
I often see teams breathe a sigh of relief after implementing password protection on a sensitive document. They believe the job is done. But a simple password on a PDF or a ZIP file doesn't automatically satisfy the stringent requirements of the General Data Protection Regulation (GDPR). The regulation demands a more thoughtful, risk-based approach to securing personal data.
Simply 'encrypting' a file is just one piece of a much larger puzzle. The real questions are: how strong is the encryption, who holds the keys, and can you prove you've taken appropriate measures to protect the data? Answering these is crucial for avoiding hefty fines and maintaining trust.
Table of Contents
What GDPR Actually Says About Encryption
A common misconception is that GDPR mandates a specific type of encryption. It doesn't. Instead, Article 32, "Security of processing," states that controllers and processors must implement "appropriate technical and organisational measures" to ensure a level of security appropriate to the risk. Encryption is explicitly listed as one of these potential measures.
This language gives organizations flexibility but also places the burden of proof on them. You must be able to justify your chosen security measures. If a data breach occurs and the compromised data was unencrypted or weakly encrypted, regulators will question whether your measures were truly 'appropriate'.
Encryption as a Safeguard
Strong encryption acts as a powerful safeguard. Under GDPR, if personal data is rendered unintelligible to any person not authorized to access it (i.e., properly encrypted), the notification obligations to the data subjects in the event of a breach may be waived. This makes a robust encryption strategy not just a protective measure, but also a critical component of your incident response plan.
The Role of Pseudonymisation
GDPR also highlights pseudonymisation, which involves processing personal data in such a way that it can no longer be attributed to a specific individual without the use of additional information. This additional information must be kept separately and securely. Encryption is a primary method for achieving pseudonymisation, adding another layer to your data protection regulation compliance.
Common Document Encryption Pitfalls

In my work, I've seen several recurring mistakes that can undermine an otherwise well-intentioned security plan. These are the gaps that a compliance audit will quickly expose.
Weak Encryption Standards
Using outdated algorithms or short, simple passwords for document protection is a major red flag. For instance, older versions of PDF encryption or ZIP file password protection are notoriously easy to break with modern computing power. Relying on these is like using a simple padlock to protect a bank vault.
Poor Key Management
This is perhaps the most frequent failure I encounter. You can have the strongest encryption in the world, but if the key (the password or certificate) is mishandled, the security is worthless. Sending a password in a separate email, storing it in a plaintext file on a shared drive, or using the same key for hundreds of documents are all practices that negate the benefits of encryption.
Lack of Access Control and Auditing
Encrypting a file is only half the battle. You also need to control who can access it and decrypt it. A compliant system must include robust access controls and maintain logs of who accessed which documents and when. Without an audit trail, you cannot demonstrate control over the data, which is a core tenet of GDPR.
Building a Compliant Encryption Strategy
A defensible gdpr document encryption strategy is built on a foundation of risk assessment and clear processes. It's not just about installing a tool; it's about integrating security into your data lifecycle.
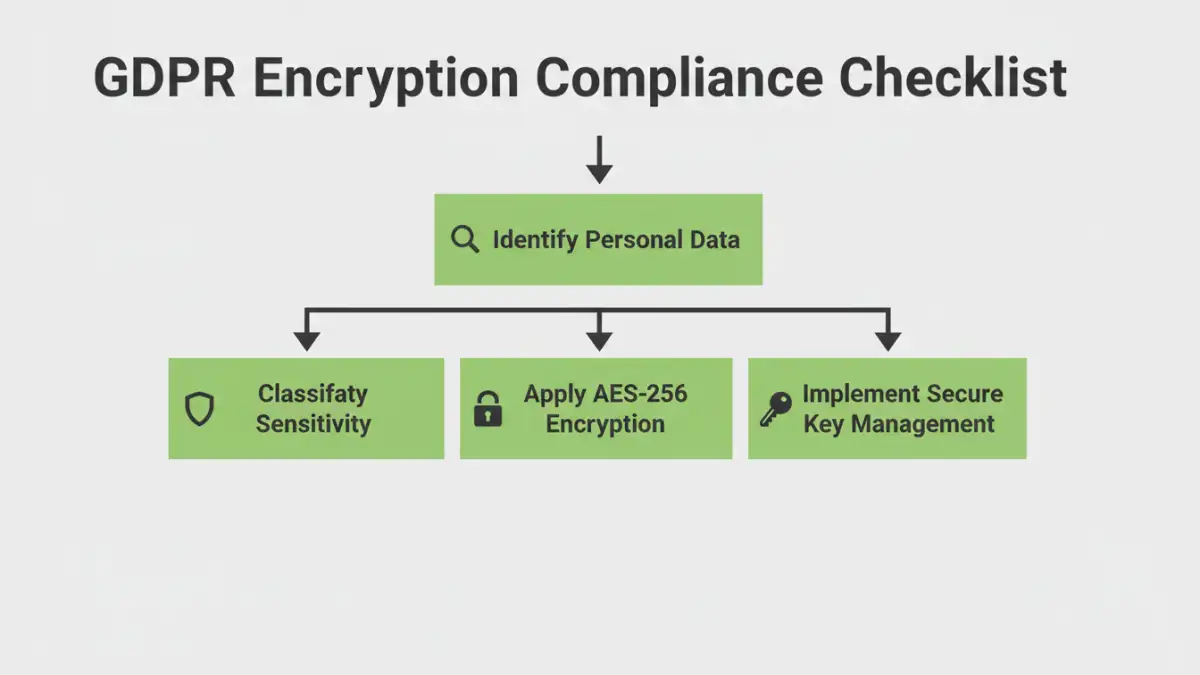
Step 1: Data Discovery and Classification
You cannot protect what you don't know you have. The first step is to identify all the places where personal data is stored. Once identified, classify the data based on its sensitivity. Not all personal data carries the same level of risk. A list of customer email addresses requires different protection than a file containing detailed medical records.
Step 2: Adopting Strong Encryption Standards
For both data at rest (stored on a drive) and data in transit (sent over a network), you should standardize on proven, modern encryption protocols. AES (Advanced Encryption Standard) with a 256-bit key is the industry benchmark for data at rest. For data in transit, TLS 1.2 or higher is essential for secure file sharing and communication.
Step 3: Implementing Secure Key Management
Your strategy must define how encryption keys are generated, distributed, stored, rotated, and ultimately destroyed. Using a dedicated key management system (KMS) or a secure password manager is far superior to ad-hoc methods. The principle of least privilege should apply: only authorized individuals should have access to the keys needed for their roles.
Practical Tools and Technologies for Compliance
Implementing your strategy requires the right set of tools. These can range from features built into operating systems to specialized enterprise solutions.
Encryption at Rest
Solutions like Microsoft's BitLocker (for Windows) and Apple's FileVault (for macOS) provide full-disk encryption, protecting all data on a device if it's lost or stolen. For individual files or folders, tools that offer container-based encryption or specific pdf encryption with AES-256 are suitable choices.
Encryption in Transit
This is typically handled by protocols like TLS/SSL for web traffic and secure email gateways (e.g., S/MIME or PGP). When using cloud services or platforms for secure file sharing, ensure they enforce TLS for all data transfers and provide clear information on their data protection measures.
Access Control and Audit Trails
Enterprise-grade document management systems and secure collaboration platforms often have these features built-in. They allow you to set granular permissions (who can view, edit, or decrypt) and provide detailed logs that are invaluable during a compliance audit. These systems centralize control, preventing the chaos of scattered, inconsistently protected files.
Encryption States and GDPR Compliance
| Encryption State | Description | GDPR Relevance | Common Technologies |
|---|---|---|---|
| Data at Rest | Data that is stored on physical media, such as hard drives, servers, or cloud storage. | Protects against physical theft or unauthorized access to storage systems. Critical under Article 32. | AES-256, BitLocker, FileVault, Database TDE |
| Data in Transit | Data that is actively moving from one location to another, such as across the internet. | Prevents eavesdropping or 'man-in-the-middle' attacks during data transfer. | TLS 1.2+, SSL, HTTPS, SFTP |
| Data in Use | Data being processed by an application or in active memory (RAM). | An advanced area of protection; protects data during processing from compromised system processes. | Confidential Computing, Secure Enclaves |
| Key Management | The processes and systems for managing cryptographic keys throughout their lifecycle. | Ensures encryption remains effective. Poor key management can render encryption useless. | KMS, HSMs, Secure Password Managers |