
Accessing your own important documents can sometimes become a hurdle, especially when they are protected by a password you've forgotten or are trying to access on behalf of an estate. This situation often leads to questions about legal rights and ethical considerations surrounding locked document access. It's a common scenario, and understanding the framework around it is crucial.
While the technical aspects of password recovery can be complex, the legal side involves a different set of rules. These rules are designed to balance the right to privacy and data security with the need for legitimate access in specific circumstances. My experience has shown that clarity on these rights can prevent significant frustration and legal complications.
Table of Contents
Understanding Ownership and Access
The fundamental principle governing access to password-protected files is ownership. If you own the file and have a legitimate reason to access it, your rights are generally stronger. This includes personal files, business documents you created, or files you have explicit permission to access.
Your Rights as an Owner
As the rightful owner of a password-protected file, you inherently have the right to access its contents. The password is a security measure you implemented. If you've forgotten it, your primary recourse is through legitimate recovery methods or by proving ownership to a service provider if applicable. The ability to recover password protected files for yourself is a core aspect of data ownership.
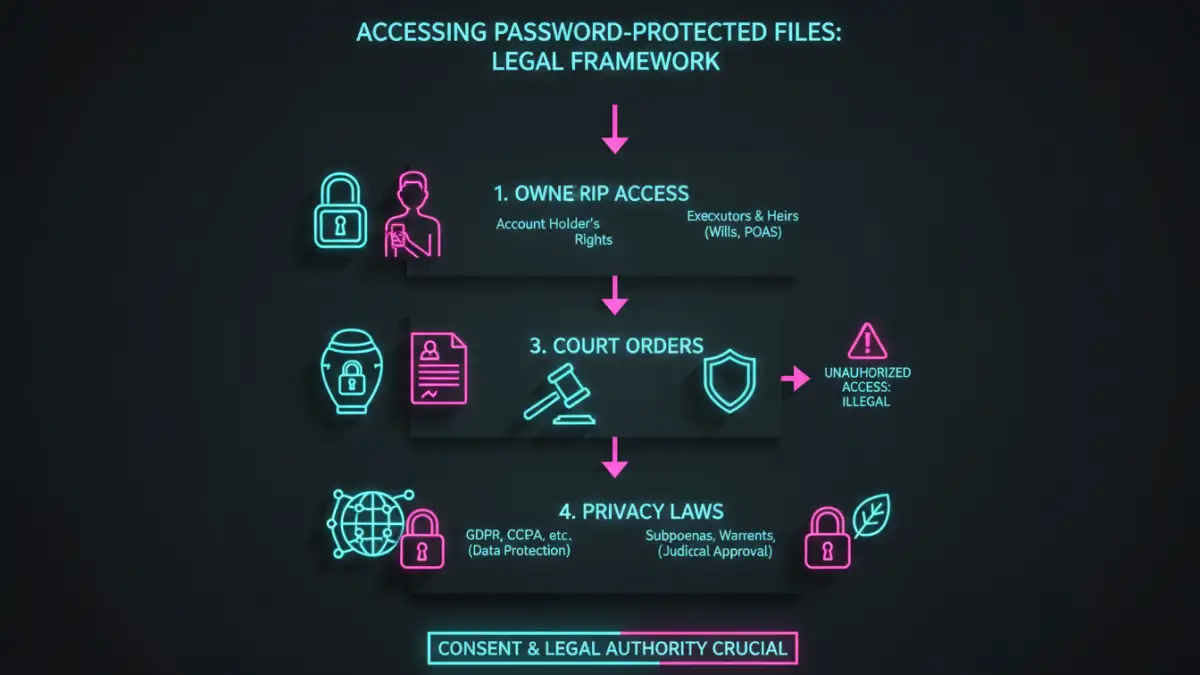
The Legal Framework
Several legal concepts underpin the right to access digital information. These often intersect with data privacy laws, intellectual property rights, and estate law. Understanding these can clarify what is permissible when dealing with locked files.
Data Privacy and Security Laws
Laws like GDPR (General Data Protection Regulation) or CCPA (California Consumer Privacy Act) emphasize data subject rights, including the right to access one's own data. While these laws primarily focus on how organizations handle data, they reflect a broader societal principle of data access for rightful owners. These regulations highlight the importance of secure data handling but also the rights individuals have regarding their information.
Estate and Succession Laws
When a person passes away, their digital assets, including password-protected files, become part of their estate. Estate and succession laws typically grant executors or administrators the legal authority to access and manage the deceased's assets. This often requires obtaining a court order or presenting specific documentation to prove their authority to access locked document access.
Ethical Considerations
Beyond legal rights, there are significant ethical considerations. Attempting to recover files you do not own or have explicit permission to access can lead to legal trouble and ethical breaches. Respecting digital privacy is paramount, even when dealing with files that may seem accessible.
Respecting Privacy
Even if you have a technical means to recover a password, it's crucial to consider the privacy implications. Accessing someone else's private files without consent is a violation of their privacy and can have severe legal consequences, regardless of whether the files are password protected.
Data Integrity
When attempting to recover password protected files, it's also important to ensure you do not compromise the integrity of the data. Using unauthorized or forceful methods could corrupt the file, making it permanently inaccessible. Always opt for methods that preserve the data.
Practical Steps for Legitimate Access
If you are the rightful owner and have forgotten a password, or are an authorized representative of an estate, there are legitimate paths to attempt recovery.
Self-Recovery Methods
For files you own, start with simple methods: try common passwords you use, check for password hints, or use password recovery features built into the software. Many applications offer 'forgot password' links that send recovery instructions to your registered email.
Using Third-Party Tools (with Caution)
There are software tools designed to help recover forgotten passwords for various file types. However, their use is generally intended for files you own. Using these tools on files you don't own can be illegal and unethical. Always ensure you have the legal right to attempt recovery before using such software.
Legal Avenues for Estate Access
If you are an executor or administrator, you will likely need to present proof of your authority (e.g., a will, court appointment) to the service provider or software vendor. Some may offer specific procedures for estate access, while others might require a court order to compel access.
Limitations and When You Can't Recover
It's important to acknowledge that not all password-protected files are recoverable, even with legal rights. Strong encryption and robust security measures can make recovery technically impossible for many users.
Technical Impossibility
Some encryption methods are designed to be virtually unbreakable without the correct password or key. Brute-force attacks, while technically possible, can take an astronomical amount of time and computational power for strong encryption, rendering them impractical for most users.
Legal Restrictions
Even with ownership, certain files might be legally protected from disclosure. For example, attorney-client privileged documents or medical records may have specific legal protections that supersede even an owner's immediate right to access, requiring strict legal processes.
Comparison Table: Methods for Accessing Password Protected Files
| Method | Legality/Ethics | Effectiveness | Best For |
|---|---|---|---|
| Owner Self-Recovery (e.g., forgot password) | High (if you own the file) | Varies (depends on software/encryption) | Personal files, forgotten passwords |
| Third-Party Recovery Tools | High (if you own the file), Low (if you don't) | Varies (can be effective for some types) | Recovering your own forgotten passwords |
| Estate Executor/Admin Access | High (with proper legal authority) | Depends on provider/court order | Accessing deceased's digital assets |
| Legal Compulsion (Court Order) | High (when legally mandated) | Can be effective, but complex process | Resolving disputes, legal investigations |
| Unauthorized Access/Hacking | Extremely Low (Illegal and unethical) | Can be effective, but carries severe penalties | No legitimate use case |