
When a colleague at a public agency I once consulted for mentioned a 'minor' data leak, it turned out to be a classic case of weak credentials. An internal document, protected by a simple, easily guessed password, was accessed by an unauthorized employee. This incident underscores a critical reality: securing internal government documents isn't just about locking a file; it's about building a fortress of policies and controls around it.
The stakes are incredibly high in the public sector. A compromised document could expose sensitive citizen data, national security information, or confidential policy details. That's why a well-defined and strictly enforced password policy is the foundational layer of any serious internal document security strategy.
Table of Contents
Foundations of a Public Sector Password Policy
Standard corporate password rules often fall short for government needs. The public sector operates under a different set of risks and regulatory pressures. State-sponsored cyber threats, stringent compliance mandates, and the sheer sensitivity of the data require a more rigorous approach to confidential document protection.
Understanding Compliance Frameworks
Before writing a single rule, it's essential to understand the governing frameworks. Standards like the National Institute of Standards and Technology (NIST) Special Publication 800-53 or the Federal Information Security Management Act (FISMA) provide detailed controls and baselines. These aren't just suggestions; they are often legal requirements that dictate everything from password length to audit logging.
Assessing Information Sensitivity
Not all documents are created equal. A policy should accommodate different levels of data classification, such as Controlled Unclassified Information (CUI), Secret, or Top Secret. The password requirements for accessing a public-facing report should be vastly different from those for a classified intelligence briefing. This tiered approach ensures that the most sensitive data receives the highest level of protection without overburdening users working with less critical information.
Core Components of an Effective Policy

A strong government document password policy is built on several key pillars that work together to create a resilient defense against unauthorized access. These rules should be clear, enforceable, and communicated effectively to all personnel.
Password Complexity and Length
The days of '8 characters with one number' are long gone. Modern policies should enforce a minimum length of 14-16 characters. More importantly, they should encourage the use of passphrases—memorable but long sequences of words—over complex, hard-to-remember strings. The policy must also require a mix of uppercase letters, lowercase letters, numbers, and special characters, enforced automatically by the system.
Password History and Rotation
To prevent attackers from reusing compromised credentials, a policy must enforce password history. This means the system should remember a user's last 10-12 passwords and prevent them from being reused. Additionally, mandatory password rotation, typically every 60 to 90 days, limits the window of opportunity for an attacker who has managed to steal a valid credential.
Implementation and Enforcement Strategies
A policy is useless if it isn't enforced. My experience has shown that technical enforcement is far more effective than relying on user compliance alone. This is where IT infrastructure plays a pivotal role in ensuring public sector password rules are followed without exception.
Using Centralized Management Tools
For most government agencies, tools like Microsoft's Active Directory and Group Policy Objects (GPOs) are the workhorses of policy enforcement. An administrator can configure a GPO to enforce every aspect of the password policy—length, complexity, history, and expiration—across the entire network. This ensures that every user and every system adheres to the same high standard, providing consistent internal document security.
Mandating Multi-Factor Authentication (MFA)
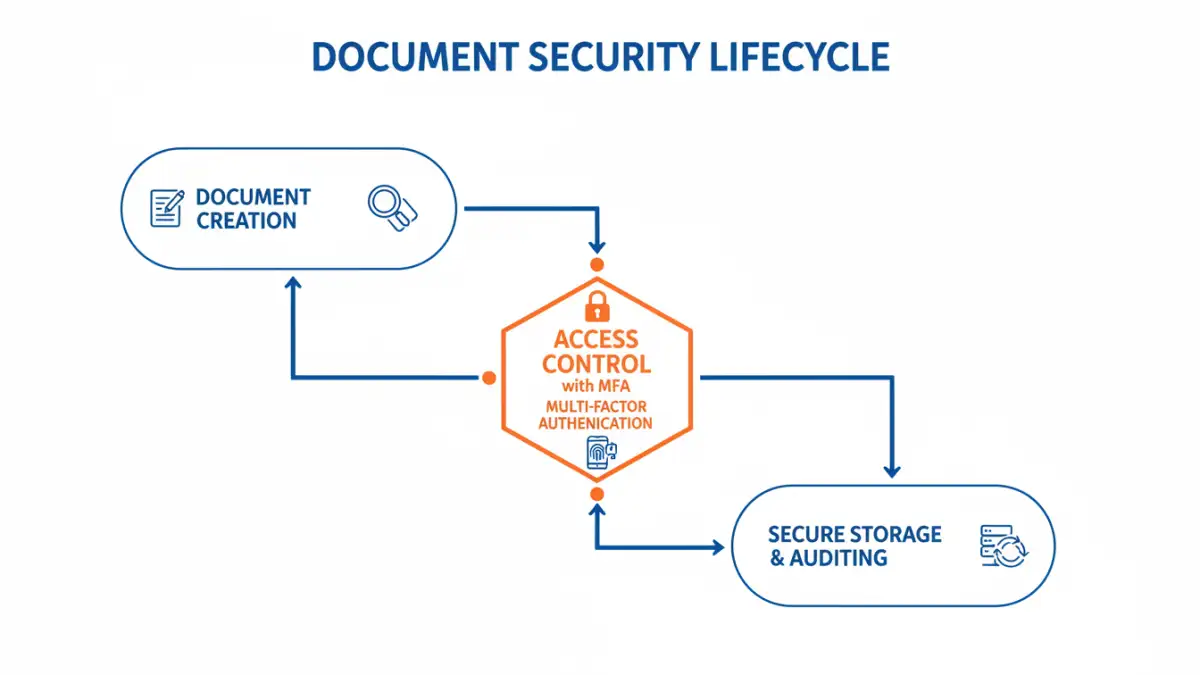
Passwords can be stolen. Multi-Factor Authentication (MFA) is the single most effective control to mitigate this risk. By requiring a second form of verification, such as a code from a mobile app, a physical security key, or a biometric scan, MFA ensures that a compromised password alone is not enough to grant access. For sensitive systems, MFA should be considered non-negotiable.
Beyond Passwords: A Holistic Security Approach
While passwords are a critical component, they are only one part of a comprehensive security posture. Achieving true confidential document protection requires thinking about the entire access lifecycle, from user permissions to data encryption.
Implementing Role-Based Access Control (RBAC)
The Principle of Least Privilege is paramount. RBAC ensures that users only have access to the information and systems necessary to perform their job duties. A financial analyst should not have access to HR records, and an IT administrator should not be able to view classified policy documents unless it's part of their role. This compartmentalization drastically reduces the potential impact of a compromised account.
Encryption at Rest and in Transit
Finally, robust encryption is essential. Data should be encrypted both when it's stored on a server or hard drive (at rest) and when it's being transmitted over the network (in transit). This ensures that even if an attacker bypasses other security controls and gains access to the raw data, it remains unreadable and useless without the proper decryption keys. This provides a final, powerful layer of defense for secure file access.
Policy Component Comparison
| Policy Component | Security Impact | Implementation Complexity | Best For |
|---|---|---|---|
| Minimum Length (14+ chars) | High | Low | Baseline for all accounts |
| Complexity Requirements | Medium | Low | Preventing simple dictionary attacks |
| Password History (10+ old) | Medium | Low | Stopping password reuse |
| Rotation (60-90 days) | Medium | Low | Limiting credential exposure time |
| Multi-Factor Authentication (MFA) | Very High | Medium | Protecting all sensitive and remote access |
| Role-Based Access Control (RBAC) | High | High | Limiting lateral movement and insider threats |