
Working with password-protected documents can be a complex area, touching on privacy, security, and legal boundaries. Whether you're a professional needing to share sensitive information or an individual receiving encrypted files, understanding the nuances is crucial. It's not just about knowing the password; it's about respecting permissions, ensuring data integrity, and adhering to various regulations.
From my experience, I've seen how easily misunderstandings can arise, leading to potential legal issues or security breaches. This guide aims to clarify what you need to know about your rights and responsibilities when dealing with these secured files.
Table of Contents
The Foundation of Document Protection
At its core, password protection for documents serves as a barrier against unauthorized access. This is achieved through various encryption methods, ranging from simple password prompts in word processors to sophisticated cryptographic algorithms. The intent is always to safeguard sensitive information, whether it's personal data, confidential business strategies, or intellectual property.
Why Password Protection?
The primary reasons for using password protection include maintaining confidentiality, ensuring data integrity, and complying with regulations like GDPR or HIPAA. When a document is password-protected, it signals that the information within is not meant for public consumption and requires explicit authorization to view or modify.
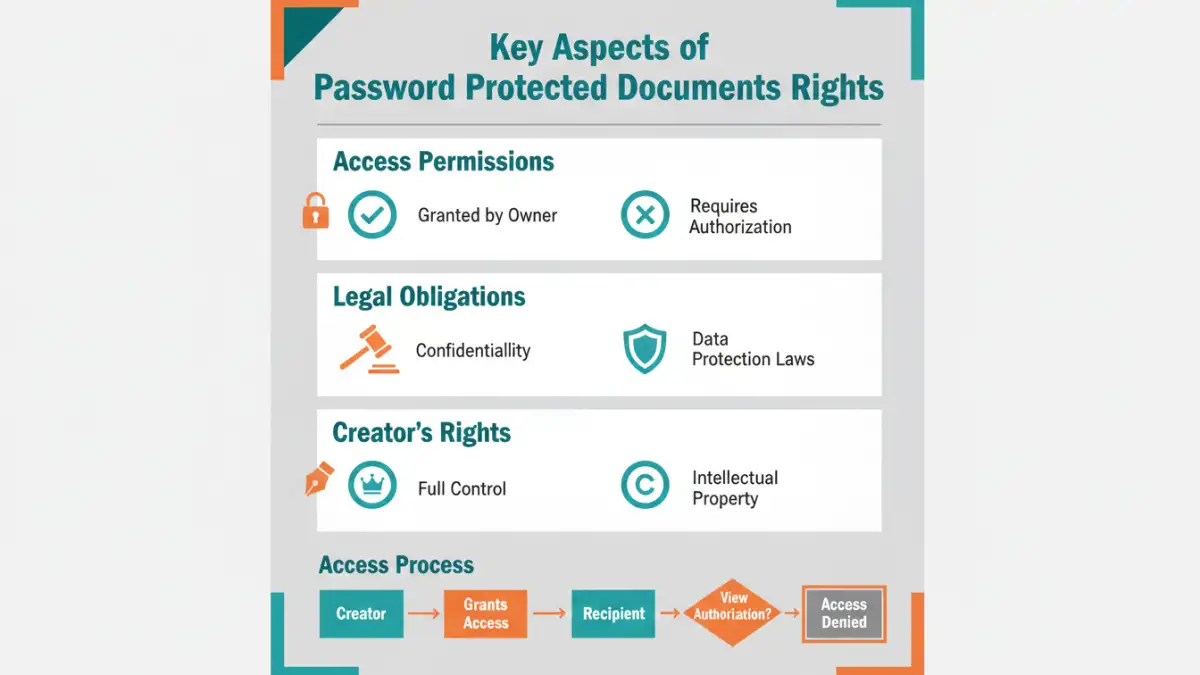
Understanding File Access Rights
File access rights are the permissions granted to individuals or systems to interact with a digital file. When a document is password-protected, these rights are inherently limited. The password acts as a gatekeeper, and only those who possess it (or can bypass it through legitimate means) are granted access.
It's important to distinguish between owning a password-protected file and having the right to access it. For instance, an employee might receive a password-protected report from their employer. While they possess the password to open the file, their access rights are still governed by their employment contract and company policies. They might have permission to read the document but not to share it further or make modifications.
Legal Frameworks and Protections
The legal landscape surrounding password-protected documents is shaped by data privacy laws, intellectual property rights, and contractual agreements. Laws like GDPR in Europe and CCPA in California dictate how personal data must be protected, and password encryption is a common method to achieve this.
When dealing with password protected documents rights, consider the context. If you are the creator or owner, you have the right to protect your information. If you are the recipient, your rights are typically defined by the sender's intent and any applicable laws or agreements. Unauthorized access or distribution of password-protected content can lead to legal repercussions, including civil lawsuits and, in some cases, criminal charges.
Intellectual Property and Copyright
Password protection can also play a role in safeguarding intellectual property and copyrighted material. By restricting access, creators can better control the distribution and use of their work, preventing unauthorized copying or dissemination.
Your Responsibilities
Possessing a password for a document comes with significant responsibilities. The most fundamental is to use the password only for its intended purpose and not to share it with unauthorized individuals. This includes respecting the sender's intent, whether it's for personal viewing, specific project collaboration, or limited internal use.
Furthermore, if you are responsible for creating and distributing password-protected documents, you have a duty to ensure the security of the passwords themselves. Weak passwords or insecure sharing methods can undermine the entire protection strategy. Responsible handling also means understanding when and how to revoke access if necessary, especially in a business context.
Best Practices for Secure Document Handling
To navigate the world of password-protected documents effectively and ethically, adopting best practices is key. This applies to both creators and recipients of secured files.
For Document Creators:
- Use strong, unique passwords that are difficult to guess.
- Employ robust encryption methods provided by reputable software.
- Clearly communicate the purpose and intended audience of the protected document.
- Consider using more advanced security features like access expiration dates if available.
For Document Recipients:
- Guard the password diligently and never share it with unauthorized parties.
- Understand the scope of your access rights – can you view, edit, or share?
- Report any suspected security vulnerabilities or unauthorized access attempts immediately.
- Do not attempt to bypass password protection through illicit means.
Comparison Table: Document Protection Methods
| Method | Pros | Cons | Use Case |
|---|---|---|---|
| Standard Password Protection (e.g., Word, PDF) | Easy to implement, widely supported | Can be bypassed with brute-force attacks if password is weak | General confidentiality, sharing with known individuals |
| Advanced Encryption Software | Stronger encryption algorithms, more control over permissions | Requires installation, potential cost, learning curve | Highly sensitive data, corporate security, legal compliance |
| Password Managers for Credentials | Securely stores and generates complex passwords for accessing protected files | Requires setup, managing the manager itself | Managing multiple document passwords, ensuring strong unique passwords |
| Cloud Storage Encryption (e.g., Google Drive, Dropbox) | Built-in security, accessible from multiple devices | Relies on provider's security, potential privacy concerns | Collaborative work, remote access to secured files |