
Working with a large collection of digital documents, whether for personal projects, business operations, or client work, often means dealing with sensitive information. Keeping these files organized, accessible, and most importantly, secure, can become a significant challenge. I've seen firsthand how the lack of a robust system can lead to data breaches, compliance issues, and wasted time trying to locate crucial files. This is where implementing effective document portfolio management strategies becomes paramount.
The digital landscape presents both opportunities and threats. While we can store vast amounts of data, the risk of unauthorized access, accidental deletion, or malicious attacks is ever-present. Establishing a secure framework isn't just about adding passwords; it's about a holistic approach to how documents are created, stored, accessed, shared, and archived. My experience has taught me that the right tools, combined with smart practices, can transform this often-daunting task into a streamlined, secure process.
Table of Contents
Understanding the Core Need for Security
The sheer volume of digital documents we handle today necessitates a proactive approach to security. From confidential client data and financial records to intellectual property and personal information, each file can carry significant risk if compromised. A breach can lead to severe financial penalties, reputational damage, and loss of trust, making robust security a non-negotiable aspect of document management.
Beyond external threats, internal risks like accidental data loss or unauthorized internal access also pose a threat. Implementing security measures helps mitigate these risks, ensuring data integrity and availability. This layered security approach protects your valuable information assets from various potential dangers.
Key Components of Secure Document Management

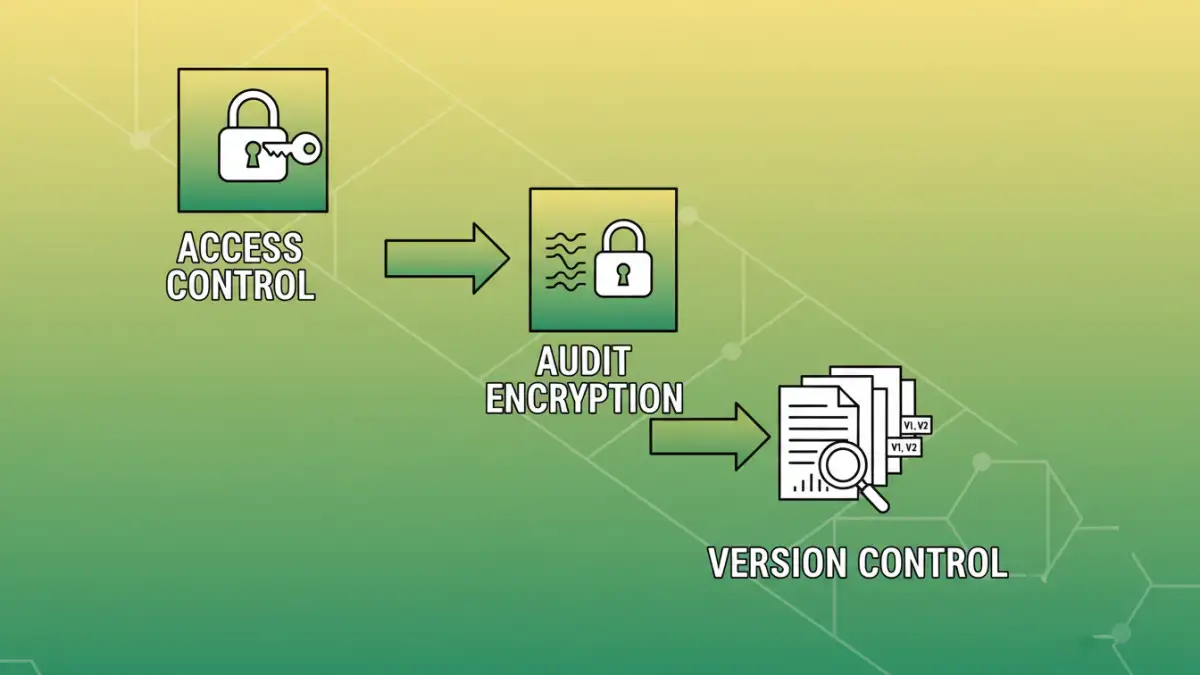
Effective secure document portfolio management relies on several interconnected components. These elements work together to create a comprehensive security framework that protects your documents throughout their lifecycle.
Access Control and Permissions
One of the foundational pillars of document security is robust access control. This involves defining who can view, edit, or delete specific documents and folders. Implementing granular permissions ensures that only authorized personnel have access to sensitive information, drastically reducing the risk of internal data leaks or accidental misuse.
Encryption and Data Protection
Encryption is the process of encoding data so that only authorized parties can read it. For sensitive documents, end-to-end encryption is crucial, meaning data is encrypted both in transit and at rest. This ensures that even if a file is intercepted or a storage device is lost, the data remains unreadable to unauthorized individuals. This is a critical layer for maintaining pdf portfolio security.
Audit Trails and Version Control
Maintaining a clear audit trail allows you to track all activities related to your documents, including who accessed, modified, or deleted them, and when. This is vital for compliance, accountability, and forensic analysis in case of a security incident. Coupled with effective version control, you can easily revert to previous document states if needed, preventing data loss and ensuring continuity.
Choosing the Right Secure Document Portfolio Tools
Selecting the appropriate tools is pivotal for streamlining your document management process while ensuring security. The market offers a variety of solutions, from simple file protection utilities to comprehensive document management software.
When evaluating options, consider factors like the types of documents you handle (PDFs, Word docs, spreadsheets, images), your team size, collaboration needs, and compliance requirements. Solutions range from built-in operating system features and cloud storage with encryption to specialized document management systems. The goal is to find a balance between robust security features, ease of use, and cost-effectiveness.
Cloud-Based vs. On-Premise Solutions
Cloud-based document management software offers flexibility, scalability, and accessibility from anywhere. These solutions often come with built-in security features like encryption and access controls. On-premise solutions provide greater control over your data and infrastructure but require more IT overhead for management and security.
Specialized Software Features
Look for features such as granular user permissions, multi-factor authentication, automatic backups, disaster recovery capabilities, and compliance certifications (like GDPR or HIPAA). Tools that offer robust pdf portfolio security, including password protection for individual files or entire portfolios, are particularly valuable for safeguarding sensitive collections.
Implementation Strategies for Success
Deploying secure document portfolio management tools is more than just installing software; it requires a strategic approach to ensure adoption and effectiveness. A phased rollout, starting with a pilot group, can help identify and resolve issues before a wider deployment.
Training your team on the new tools and security protocols is essential. They need to understand not only how to use the system but also why these security measures are in place. Clear policies regarding document handling, sharing, and retention should be established and communicated effectively to all users.
Best Practices for Ongoing Security
Maintaining a secure document portfolio is an ongoing effort. Regularly review and update access permissions, especially when employees change roles or leave the organization. Conduct periodic security audits to identify vulnerabilities and ensure compliance with policies.
Stay informed about the latest security threats and update your software and security protocols accordingly. Encourage a security-conscious culture within your team, where everyone understands their role in protecting sensitive information. Implementing these best practices ensures that your document management remains secure and efficient over time.
Comparison Table: Document Security Features
| Feature | Basic File Protection | Cloud Storage (with encryption) | Dedicated Document Management Software |
|---|---|---|---|
| Access Control | Limited (OS permissions) | User-based, role-based | Granular, permission-based |
| Encryption | Optional (e.g., password-protected files) | In-transit and at-rest encryption | End-to-end, advanced options |
| Audit Trails | Minimal or none | Basic logging | Comprehensive, detailed logs |
| Version Control | Manual or basic | Automatic versioning | Advanced versioning and rollback |
| Collaboration | Limited, often manual sharing | Good, with sharing links | Robust, integrated workflows |
| Scalability | Low | High | High |
| Cost | Free to low | Subscription-based | Subscription or licensing |