
Sharing sensitive information requires robust security measures. Whether it's a groundbreaking invention, a proprietary algorithm, or confidential business strategies, ensuring that your intellectual property (IP) remains confidential during transit and storage is paramount. One of the most common and effective ways to achieve this is by utilizing encrypted PDF files. This method offers a balance of accessibility and security, making it a go-to solution for many professionals aiming to secure intellectual property pdf documents.
Over my years in software engineering, I've seen firsthand how crucial secure document sharing is. Mishandling sensitive data can lead to significant financial losses, reputational damage, and even legal complications. Fortunately, PDF technology offers built-in encryption features that, when used correctly, provide a strong layer of protection against unauthorized access.
Table of Contents
Understanding PDF Encryption
PDF encryption works by scrambling the data within a document, rendering it unreadable to anyone who does not possess the correct decryption key, typically a password. This process ensures that only authorized individuals can access the content. For anyone looking to secure intellectual property pdf files, this is the foundational step.
Key Concepts in PDF Security
When we talk about PDF encryption, we're usually referring to password protection. This can involve two types of passwords: one to open the document and another to restrict certain actions like printing, copying text, or editing the file. Understanding these distinctions is vital for comprehensive IP document protection.
Methods for Encrypting PDFs

Fortunately, encrypting a PDF is not a complex process and can be achieved through various means, catering to different user needs and software availability. I've used several of these methods myself, and they all serve the purpose effectively when applied correctly.
Using Adobe Acrobat Pro
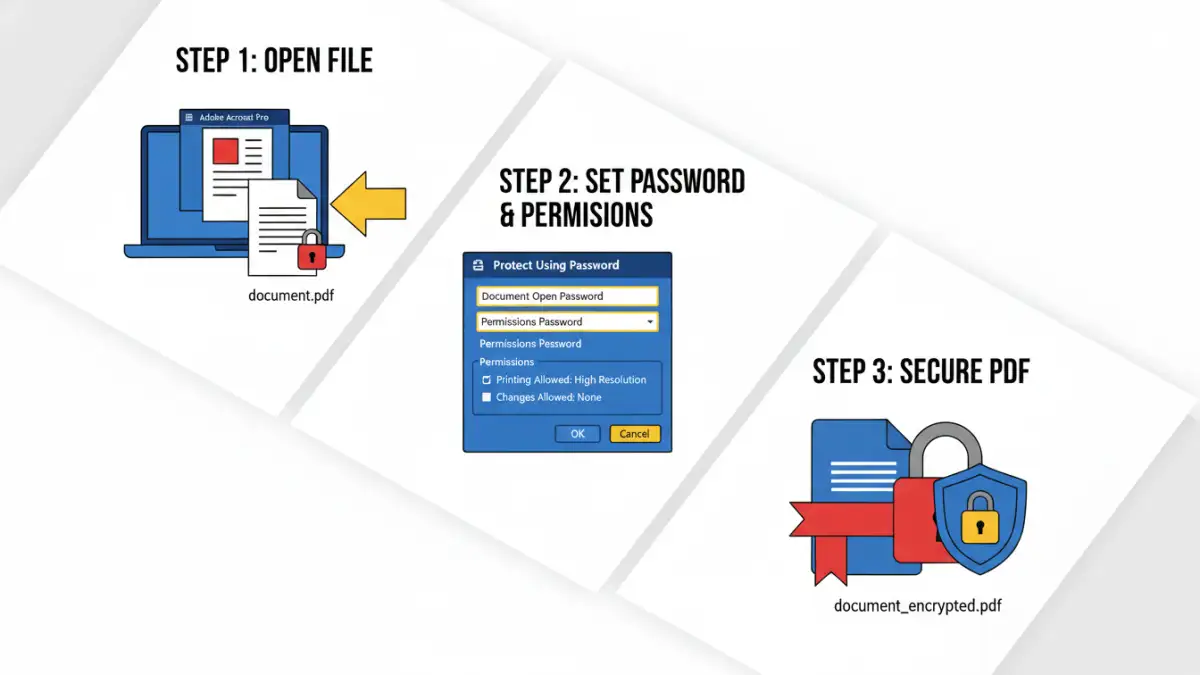
Adobe Acrobat Pro is a professional tool that offers robust PDF security features. You can encrypt your documents by navigating to 'File' > 'Protect Using Password.' Here, you can set passwords for opening the document and for restricting permissions. This is a reliable method for ensuring patent file encryption.
Using Online PDF Tools
Numerous online platforms offer free PDF encryption services. These tools are convenient for quick, on-the-go security needs. You simply upload your PDF, set a password, and download the encrypted version. However, for highly sensitive trade secret security, one must consider the privacy implications of uploading files to third-party servers.
Using Built-in OS Features
Both Windows and macOS offer ways to create password-protected PDFs, often through their print dialogs. When printing a document, you can choose the 'Save as PDF' option and look for security settings. While this is accessible, it might offer less granular control compared to dedicated software.
Advanced Security Features
Beyond basic password protection, advanced encryption techniques can offer even greater security. This includes using stronger encryption algorithms like AES-256, which is significantly harder to crack than older methods. Some tools also allow for certificate-based encryption, which uses digital certificates instead of passwords for authentication, offering a higher level of security for trade secret security.
Best Practices for IP Protection
To effectively secure intellectual property pdf files, it's not just about applying a password. It's about adopting a holistic approach to document security. This includes choosing strong, unique passwords, regularly updating them, and only sharing them through secure channels. Furthermore, consider limiting permissions to only what is absolutely necessary for the recipient.
Comparison of Encryption Methods
Choosing the right method for encrypting your PDFs depends on your specific needs, the sensitivity of the information, and the tools you have available. Here's a quick comparison:
Comparison Table: PDF Encryption Methods
| Method | Ease of Use | Security Level | Cost | Ideal For |
|---|---|---|---|---|
| Adobe Acrobat Pro | Moderate | High (AES-256) | Paid Subscription | Comprehensive IP document protection, legal documents |
| Online PDF Tools | Very Easy | Moderate (Varies by tool) | Free to Paid Tiers | Quick sharing, non-critical documents |
| Built-in OS Features | Easy | Moderate (Varies by OS) | Free | Basic protection, everyday documents |
| Third-Party Software | Moderate to Easy | High (Often AES-256) | One-time Purchase or Free Tiers | Regular use, enhanced features |
When dealing with valuable intellectual property, opting for a higher security level is always advisable. Methods like Adobe Acrobat Pro or reputable third-party desktop software often provide the most robust options for ensuring patent file encryption and overall IP document protection.
Extra tips before you try to secure intellectual property pdf
First, confirm what kind of protection you are dealing with. Some PDFs require a password to open (user password), while others only restrict printing/copying/editing (owner password). The safest approach depends on which one you have.
For sensitive documents, prefer offline tools and avoid uploading confidential files to unknown websites. If you must use an online tool, read the privacy policy and delete uploaded files immediately after processing.
- Try a different PDF viewer (some apps cache old permissions)
- Re-download the file (corruption can cause false password errors)
- Check caps lock / keyboard layout for password entry
- Differentiate “permission password” vs “open password” prompts
- If it is not your file, request access from the owner