
When you've put time and effort into securing a sensitive document with PDF encryption, the next step often involves sharing it. However, the process of distributing these protected files isn't always straightforward. Understanding the legal landscape and the permissions involved is crucial to avoid inadvertent data breaches or legal complications. It's a common point of confusion, even for experienced professionals.
Over my years working with data security and software development, I've encountered numerous scenarios where the sharing of encrypted documents raised questions. Whether it's a legal contract, financial report, or proprietary information, ensuring it reaches the intended recipients without unauthorized access is paramount. This involves more than just applying a password; it requires a clear understanding of rights, responsibilities, and the technical methods available.
Table of Contents
Understanding PDF Encryption and Permissions
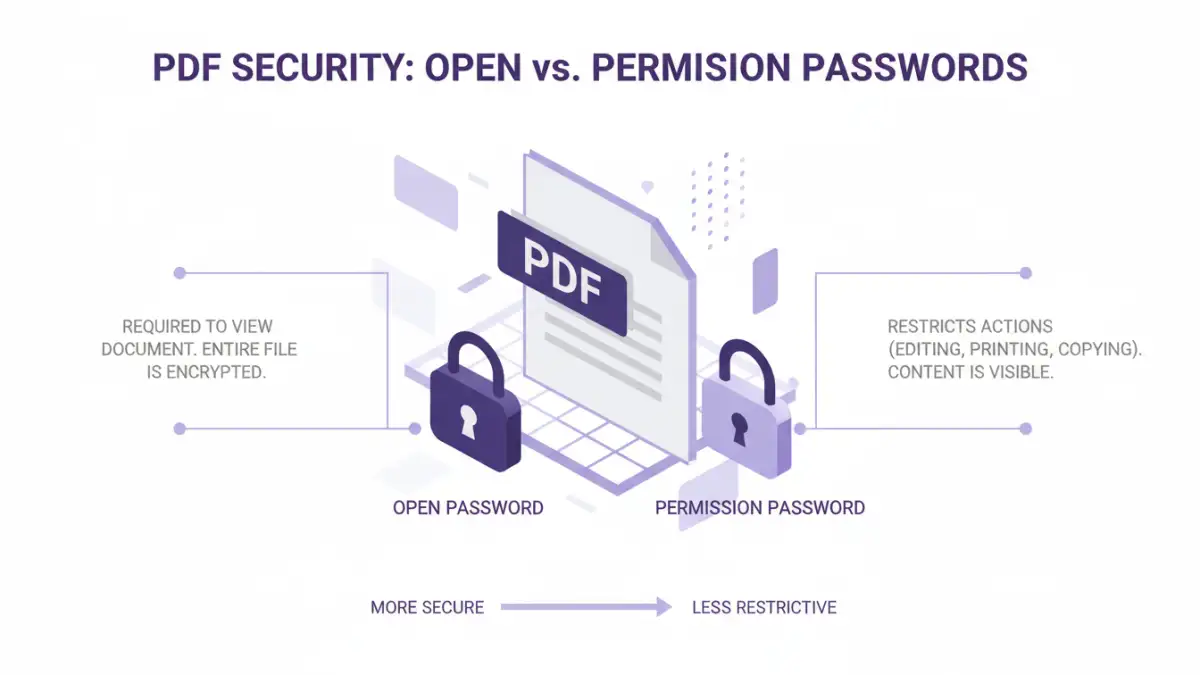
PDF encryption typically involves two layers of security: document open passwords and permission passwords. The open password prevents anyone from opening the PDF at all. The permission password, on the other hand, allows access to the document but restricts specific actions like printing, copying text, or editing.
Distinguishing Open vs. Permission Passwords
When you encrypt a PDF, you can set an open password that is essential to even view the file. Alternatively, or additionally, you can set a permission password. This second layer controls what users can do once they have opened the document. Understanding this distinction is key, as it directly impacts how you manage sharing and what permissions you grant.
The Legal Framework for Sharing

The legal aspects of sharing encrypted PDFs hinge on data privacy laws, intellectual property rights, and contractual agreements. In many jurisdictions, laws like GDPR or CCPA mandate that personal or sensitive data must be protected from unauthorized access. Sharing an encrypted PDF is a method of protection, but the act of sharing itself needs careful consideration.
When you share a password-protected file, you are implicitly granting certain rights to the recipient. The crucial question is, what are those rights? This depends entirely on the type of password used and the specific terms you've communicated. If you've only used an open password, the recipient can do anything with the file once opened. If you've used a permission password, you've explicitly defined what they can and cannot do.
Methods for Sharing Encrypted PDFs
The method you choose for sharing encrypted PDFs can significantly impact the security and convenience. Simply emailing a password-protected PDF and the password in a separate email is a common, though not always the most secure, practice. This approach requires careful coordination to ensure the password reaches the recipient securely.
Other methods involve using secure file-sharing platforms that offer end-to-end encryption, or utilizing features within PDF software that allow for controlled sharing. For instance, some tools allow you to set expiration dates for access or track who has downloaded the file. These advanced features can enhance control over your encrypted files, especially when dealing with sensitive information where precise sharing encrypted pdf permissions are vital.
Secure Communication Channels
It's essential to use secure channels for transmitting both the encrypted file and its password. Sending the password via a different method than the file itself (e.g., a phone call, a secure messaging app, or a different email thread) adds a layer of security. This minimizes the risk if one channel is compromised.
Best Practices for Secure Distribution
Beyond the technical aspects of encryption, establishing clear protocols for sharing is vital. This includes defining who is authorized to receive the document and what actions they are permitted to take. Documenting these permissions, even internally, can be beneficial for accountability.
Always use strong, unique passwords for your encrypted PDFs. Regularly review who has access to sensitive documents and revoke access when it's no longer needed. For critical information, consider using encryption solutions that offer advanced access control and auditing features. This proactive approach helps maintain the integrity of your data and ensures compliance with any relevant regulations.
Comparison Table: PDF Encryption and Sharing Methods
| Method | Pros | Cons | Best For |
|---|---|---|---|
| Open Password Only | Simple to implement, broadly compatible | No control over recipient actions (printing, copying) | General document protection, non-critical data |
| Permission Password | Restricts specific actions (print, copy, edit) | Recipient needs to know both passwords to bypass restrictions; some software can break these | Controlling how a document is used post-sharing |
| Secure File Sharing Platforms | End-to-end encryption, access controls, audit trails | Often requires subscription, recipient may need an account | High-security documents, business-to-business sharing |
| Encrypted Email Attachments (with separate password delivery) | Utilizes existing infrastructure, user familiarity | Password transmission security is critical; can be cumbersome | Ad-hoc secure sharing of moderately sensitive files |