
With the explosion of digital data and the rise of sophisticated cyber threats, securing sensitive information has shifted from a best practice to a critical business necessity. Every organization, from a small law firm to a multinational corporation, handles documents that require protection—contracts, financial records, intellectual property, and personal data. This has created a significant and expanding demand for robust security solutions.
Understanding the forces behind this expansion is key for any professional involved in IT, security, or business strategy. It's not just about locking a file; it's about deploying a comprehensive strategy that aligns with regulatory demands, supports modern workflows like remote collaboration, and stays ahead of emerging threats.
Table of Contents
Key Market Growth Drivers
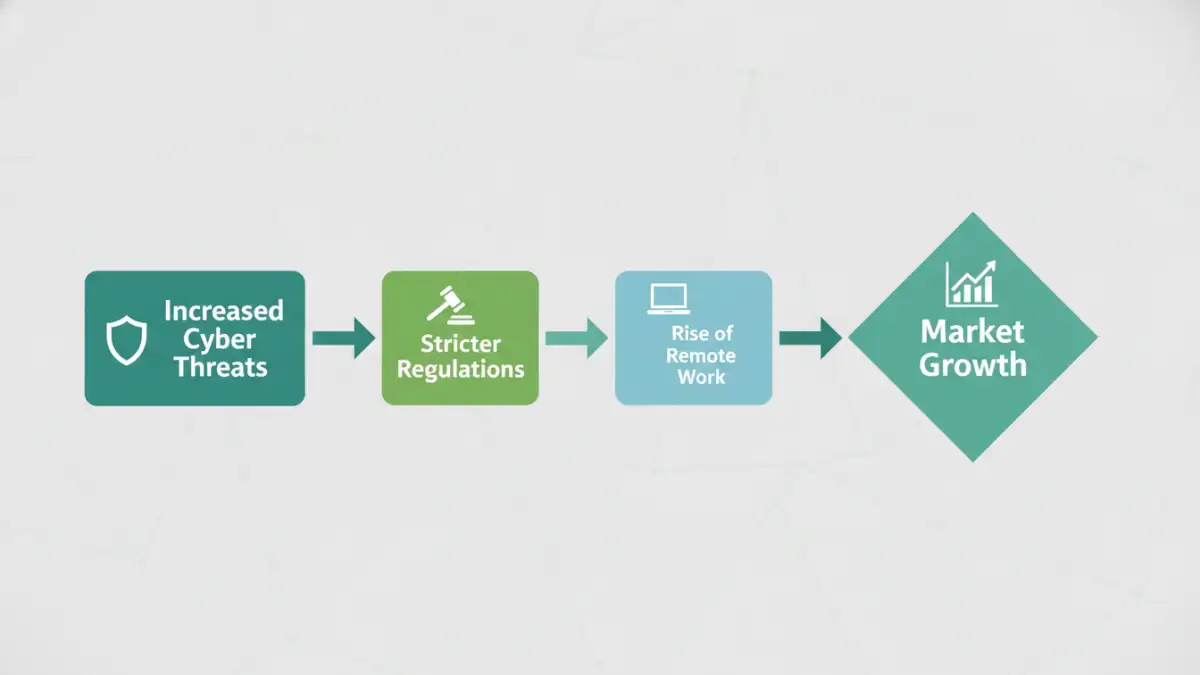
Several powerful forces are fueling the expansion of the document encryption software market. The primary catalyst is the increasing frequency and sophistication of data breaches. A single leaked document can lead to devastating financial loss, reputational damage, and legal consequences, making proactive encryption a non-negotiable layer of defense.
Regulatory Compliance and Data Privacy Laws
Another major driver is the stringent regulatory landscape. Laws like GDPR in Europe, CCPA in California, and HIPAA in the healthcare sector mandate the protection of personal and sensitive data. Non-compliance can result in massive fines. Encryption is one of the most effective technical safeguards to meet these requirements, as encrypted data, even if stolen, remains unreadable and unusable to unauthorized parties.
These regulations effectively create a baseline security standard that organizations must meet. As a software engineer, I've seen firsthand how projects are re-scoped to include encryption-at-rest and in-transit specifically to satisfy these legal obligations. It's no longer an optional feature but a core requirement for any system handling user data.
Emerging Technology and Secure Document Sharing Trends

The technology within the encryption space is also evolving rapidly. Modern solutions are moving beyond simple password protection to incorporate more advanced and user-friendly methods. This includes leveraging public key infrastructure (PKI), multi-factor authentication (MFA) for access, and granular permission controls that dictate who can view, edit, or print a document.
One of the most significant secure document sharing trends is the focus on seamless user experience. Early encryption tools were often clunky and disruptive to workflows. Today's solutions aim for transparency, integrating directly into email clients, cloud storage platforms, and collaboration tools. The goal is to make security an invisible part of the process, not a hurdle for employees to overcome.
The Rise of Cloud-Native and AI-Powered Solutions
The shift to cloud computing has fundamentally changed how documents are stored and shared. Consequently, cloud-native encryption solutions are gaining traction. These tools provide persistent encryption that protects data whether it's stored in Dropbox, Google Drive, or a private cloud. They also offer centralized management and auditing capabilities, which are crucial for maintaining oversight in a distributed environment. Furthermore, AI and machine learning are beginning to play a role in identifying sensitive data automatically and applying appropriate encryption policies, reducing the risk of human error.
Competitive Landscape and Market Segmentation
The market for document encryption is diverse, featuring a mix of established cybersecurity giants and innovative startups. We can broadly segment vendors into a few categories. First, there are the platform players like Microsoft and Google, who build encryption features directly into their operating systems and productivity suites (e.g., BitLocker, Microsoft Purview Information Protection). These offer convenience and deep integration.
Second, we have standalone encryption specialists who offer best-of-breed solutions. These companies often provide more advanced features, cross-platform support, and higher levels of customization. Finally, there are vendors who embed encryption within broader solutions like Data Loss Prevention (DLP) or Enterprise Content Management (ECM) systems. The choice of vendor often depends on an organization's existing tech stack, security needs, and budget.
Future Projections and Industry Challenges
Looking ahead, the data encryption market size is projected to continue its strong growth trajectory. The proliferation of IoT devices and the continued expansion of remote work will generate even more data that needs protection. We can expect to see more sophisticated solutions that utilize quantum-resistant cryptography and advanced key management systems.
However, the industry faces challenges. Integration complexity remains a significant hurdle, as encryption tools must work flawlessly with a wide array of applications and systems. User adoption is another concern; if a solution is too difficult to use, employees may seek workarounds that bypass security controls. Balancing robust security with usability will continue to be the central challenge for software developers and vendors in this space.
Comparison of Document Encryption Solution Types
| Solution Type | Key Features | Best For | Potential Drawbacks |
|---|---|---|---|
| On-Premise Software | Full control over data and keys, offline access, one-time purchase model. | Organizations with strict data sovereignty requirements or limited internet access. | Higher upfront cost, requires dedicated IT staff for maintenance and updates. |
| Cloud-Based (SaaS) | Scalable, accessible from anywhere, automatic updates, subscription-based pricing. | Businesses of all sizes, especially those with remote teams and a cloud-first strategy. | Reliance on vendor for security and uptime, potential data privacy concerns. |
| Integrated Platform Features | Seamless integration with existing ecosystems (e.g., Microsoft 365), simplified user experience. | Companies heavily invested in a specific vendor's platform. | May lack advanced features of specialized tools, risk of vendor lock-in. |
| Open-Source Tools | Free to use, customizable, transparent and auditable code. | Technically proficient users, developers, and organizations with tight budgets. | No official support, requires in-house expertise to implement and maintain. |