
A few years ago, I was part of a team migrating a healthcare provider's entire document management system. The biggest hurdle wasn't the data transfer; it was ensuring every single patient record met strict HIPAA access control requirements. The existing password-based system was a constant headache of forgotten credentials, shared accounts, and a weak audit trail. It became clear that to truly secure the data and prove it, we needed to verify the person, not just the password.
This is where the conversation shifted to biometrics. Instead of relying on something a user knows, we started focusing on something a user *is*. This fundamental change is not just about convenience; it's about building a foundation of trust and irrefutable proof, which is the cornerstone of modern data regulation.
Table of Contents
The Failure of Traditional Security in Compliance
For decades, the password has been the gatekeeper of digital information. While simple to implement, its weaknesses are profound, especially when viewed through the lens of regulatory compliance. Passwords can be stolen, shared, written on sticky notes, or cracked through brute-force attacks. From a compliance standpoint, this creates a massive accountability gap.
When an auditor asks, "Who accessed this sensitive file on May 15th at 2:00 PM?", a system log showing 'user_jdoe' isn't enough. How can you prove it was actually Jane Doe and not a colleague using her credentials? You can't, and that ambiguity is a significant compliance risk for regulations that demand strict access controls.
The Audit Trail Problem
Regulations like HIPAA and GDPR require organizations to maintain detailed, accurate audit trails of who accesses protected data. A log tied to a shareable credential is inherently weak. This makes it difficult to investigate data breaches, enforce accountability, and demonstrate due diligence to regulators, potentially leading to heavy fines and reputational damage.
How Biometrics Provide a Solution

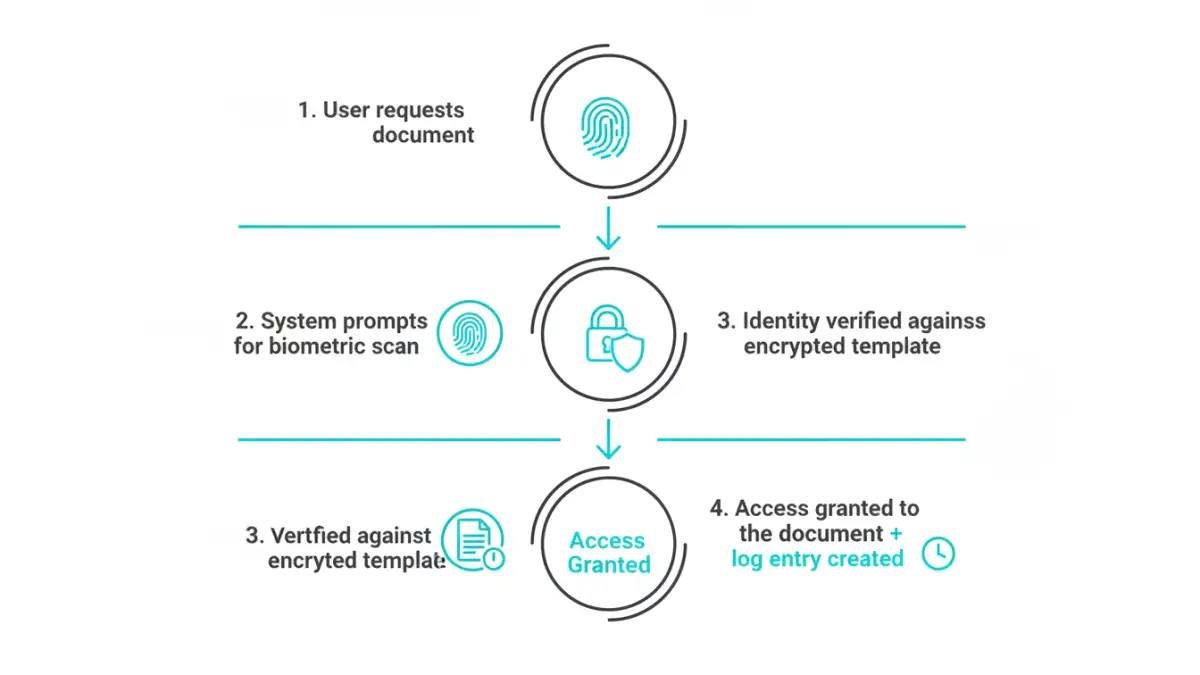
Biometric authentication uses unique physiological or behavioral characteristics—like a fingerprint, face, or iris—to verify a person's identity. Unlike a password, these identifiers cannot be easily shared, forgotten, or stolen. This introduces a critical concept into security: non-repudiation.
Non-repudiation is the assurance that someone cannot deny the authenticity of their signature on a document or the fact that they performed an action. When access to a sensitive file is gated by a fingerprint scan, the system log now has irrefutable proof that a specific individual was physically present and authorized the access. This transforms a weak audit trail into a powerful compliance tool.
Strengthening Identity Assurance
For compliance, identity assurance is everything. Biometrics provide a much higher level of assurance than traditional methods. By tying data access to a unique biological trait, organizations can confidently prove that only authorized individuals are viewing, editing, or sharing regulated documents. This is a fundamental step toward achieving robust biometric document compliance.
Biometric Technologies in Document Workflows
Implementing biometrics isn't a one-size-fits-all approach. Different technologies are suited for different environments and levels of security. My work has involved integrating several of these into various systems.
- Fingerprint Scanning: This is the most common and cost-effective method. It's ideal for logging into workstations, unlocking mobile devices to access files, or authorizing document approvals within an application.
- Facial Recognition: Growing rapidly in popularity, this offers a frictionless user experience. It's excellent for securing access to cloud-based document portals or for continuous authentication, ensuring the authorized person is still the one viewing the screen.
- Iris Scanning: Offering extremely high accuracy, iris scanning is often reserved for high-security environments. Think government agencies or R&D departments where access to classified or proprietary documents must be ironclad.
- Voice Recognition: Useful for remote or hands-free scenarios, like a doctor dictating notes into a secure system. The system verifies the voiceprint before allowing the record to be saved.
Real-World Compliance Scenarios
The true value of biometrics becomes clear when applied to specific regulatory frameworks. It moves from a theoretical benefit to a practical solution for everyday compliance challenges.
For example, achieving hipaa compliant document security requires stringent controls on Protected Health Information (ePHI). A nurse accessing a patient's chart on a shared hospital workstation can use their fingerprint to log in. This creates a specific, auditable event tied directly to that individual, preventing unauthorized access and ensuring accountability.
Similarly, gdpr file protection mandates that access to EU citizens' personal data be tightly controlled. A company can use facial recognition to grant remote employees access to a customer database. This helps fulfill GDPR's principle of 'integrity and confidentiality' by ensuring that only verified employees can view sensitive personal information, no matter where they are working.
Addressing Privacy and Implementation Challenges
Of course, using biometrics introduces its own set of responsibilities. The very data used for authentication is sensitive and must be protected. This is a common concern and one we had to address carefully in my projects. The key is to never store raw biometric images.
Instead, modern systems convert the biometric input (like a fingerprint scan) into an encrypted mathematical representation, or template. This template cannot be reverse-engineered to recreate the original fingerprint. Often, this data is stored in a secure enclave on the device itself, so it never leaves the user's control. Addressing biometric data privacy is not just good practice; it's a requirement for earning user trust and meeting compliance standards.
Biometric Authentication Methods Comparison
| Method | Accuracy | Implementation Cost | User Acceptance |
|---|---|---|---|
| Fingerprint Scan | High | Low to Medium | Very High |
| Facial Recognition | High | Low to High (depends on hardware) | High |
| Iris Scan | Very High | High | Medium |
| Voice Recognition | Medium to High | Low | Medium to High |