
With the explosion of mobile devices and cloud-based workflows, the demand for efficient yet powerful security has never been greater. For years, RSA has been the workhorse of public-key cryptography, but its age is starting to show. It requires increasingly large keys to stay secure, which slows down everything from establishing a secure connection to encrypting a file.
This is where a more modern approach comes in. I've seen firsthand in system architecture planning how switching to newer cryptographic standards can drastically improve performance without sacrificing security. The answer for many modern challenges is Elliptic Curve Cryptography (ECC), a powerful and efficient alternative poised to become the new standard.
Table of Contents
The Limits of Legacy Encryption
For decades, the RSA algorithm was the gold standard. Its security is based on the mathematical difficulty of factoring very large prime numbers. To maintain security against advancing computer power, RSA keys have had to grow significantly longer. A 2048-bit RSA key is now considered standard, with 4096-bit keys recommended for long-term security.
This brute-force approach to security comes at a cost. Larger keys require more computational power to generate and use, consume more storage, and increase latency. This isn't a major issue for a powerful desktop server, but it's a significant bottleneck for smartphones, IoT devices, and even busy web servers handling thousands of connections.
The Performance Bottleneck
I remember working on a project involving secure data transmission for a fleet of low-power sensors. Using standard RSA encryption was draining their batteries and creating unacceptable delays. The processing overhead of managing large keys was simply too much for the resource-constrained hardware. This is a classic example of where traditional methods struggle to keep up with modern demands.
What is Elliptic Curve Cryptography?

Elliptic Curve Cryptography is a different approach to public-key encryption. Instead of relying on factoring large numbers, its security is based on the difficulty of solving the elliptic curve discrete logarithm problem. In simpler terms, it uses the properties of points on a specific mathematical curve to create cryptographic keys.
Imagine a point on a curve. You can easily calculate a new point by "adding" the original point to itself a certain number of times. However, if you are only given the original point and the final point, it is computationally infeasible to determine how many times the addition was performed. That number is your private key, and the final point is your public key. This elegant mathematical trapdoor is what makes ECC so powerful.
The Key Size Advantage
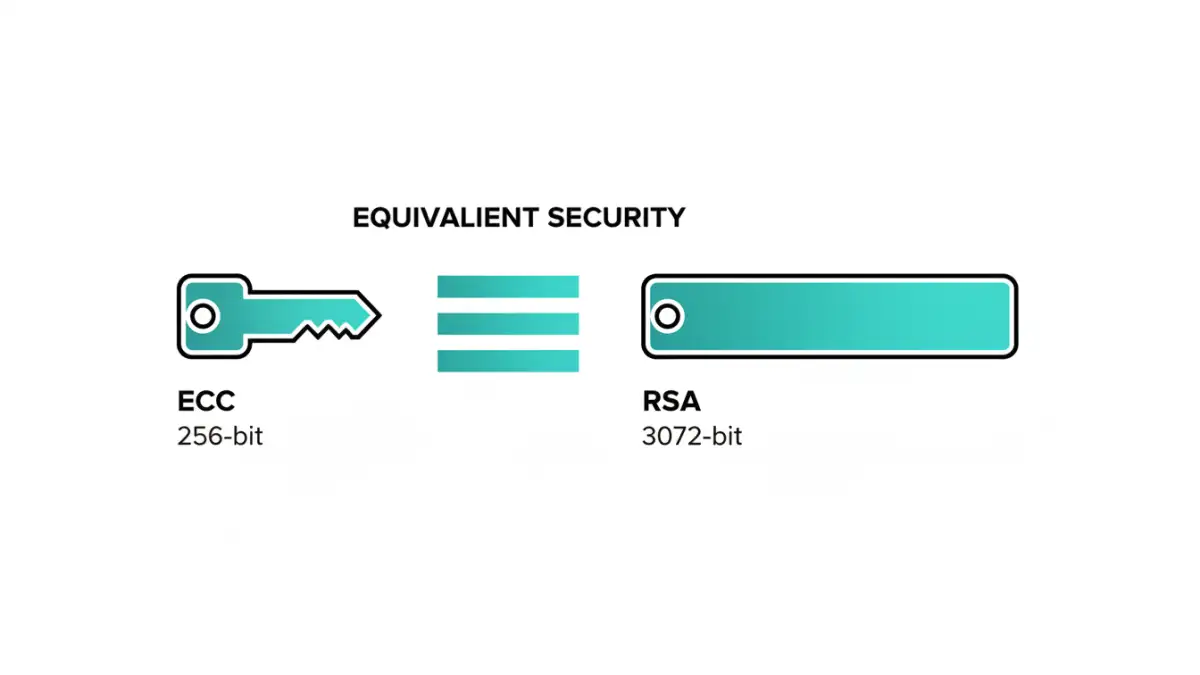
The most significant benefit of ECC is the security it provides for a given key size. A 256-bit ECC key offers a comparable level of security to a 3072-bit RSA key. This dramatic reduction in size means faster computations, lower power consumption, and reduced storage and bandwidth requirements. It's a prime example of more efficient, or 'lightweight cryptography', in action.
Why ECC Is Perfect for Modern Document Security
The efficiency of ECC makes it uniquely suited for today's technology landscape. When we talk about secure document encryption, we're no longer just thinking about a file sitting on a local hard drive. We're considering documents synced across multiple devices, accessed via mobile apps, and stored in the cloud.
For these scenarios, ECC's benefits are clear. Encrypting a document on your phone before uploading it to a cloud service is faster and consumes less battery. Secure sessions for accessing these documents can be established more quickly, leading to a better user experience. This efficiency is critical for applications that need to perform many cryptographic operations in a short amount of time.
Efficiency in Constrained Environments
The rise of the Internet of Things (IoT) further highlights ECC's importance. Devices like smart cards, medical implants, and industrial sensors often have very limited processing power and memory. Using RSA on these devices is often impractical. ECC provides a way to implement strong security without overwhelming their limited resources, making it a cornerstone of modern embedded systems security.
ECC in the Real World and Its Future
ECC isn't just a theoretical concept; it's already widely deployed. It's a key component of the TLS protocol that secures most of the web traffic today (HTTPS). It's also the cryptographic foundation for cryptocurrencies like Bitcoin and Ethereum, which rely on its efficiency and security for transaction signing.
As we move forward, ECC is set to become the default choice for new systems. Government agencies like the NSA have endorsed ECC for protecting classified information, signaling its robustness. For any developer or organization building systems that require strong and efficient encryption, choosing modern encryption algorithms like ECC is no longer just an option—it's a necessity for future-proofing security infrastructure.
Comparison Table: ECC vs. RSA
| Feature | Elliptic Curve Cryptography (ECC) | RSA |
|---|---|---|
| Key Size (Equivalent Security) | 256-bit | 3072-bit |
| Computational Cost | Low | High |
| Performance | Faster key generation and signing | Slower, especially with larger keys |
| Ideal Use Cases | Mobile devices, IoT, web servers, blockchain | Legacy systems, applications not constrained by performance |
| Security Strength per Bit | Very high | Lower, requires much larger keys |