The encryption that protects our emails, financial transactions, and sensitive documents feels unbreakable. For decades, it has relied on mathematical problems so difficult for classical computers that it would take them billions of years to solve. But a new type of computing is on the horizon, one that doesn't play by the same rules and threatens to make our current security obsolete.
This isn't science fiction. As a software engineer working with secure systems, the conversation has shifted from a theoretical 'what if' to a practical 'when and how.' The arrival of fault-tolerant quantum computers will fundamentally change the landscape of data protection, and understanding this threat is the first step toward building a secure future.
Table of Contents
The Classical Encryption Wall: How It Works Today
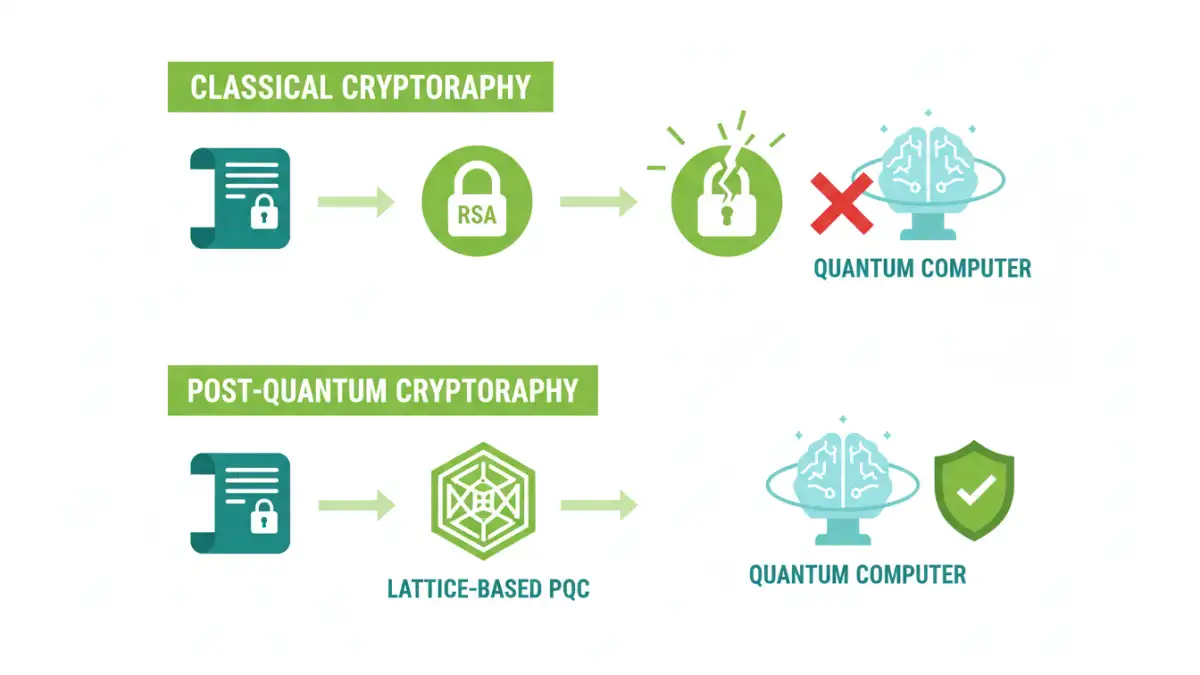
Most of the security we rely on today is built on public-key cryptography. Systems like RSA and Elliptic Curve Cryptography (ECC) are the bedrock of secure communication on the internet. They work on a simple principle: it's easy to perform a calculation in one direction but incredibly difficult to reverse it without a secret key.
For RSA, this 'hard problem' is integer factorization. It's simple to multiply two large prime numbers together to get a massive composite number. However, taking that massive number and finding its original prime factors is computationally infeasible for even the most powerful supercomputers we have today. This is the foundation of modern file encryption and secure communications.
Asymmetric Keys in Practice
Imagine a public mailbox. Anyone can drop a letter (encrypted data) into it using your public address (public key). But only you have the special key (private key) to open the mailbox and read the letters. Breaking RSA encryption without the private key is equivalent to figuring out the prime factors of the public key's massive number—a task considered impossible for classical machines.
The Quantum Hammer: Shor's Algorithm and Its Impact

Quantum computers operate on principles of quantum mechanics, like superposition and entanglement. This allows them to process a vast number of calculations simultaneously. While they won't replace our classical computers for everyday tasks, they are exceptionally good at solving certain types of problems—unfortunately, the exact types of problems our encryption relies on.
In 1994, mathematician Peter Shor developed a quantum algorithm that can find the prime factors of large numbers exponentially faster than any classical algorithm. This means a sufficiently powerful quantum computer running Shor's algorithm would make `breaking rsa encryption` a trivial task. The mathematical wall that protects our data would effectively crumble.
The 'Harvest Now, Decrypt Later' Threat
Even though large-scale quantum computers don't exist yet, the threat is immediate. Adversaries can capture and store encrypted data today with the intention of decrypting it years from now when a quantum computer becomes available. This makes the `future of data security` a present-day concern for governments, financial institutions, and any organization with long-term sensitive data.
Building a Quantum-Resistant Future: Post-Quantum Cryptography
The cryptographic community has been preparing for this for years. The solution is not to make existing algorithms more complex but to switch to entirely new ones. This new field is called `post quantum cryptography` (PQC). These are algorithms designed to run on the classical computers we use today but are believed to be secure against attacks from both classical and quantum computers.
These new cryptographic systems are based on different mathematical problems that are thought to be hard for even quantum computers to solve. The U.S. National Institute of Standards and Technology (NIST) has been running a multi-year competition to standardize a suite of these `quantum resistant algorithms` to ensure a smooth and secure transition.
Practical Steps for a Secure Transition
Migrating an organization's entire cryptographic infrastructure is a monumental task. It's not as simple as flipping a switch. From my perspective, the most critical first step is achieving 'crypto-agility.' This means designing systems that can easily swap out cryptographic algorithms without a complete overhaul.
Organizations should begin by creating an inventory of all systems that use public-key cryptography. Where is it used? What data does it protect? How long does that data need to remain secure? Answering these questions now allows for a prioritized and planned migration to PQC standards once they are finalized. Waiting until the threat is at the door will be too late.
Cryptographic Algorithm Comparison: Classical vs. Quantum-Resistant
| Algorithm Family | Underlying Math Problem | Vulnerability to Quantum Attack | Example |
|---|---|---|---|
| Asymmetric (Classical) | Integer Factorization | High (Shor's Algorithm) | RSA |
| Asymmetric (Classical) | Elliptic-Curve Discrete Logarithm | High (Shor's Algorithm) | ECDH/ECDSA |
| Symmetric (Classical) | Substitution-Permutation Network | Moderate (Grover's Algorithm) | AES |
| Lattice-Based (PQC) | Shortest Vector Problem (Lattices) | Believed to be Low | CRYSTALS-Kyber |
| Hash-Based (PQC) | Security of Cryptographic Hash Functions | Believed to be Low | SPHINCS+ |