
A colleague once frantically called me, locked out of a critical encrypted ZIP file hours before a deadline. The password was 'somewhere in his notes.' This scenario highlights a common confusion I see: the line between recovering a password and cracking it. While they might sound similar, they represent two fundamentally different worlds—one of legitimate access and the other of unauthorized intrusion.
Understanding this distinction is crucial for anyone handling sensitive data. It’s not just semantics; it’s the core of how we approach protecting our digital assets. One path is about helping the rightful owner regain access, while the other is about breaking in.
Table of Contents
The Core Difference: Recovery vs. Cracking
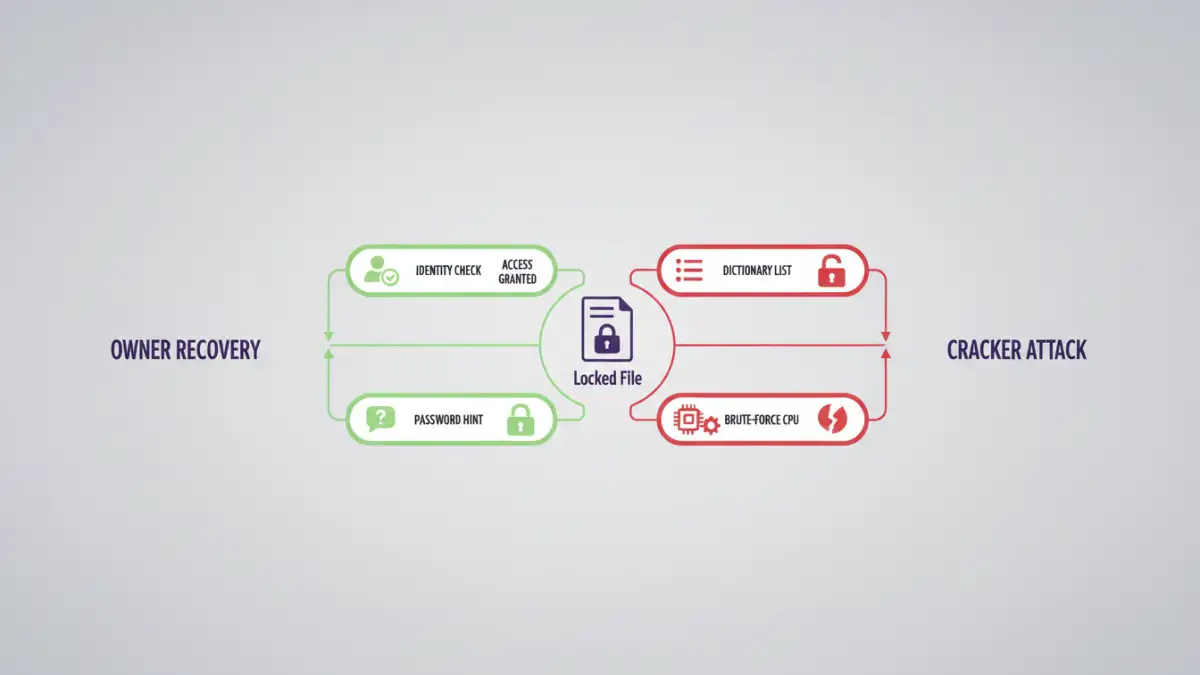
At its heart, the difference is about intent and permission. One is a rescue mission for your own data; the other is a heist. Conflating the two can lead to poor security practices and a false sense of protection.
What is Password Recovery?
Document password recovery is the authorized process of regaining access to a file you own but have lost the password for. Think of it as using a spare key. This process often relies on pre-established mechanisms, like security questions, a backup email, or a master password from a password manager. The system is designed to verify your identity before granting access.
For locally encrypted files without a built-in recovery mechanism, the process is more about jogging your memory or using tools that systematically test variations of passwords you might have used. The key here is that you are the legitimate owner trying to access your own information.
What is Password Cracking?
Password cracking, on the other hand, is an unauthorized attempt to gain access to a file. The attacker has no legitimate claim to the data. They use computational power and clever algorithms to guess the password, bypass security, or exploit a vulnerability. This is the digital equivalent of a safecracker trying every possible combination.
This is where concepts like brute-force attacks and exploiting an encryption weakness come into play. The goal is to break the lock, not to be recognized as the owner.
How Document Password Recovery Works

Legitimate recovery focuses on leveraging information that only the owner would likely possess. It's a process of guided assistance rather than a brute-force assault.
Using Hints and Metadata
Some systems allow you to set a password hint. While this seems helpful, I generally advise against it, as a poorly chosen hint can give an attacker a massive head start. Metadata within a file can sometimes provide clues, such as the author's name or creation date, which might be part of a predictable password pattern.
Systematic Guessing Based on User Info
Recovery tools, when used by the owner, can be configured with personal information to narrow down the possibilities. You might input important dates, names of pets, old street addresses, or common password patterns you've used before. The software then intelligently combines these elements, which is far more efficient than trying every character combination in the universe.
A Look into Password Cracking Techniques
Cracking tools don't have the luxury of personal hints. Instead, they rely on raw power and sophisticated algorithms to find the key. This is a critical part of any security vulnerability analysis, as we need to understand the attacker's methods to build strong defenses.
Brute-Force and Dictionary Attacks
A brute-force attack is the most straightforward method: the software tries every possible combination of letters, numbers, and symbols until it finds the correct one. A dictionary attack is a smarter version, using a list of common words, phrases, and previously leaked passwords. A hybrid attack combines these, trying variations like 'Password123!' or 's3cur1ty'.
Exploiting Encryption Weakness
This is a more advanced technique. Older file formats, like early versions of Microsoft Office or ZIP, used weaker encryption algorithms. Some of these have known vulnerabilities that can be exploited to find the password much faster than a brute-force attack would allow. A common goal for attackers is a PDF password bypass, which is often possible on documents with older, less robust security settings. Modern encryption standards like AES-256 are significantly harder to crack.
Practical Implications for Your Files
Understanding these methods provides a clear roadmap for protecting your documents. It’s not about making them impossible to crack—with enough time and resources, anything is possible—but about making it so difficult and time-consuming that it's not worth the attacker's effort. This simple file security breakdown should guide your choices.
Use Strong, Modern Encryption
When you have the option, always choose the strongest encryption available. For example, when password-protecting a PDF or ZIP file, look for AES-256 encryption. This is the current industry standard and is resistant to all known practical attacks. Avoid older, legacy encryption options if possible.
The Power of Password Managers
The single best defense is a long, complex, and unique password. Humans are terrible at creating and remembering these. A password manager solves this problem by generating and securely storing these passwords for you. Instead of needing to remember 'MyD0gSp0t!2024', you only need to remember one strong master password. This effectively neutralizes dictionary and common brute-force attacks.
Recovery vs. Cracking: A Technical Comparison
| Aspect | Password Recovery (Authorized) | Password Cracking (Unauthorized) |
|---|---|---|
| Intent | Regain access for the legitimate owner. | Gain access for a malicious actor. |
| Methodology | Uses hints, personal data, and identity verification. | Uses brute-force, dictionary attacks, and exploits. |
| Information Used | Owner-provided information (e.g., old passwords, pet names). | Public wordlists, leaked password databases, algorithms. |
| Typical Scenario | An employee forgetting the password to an encrypted report. | An attacker trying to steal data from a protected file. |
| Primary Tools | Password managers, account recovery options, user-guided tools. | Specialized software like Hashcat or John the Ripper. |