passwords, our software wraps your document in a secure, encrypted container. This container communicates with our server to verify a user's identity and permissions before granting access.
When a user attempts to open a protected file, they must authenticate themselves. Our system then checks the policies you've set for that specific user and document. If they have the appropriate rights, the file is decrypted locally for their use, according to the permissions granted. This entire process is fast, seamless, and happens in the background.
A Look at the Encryption Process
Securing a file is as simple as a right-click or drag-and-drop action. You select the document, choose the security policy you want to apply, and our software handles the rest. This approach removes the burden of managing complex passwords from the end-user, reducing human error and strengthening your overall security posture.
This is a significant PDF protection update for organizations that handle sensitive contracts or reports. The ability to revoke access to a PDF even after it has been sent provides an unprecedented level of control.
Key Benefits for Your Enterprise
Adopting our suite offers tangible benefits that go beyond just locking a file. It empowers your organization with proactive control over its most valuable digital assets. You can confidently collaborate with external partners, knowing your intellectual property remains protected.
This solution for advanced document encryption helps you meet stringent compliance requirements like GDPR, HIPAA, and CCPA by providing demonstrable control and auditability over personal and sensitive data. Ultimately, it provides peace of mind, allowing your team to focus on its core objectives without worrying about data leaks.
Sentinel Suite vs. Standard Encryption
| Feature | Sentinel Encryption Suite | Standard Built-in Encryption | Business Impact |
|---|---|---|---|
| Access Control | Granular (per-user, per-group) | All-or-nothing (single password) | Prevents unauthorized internal access. |
| Access Revocation | Real-time, remote revocation | Not possible once shared | Mitigates damage from leaks immediately. |
| Audit Trail | Detailed logs of all activity | None | Enables compliance and forensic analysis. |
| Dynamic Watermarking | Yes, user-specific | No | Deters screenshots and unauthorized sharing. |
| Policy Management | Centralized and scalable | Manual, per-file basis | Ensures consistent security across the org. |
| Authentication | Multi-factor options | Shared password | Drastically reduces risk of compromised credentials. |