Unlocking a phone or laptop with a fingerprint feels like something from a spy movie—fast, personal, and seemingly foolproof. This convenience has naturally extended to securing sensitive documents. But have you ever paused to ask, 'Is this really secure?' While biometrics eliminate the problem of forgotten passwords, they introduce a completely different set of challenges that aren't as simple as just resetting a password.
Table of Contents
The Promise and Pitfalls of Biometrics

The appeal of biometric security is undeniable. It's based on 'something you are'—a fingerprint, your face, your voice—rather than 'something you know,' like a password. This eliminates password fatigue, phishing attacks that steal credentials, and the need for complex password management. For document access, it promises a seamless and quick way to get to your data without typing a single character.
How Biometric Authentication Works
When you first register your biometric data, the system doesn't store an actual image of your fingerprint or face. Instead, it creates a digital template by mapping unique points and converting them into a mathematical representation. During authentication, the sensor captures your biometric data again, converts it to a template, and compares it to the stored version. A close enough match grants access. This process is incredibly fast, but the magic happens in that 'close enough' comparison.
Convenience at a Cost?
The primary trade-off is between security and convenience. A system that is too strict might fail to recognize the legitimate user due to a small cut on their finger or poor lighting for a facial scan. A system that is too lenient becomes vulnerable to spoofing. Finding that perfect balance is a constant engineering challenge, and it's where many potential security flaws originate.
Common Document Security Vulnerabilities in Biometrics
While biometrics are strong, they are not infallible. The attack vectors are just different from traditional password-based systems. Understanding these weaknesses is the first step toward building a more robust security posture for your sensitive files. These are the core biometric document security risks that I've seen exploited in various proof-of-concept attacks and real-world scenarios.
Presentation Attacks (Spoofing)
This is the most well-known form of biometric hacking. It involves presenting a fake biometric artifact to the sensor. High-resolution photos can fool some facial recognition systems, and detailed fingerprint molds made from latent prints (left on a glass, for example) can trick certain scanners. Modern systems have 'liveness detection' to counter this, checking for things like blinking or blood flow, but determined attackers are constantly finding ways to bypass these measures.
Database Breaches: The Irreversible Compromise
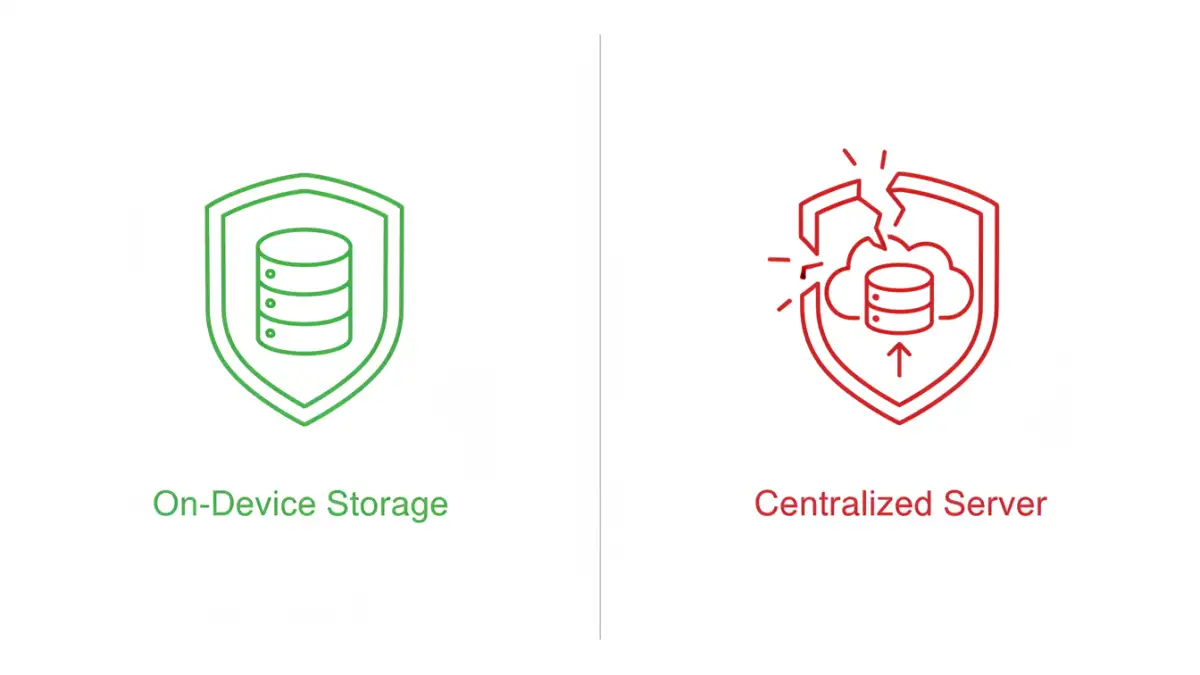
This is, in my opinion, the most significant risk. If a hacker steals your password, you can change it. If they steal the biometric template of your fingerprint, you can't get a new finger. A breach of a database containing biometric templates is a permanent compromise. While these templates are typically encrypted, a sophisticated breach could expose data that uniquely identifies you forever, creating massive risks for identity theft.
Real-World Biometric Hacking Examples
These aren't just theoretical problems. Researchers and security professionals have demonstrated these vulnerabilities time and again. These examples show that we can't afford to be complacent about biometric security.
The 'Gummy Bear' Hack
A famous early example involved Japanese researchers lifting a latent fingerprint from a glass surface, creating a mold, and then using a gelatin-based substance (like a gummy bear) to create a replica that successfully fooled many fingerprint sensors. This highlighted how easily our biometric data can be unintentionally left behind and copied.
AI and Deepfake Threats
The rise of artificial intelligence presents new threats. AI can be used to generate realistic deepfake images or videos to fool facial recognition systems. Similarly, voice cloning technology can replicate a person's voice with just a few seconds of audio, potentially bypassing voice authentication systems used to access secure documents or accounts.
Strategies for Securing Biometric Access
So, is biometric safe for files? The answer is nuanced. It can be, provided it's implemented correctly and supplemented with other security layers. It's not about abandoning the technology but about using it wisely.
Embrace Multi-Factor Authentication (MFA)
The single most effective way to secure biometric access is to not rely on it alone. Combine 'something you are' (biometrics) with 'something you know' (a password or PIN) or 'something you have' (a security key or phone authenticator app). Requiring a fingerprint and a PIN to access a highly sensitive document folder provides exponentially more security than either method alone.
Evaluate the System
Not all biometric systems are created equal. When choosing a device or software, look for features like advanced liveness detection and on-device storage of biometric templates (as opposed to cloud storage). Keeping your data local to your device significantly reduces the risk of a large-scale database breach. Always keep your device's software updated to get the latest security patches.
Biometric Vulnerability Comparison
| Biometric Type | Common Vulnerability | Mitigation Strategy | Best Use Case |
|---|---|---|---|
| Fingerprint | Spoofing with molds or lifted prints | Use sensors with liveness detection (e.g., capacitive or ultrasonic) | Device unlocking, app access |
| Facial Recognition | Spoofing with high-res photos or deepfakes | Systems with 3D depth sensing and liveness checks (e.g., blinking) | Hands-free authentication |
| Voice Recognition | Replay attacks with recordings or AI-cloned voice | Require randomized phrases; analyze vocal tract characteristics | Phone-based support, accessibility |
| Iris/Retina Scan | Difficult to spoof but possible with high-res images | Infrared light to check for blood flow and unique vein patterns | High-security physical access control |