
I once worked on a project involving highly sensitive legal contracts that needed to be shared between multiple parties across different organizations. Simply password-protecting a ZIP file wasn't enough; we needed to guarantee that only the intended recipient could open the document and also verify that it hadn't been tampered with. This is a classic scenario where simple password protection falls short and a more robust system is required.
This is where the elegance of asymmetric cryptography, specifically the RSA algorithm, comes into play. It solves two critical problems in secure file sharing: ensuring confidentiality (only the right person can read it) and guaranteeing authenticity (it really came from the person who claims to have sent it). It’s a foundational technology that powers much of the secure web, from SSL/TLS certificates to secure email.
Table of Contents
Understanding Asymmetric Cryptography
Before we can appreciate RSA, we need to understand the concept it's built on: asymmetric encryption, also known as public key cryptography. Unlike symmetric encryption where the same key is used to both encrypt and decrypt data (like a simple password), the asymmetric approach uses a pair of mathematically linked keys.
These two keys work together but are kept separate. What one key encrypts, only the other key can decrypt. This pair consists of a public key, which you can share freely with anyone, and a private key, which you must keep absolutely secret. Think of the public key as a secure mailbox slot that anyone can use to drop off a message for you, but only you have the private key to open the mailbox and read it.
The Role of the Public and Private Key Pair
The magic is in the separation of these keys. If someone wants to send you a secure document, they use your public key to encrypt it. Once encrypted, that document becomes an unreadable jumble of data to anyone who intercepts it. The only thing that can unscramble it back into a readable format is your corresponding private key. Even the sender, who used the public key to encrypt it, cannot decrypt it.
Why It's a Game-Changer for Sharing
This solves a massive problem in cryptography known as key distribution. With symmetric encryption, you have to find a secure way to share the secret key with your recipient. If you send it over an insecure channel, it could be intercepted, rendering your encryption useless. Public key cryptography eliminates this risk. You can post your public key on your website or email it in the clear without any worry, because it can only be used to lock data, not unlock it.
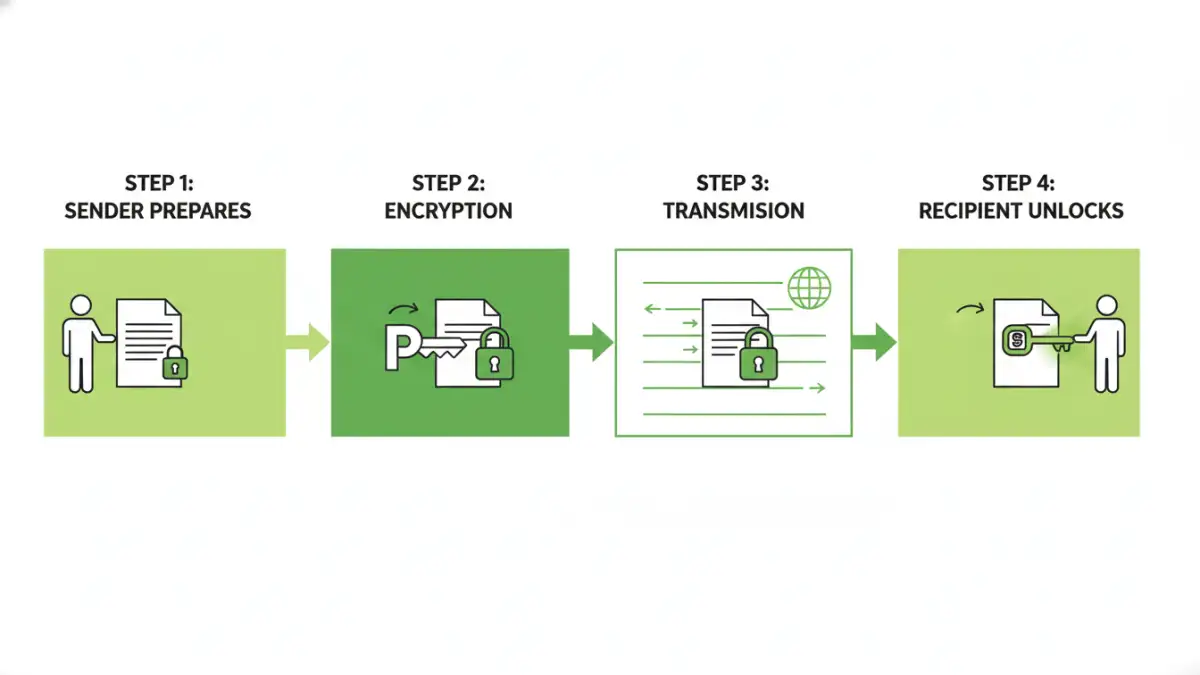
How RSA Secures a Document: A Step-by-Step Guide
The RSA algorithm (named after its inventors Rivest, Shamir, and Adleman) is the most widely used implementation of public key cryptography. Using RSA encryption for documents provides a robust framework for confidentiality. Let's walk through a typical secure file sharing scenario.
- Key Generation: The recipient (let's call her Alice) first generates her RSA key pair: a public key and a private key. She keeps her private key safe and sends her public key to the sender (Bob).
- Encryption by the Sender: Bob takes the sensitive document he wants to send to Alice. He uses her public key and an encryption program to scramble the document's contents. The output is an encrypted file that is unreadable without the correct key.
- Secure Transmission: Bob can now send this encrypted document to Alice over any channel—email, a cloud storage link, or a messaging app. He doesn't have to worry if someone intercepts it, because they won't have the key to open it.
- Decryption by the Recipient: Alice receives the encrypted file. She uses her private key, which she has kept secret, to decrypt the document. The file is instantly restored to its original, readable state. If anyone else tries to open it with a different key, they will only see gibberish.
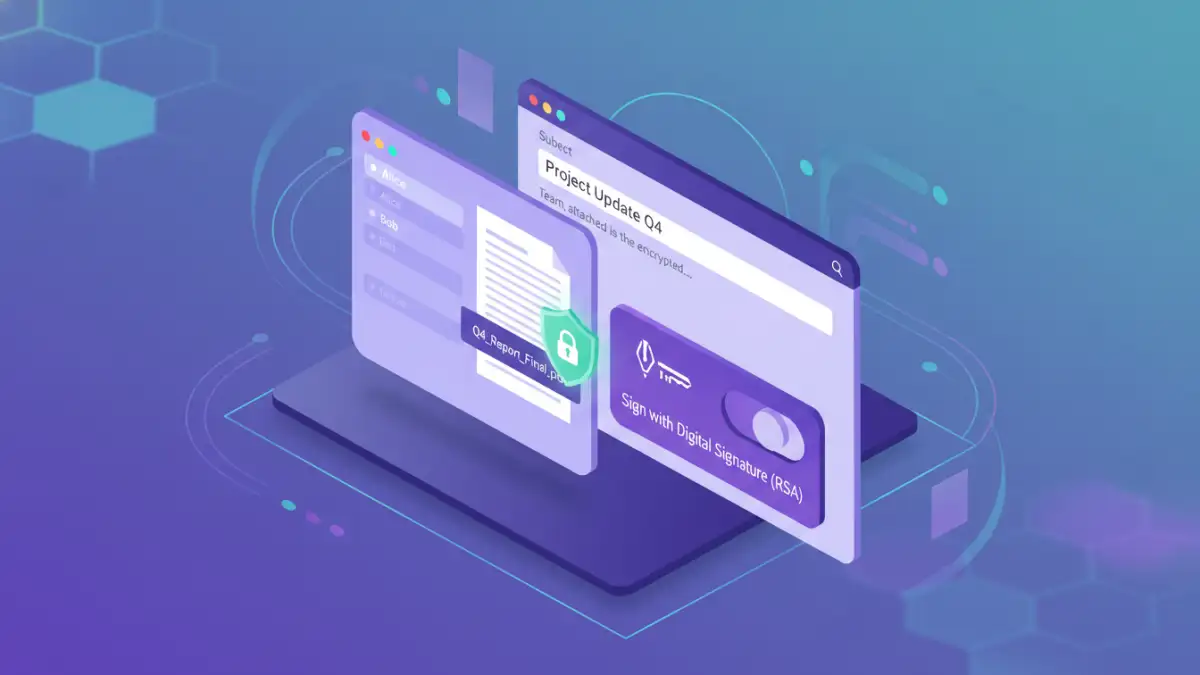
Beyond Encryption: RSA and Digital Signatures
Confidentiality is only half the battle. How does Alice know the document truly came from Bob and wasn't altered in transit? RSA's key pair mechanism can also be used to create digital signatures, which provide authenticity and integrity.
The process is essentially reversed. To 'sign' a document, Bob uses his own private key to encrypt a small piece of data related to the document (a hash). He then sends this signature along with the document. When Alice receives it, she can use Bob's public key (which is widely available) to decrypt the signature. If it decrypts successfully, it proves two things: the document could only have been signed by Bob (since only his private key could create a signature his public key can open), and the document hasn't been changed since he signed it.
The Power of Non-Repudiation
This creates a powerful property called non-repudiation. Bob cannot later deny that he sent the document, because only he has access to the private key that created the verifiable signature. This is critical for legal contracts, financial agreements, and official communications where sender identity is paramount.
Practical Applications and Tools
While the underlying math of RSA is complex, you don't need to be a cryptographer to use it. Many tools integrate this technology to provide secure file sharing capabilities. For instance, PGP (Pretty Good Privacy) and its open-source alternative, GnuPG, are classic examples that use asymmetric cryptography for securing emails and files.
Many modern secure collaboration platforms and some enterprise-grade cloud storage solutions use these principles under the hood to manage access and protect data. When you use a service that offers end-to-end encryption, it's often leveraging a hybrid system where asymmetric encryption is used to securely exchange a one-time symmetric key, combining the security of public key cryptography with the speed of symmetric encryption for the actual file transfer.
Encryption Method Comparison
| Feature | Asymmetric Encryption (RSA) | Symmetric Encryption (AES) |
|---|---|---|
| Keys Used | Two keys: a public and a private key. | One single, shared secret key. |
| Key Management | Simpler. Public key can be shared openly. | Complex. The shared key must be distributed securely. |
| Primary Use Case | Secure key exchange, digital signatures, encrypting small data. | Encrypting large amounts of data (bulk encryption). |
| Speed | Slower due to complex mathematical operations. | Significantly faster and more efficient. |
| Example Algorithms | RSA, ECC (Elliptic Curve Cryptography) | AES, DES, Blowfish |