
With the explosion of digital collaboration, password-protecting sensitive documents has become standard practice. But what happens when that crucial password is forgotten, or an employee leaves without sharing it? This scenario, once a minor annoyance, is now a significant business continuity risk, fueling rapid innovation in recovery tools.
The days of simple brute-force attacks running on a single machine are fading. We're now seeing a sophisticated ecosystem emerge, driven by powerful hardware, intelligent algorithms, and cloud infrastructure. Understanding these shifts is crucial for any organization that relies on encrypted data.
Table of Contents
The Shifting Landscape of Document Security
The need for robust recovery tools is directly tied to the evolution of document security itself. Encryption standards have become significantly more complex, moving beyond simple password protection to include multi-layered security protocols that are much harder to circumvent.
From Simple Passwords to Complex Encryption
Early document protection was straightforward. Today, we deal with AES-256 encryption, digital signatures, and permission-based access controls within a single file. This complexity makes legacy recovery methods obsolete and demands more advanced solutions that can intelligently analyze and attack these modern encryption schemes. The file password recovery trends point towards tools that understand these nuances.
The Rise of Remote Work and Data Sprawl
The shift to remote and hybrid work models has scattered sensitive data across countless personal devices and cloud services. This decentralization increases the instances of lost access, as files are managed outside of a controlled corporate IT environment. Consequently, the demand for reliable, accessible recovery solutions has skyrocketed, contributing to significant data recovery software growth.
Key Technological Drivers in Password Recovery
Technology is at the heart of the evolution in this space. Several key advancements are making password recovery faster, more efficient, and more successful than ever before. As a developer, I've seen firsthand how these technologies have changed the game.
AI and Machine Learning Integration
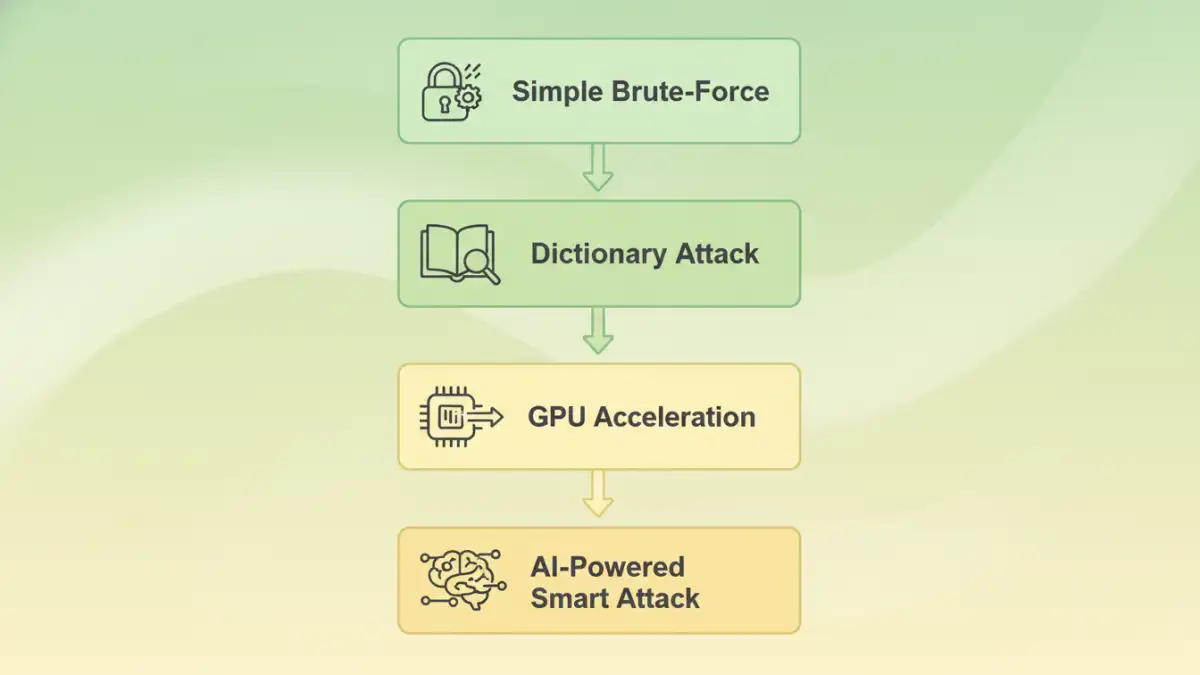
Artificial intelligence is no longer just a buzzword here. Modern tools use machine learning to perform smart attacks, analyzing password patterns, learning from previous recovery attempts, and prioritizing likely character combinations. Instead of trying 'aaaa' then 'aaab', an AI-powered tool might prioritize common words, dates, or substitutions like '@' for 'a', dramatically reducing recovery time.
GPU Acceleration and Cloud Computing
Password cracking is a numbers game, and raw processing power matters. Modern tools now leverage the parallel processing power of Graphics Processing Units (GPUs) to try billions of combinations per second. Furthermore, cloud-based platforms can distribute this workload across thousands of machines, making it possible to crack even very complex passwords in a fraction of the time it would take on a single desktop.
Emerging Business Models and Market Players
The way these tools are sold and delivered is also changing. The market is maturing, moving away from niche, single-purchase software to more flexible and scalable service-based offerings that cater to both individual and enterprise needs.
Subscription Services vs. One-Time Purchases
While you can still buy standalone desktop software, the trend is moving towards Software-as-a-Service (SaaS) models. These subscription-based services offer continuous updates, access to powerful cloud-processing infrastructure, and dedicated support. This model is particularly attractive for businesses that need ongoing recovery capabilities without a massive upfront investment in hardware.
The Growing PDF Unlocker Market Analysis
PDFs remain one of the most common formats for secure document exchange, and the specialized PDF unlocker market is a significant segment. Companies are focusing on user-friendly online tools that offer quick, drag-and-drop solutions for removing restrictions or recovering passwords, often on a pay-per-use basis. This accessibility has broadened the user base beyond just IT professionals.
Ethical Considerations and Future Outlook
The power of modern encryption bypass tools brings up important ethical questions. The same technology used to recover a lost password for a legitimate business document can also be used for malicious purposes. Reputable vendors in the document password recovery market navigate this by focusing their services on users who can prove ownership of the file.
Looking ahead, I expect to see even tighter integration of AI, with tools capable of predicting password structures based on user or company profiles. We'll also likely see a rise in blockchain-based solutions for secure key management, potentially reducing the need for password recovery altogether by creating decentralized, recoverable access methods. The industry will continue to walk the fine line between providing essential recovery services and preventing misuse.
Recovery Technology Comparison
| Technology | Core Principle | Pros | Cons |
|---|---|---|---|
| Brute-Force Attack | Tries every possible character combination. | Guaranteed to work eventually. | Extremely slow for complex passwords. |
| Dictionary Attack | Uses a list of common words and phrases. | Much faster than brute-force for common passwords. | Ineffective against random, non-dictionary passwords. |
| GPU Acceleration | Uses graphics cards for parallel processing. | Massively speeds up brute-force and dictionary attacks. | Requires specialized hardware or cloud services. |
| AI-Powered Analysis | Uses machine learning to predict password patterns. | Intelligently prioritizes likely combinations, saving time. | Effectiveness depends on the quality of the algorithm. |