
The shift from CMMC 1.0 to 2.0 has simplified some aspects of compliance but sharpened the focus on others, particularly data protection. For any organization in the Defense Industrial Base (DIB), understanding how to handle Controlled Unclassified Information (CUI) is no longer optional; it's a fundamental requirement. At the heart of this is encryption, the primary technical safeguard for protecting data wherever it lives.
From my perspective working on secure systems, the core challenge isn't just flipping an 'encrypt' switch. It's about implementing a cohesive strategy that aligns with specific government standards. Let's break down what CMMC 2.0 actually requires for your data and how you can implement effective document encryption to meet these mandates.
Table of Contents
CMMC 2.0: A Refresher on What Matters
The Cybersecurity Maturity Model Certification (CMMC) framework was created by the Department of Defense (DoD) to protect the defense supply chain from cyber threats. CMMC 2.0 streamlined the original model into three levels, with Level 2 being the most common target for contractors handling CUI.
This level aligns directly with the security controls outlined in NIST SP 800-171. This alignment is critical because it gives us a clear, established playbook for implementation. Instead of navigating a brand-new set of rules, we can lean on well-understood NIST standards that have been the bedrock of federal information security for years.
The Central Role of CUI Protection
Controlled Unclassified Information (CUI) is the focal point of CMMC. This is information that isn't classified but is still considered sensitive and requires safeguarding. Examples include technical drawings, project plans, and certain types of research data. Your primary mission under CMMC is to demonstrate that you have the controls in place to protect CUI from unauthorized disclosure.
Encryption is a non-negotiable part of that demonstration. If CUI is compromised, it can give adversaries insights into U.S. military capabilities and technology. That's why the DoD mandates its protection so rigorously through frameworks like CMMC.
Core Encryption Requirements Under CMMC 2.0

For contractors aiming for Level 2 compliance, the encryption requirements are derived directly from NIST SP 800-171. The framework doesn't just say "encrypt your data"; it specifies the *type* of encryption required. This is where many organizations can misstep.
The key requirement is the use of FIPS 140-2 validated cryptographic modules. FIPS (Federal Information Processing Standards) are issued by NIST. A FIPS 140-2 validation means the encryption algorithm and its implementation have been rigorously tested and approved for use in protecting government data. Using a commercial encryption tool that isn't FIPS-validated simply won't meet the compliance standard.
Adhering to NIST Standards
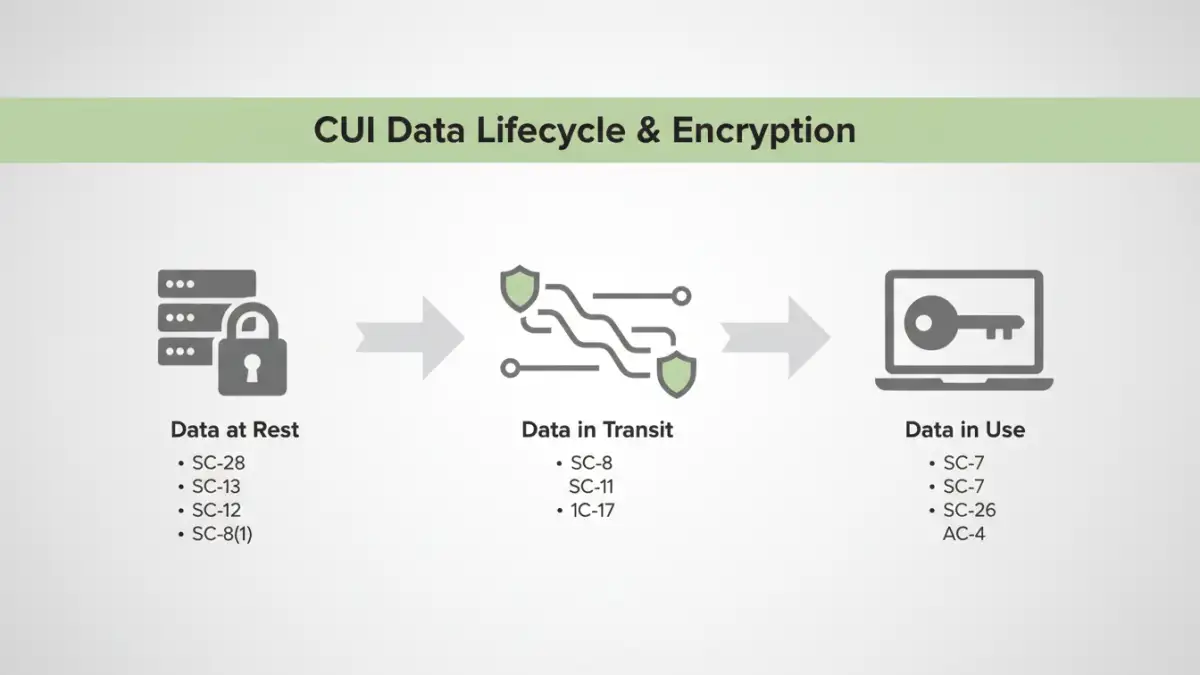
Two key areas where NIST SP 800-171 mandates encryption are for data at rest and data in transit. This comprehensive approach ensures CUI is protected whether it's sitting on a server, a laptop, or being sent over a network.
- Data at Rest: This refers to CUI stored on any media, such as hard drives, servers, or removable drives. Full-disk encryption (like BitLocker or FileVault) is a foundational control here.
- Data in Transit: This covers CUI being transmitted over networks. This is typically handled by protocols like TLS for web traffic, SSH for remote access, and secure VPNs for network connections.
Practical Implementation of Document Encryption
Meeting compliance isn't just about having the right technology; it's about process and policy. A robust cmmc document encryption strategy involves identifying where CUI exists and applying the correct controls systematically.
First, you need to perform a data discovery exercise. You can't protect what you don't know you have. Use tools and manual processes to identify and tag all CUI within your environment. Once identified, you can apply policies to ensure it's always stored in an encrypted state. This involves more than just turning on disk encryption; it means ensuring your collaboration platforms, email systems, and file-sharing solutions enforce these rules.
Beyond Basic Encryption: Secure File Handling
Effective CUI protection goes beyond the algorithm. It includes access controls, key management, and audit logs. Who has the keys to decrypt the data? How are those keys stored and managed? Can you track who accessed a sensitive file and when?
This is where solutions like Data Loss Prevention (DLP) and Information Rights Management (IRM) come into play. These tools can enforce policies automatically, such as preventing CUI from being emailed to an external address or copied to a USB drive. They provide the granular control and audibility needed for true defense contractor security.
Choosing the Right Tools for Compliance
When selecting tools, the first question should always be: "Is it FIPS 140-2 validated?" Many mainstream cloud providers, like Microsoft 365 GCC High and AWS GovCloud, offer services that meet this standard. These platforms are often a good starting point for DIB contractors because they have built-in capabilities for CUI protection.
For endpoint protection, enterprise-grade antivirus and endpoint detection and response (EDR) solutions often include FIPS-validated encryption modules. The goal is to build a layered defense where encryption is one part of a broader security architecture that includes robust access control, continuous monitoring, and incident response planning.
CMMC 2.0 Encryption Solution Comparison
| Encryption Type | Primary Use Case | NIST Control Alignment | Implementation Complexity |
|---|---|---|---|
| Full-Disk Encryption (FDE) | Protecting data at rest on laptops and servers. | 3.13.11, 3.13.16 | Low (Often built into OS) |
| File/Folder Level Encryption | Securing specific documents or project folders. | 3.1.13, 3.13.11 | Medium |
| Email Encryption (S/MIME, PGP) | Protecting CUI in transit via email. | 3.13.11, 3.13.15 | Medium to High |
| Transport Layer Security (TLS) | Securing data in transit over networks (e.g., web traffic). | 3.13.8, 3.13.11 | Low (Handled by servers/clients) |
| Database Encryption (TDE) | Encrypting entire databases at rest. | 3.13.11, 3.13.16 | High |