
Have you ever set a password on a PDF and wondered what's happening behind the scenes to keep it safe? It’s not as simple as just storing your password somewhere. The real workhorse is a cryptographic concept called hashing, which transforms your simple password into a complex security key. Understanding this process is key to appreciating why some security methods are vastly superior to others.
Without a solid grasp of hashing, it's easy to assume all password protection is the same. But as I've seen in my work, the specific algorithm used can mean the difference between a document that's genuinely secure and one that offers a false sense of safety. Let's break down how this technology works and what it means for your sensitive files.
Table of Contents
What is a Hashing Algorithm?

At its core, a hashing algorithm is a mathematical function that takes an input (like your password) and produces a fixed-size string of characters, which is called the hash. Think of it like a digital fingerprint. No matter how long or short your password is, the output hash will always be the same length for a given algorithm.
This process is designed to be a one-way street. You can easily generate a hash from a password, but it's computationally infeasible to reverse the process and get the password from the hash. When you enter your password to open a PDF, the software hashes it and compares the result to the stored hash. If they match, the document unlocks.
Deterministic and Unique by Design
Two crucial properties of any good password hashing algorithm are that it's deterministic and collision-resistant. Deterministic means the same input will always produce the same output. 'Password123' will always generate the exact same hash. Collision resistance means it's incredibly unlikely that two different inputs will produce the same hash. This ensures that only the correct password will work.
Key Hashing Algorithms in PDF Security
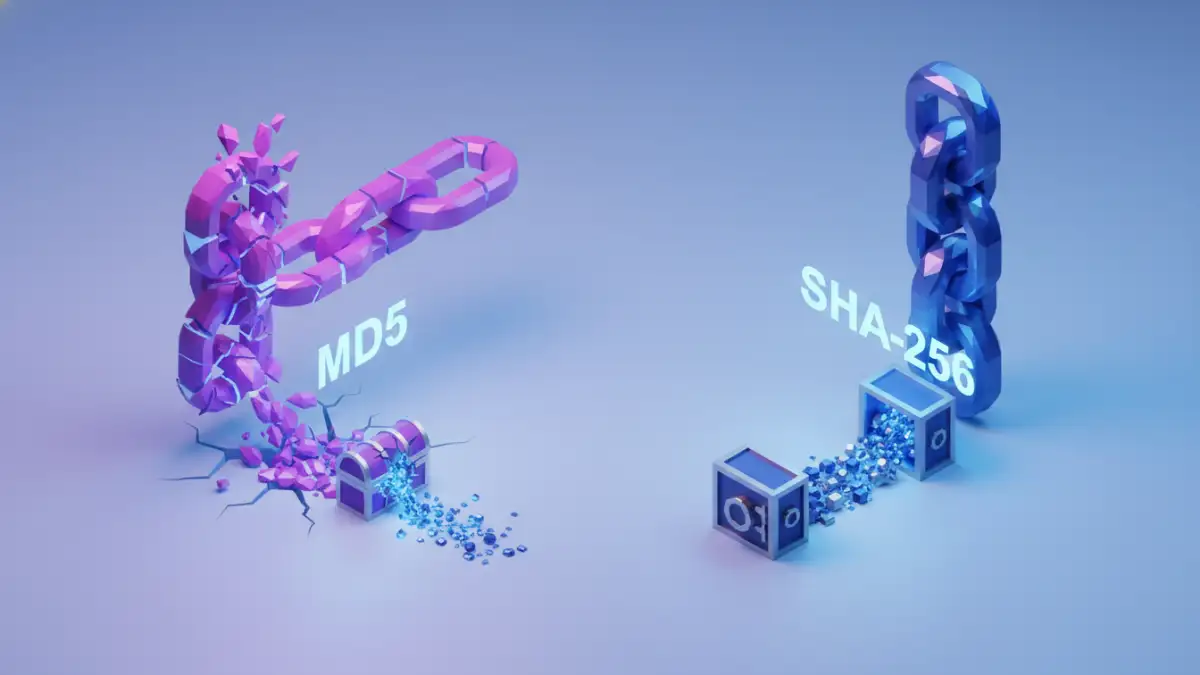
The PDF specification has evolved over the years, and so have the encryption and hashing methods it supports. Early versions relied on algorithms like RC4 and MD5, which were strong for their time but are now considered insecure and vulnerable to attacks. I've had to help clients migrate away from legacy systems that still used these outdated standards.
Modern PDFs, particularly those using AES (Advanced Encryption Standard) encryption, employ much stronger hashing functions. The most common and trusted of these is the SHA (Secure Hash Algorithm) family.
The Gold Standard: SHA-256 Hashing
When you see options for 128-bit or 256-bit AES encryption in your PDF software, you're often getting SHA-256 hashing as part of the package. SHA-256 produces a 256-bit (32-byte) hash, creating a massive number of possible outputs. This makes it extremely resistant to brute-force attacks and collisions, providing a robust foundation for your document's security.
Beyond Hashing: Salting and Key Stretching
A strong algorithm isn't the only component of excellent pdf password security. Two other techniques, salting and key stretching, are critical for defending against modern attacks. These methods are essential for any system focused on secure password storage.
Salting involves adding a unique, random piece of data (the 'salt') to your password before it's hashed. This means that even if two users have the same password, their stored hashes will be completely different. This simple step renders pre-computed hash lists, known as rainbow tables, useless for attackers. Creating salted hashes is a non-negotiable best practice.
Key stretching, or key derivation, intentionally makes the hashing process slow. The algorithm is run thousands, or even millions, of times. While this adds a negligible delay for a legitimate user entering one password, it makes a brute-force attack, which involves trying billions of passwords, prohibitively slow and expensive for an attacker.
How Strong Hashing Thwarts Attacks
So, how does this all come together to protect a file? When an attacker tries to crack a PDF password, they are essentially trying to guess the input that produces the correct hash. If the document uses an old algorithm like MD5 with no salt, they can try billions of common passwords per second.
However, if the document is protected with AES-256 encryption using a password that has been processed with SHA-256, a random salt, and a high iteration count (key stretching), the game changes. Each guess now requires significant computational work. The time required to crack the password expands from seconds or minutes to potentially thousands of years, making the attack impractical.
Hashing Algorithm Security Comparison
| Algorithm | Output Size | Security Status | Primary Weakness |
|---|---|---|---|
| MD5 | 128 bits | Broken | Vulnerable to collisions |
| SHA-1 | 160 bits | Deprecated | Considered insecure for most uses |
| SHA-256 | 256 bits | Secure | None known with current technology |
| SHA-512 | 512 bits | Secure | Slightly more computational overhead |
| Scrypt/bcrypt | Variable | Very Secure | Designed for passwords, less common in PDFs |