
Imagine this scenario: a critical project file containing sensitive financial projections has been altered, but no one knows who did it or when. Panic sets in. Without a clear record of activity, you're left guessing, pointing fingers, and trying to reconstruct events from memory—a nightmare for any organization. This is precisely the problem that a robust audit trail solves.
An audit trail is the digital equivalent of a detective's notebook. It meticulously records every significant action related to a file or system, providing a clear, chronological history that is indispensable for security and accountability. It’s not just a feature; it’s a foundational component of modern data governance.
Table of Contents
What Exactly Is a Security Audit Trail?
At its core, a security audit trail is an unchangeable, time-stamped log of security-relevant events. Think of it as a detailed ledger that answers the critical questions of who, what, when, and where for every action taken on a file. This isn't just about tracking who opened a document; it's about creating a comprehensive record of the entire file lifecycle.
These records, often called document access logs, capture everything from file creation, viewing, and modification to deletion, printing, and permission changes. Unlike generic system logs that might track server performance, a security-focused trail is specifically designed to provide context for security investigations and prove accountability.
Key Components of a Meaningful Log
A useful audit log entry contains several key pieces of information. It must identify the user who performed the action, specify the exact action taken (e.g., 'file_deleted'), record the precise timestamp, and note the location or IP address from which the action originated. It should also log the outcome, such as whether a login attempt succeeded or failed. Without this level of detail, the log is just noise.
The Core Pillars Supported by Audit Trails

Audit trails are more than just a historical record; they are an active defense mechanism that reinforces several critical aspects of your security posture. They provide the necessary evidence to enforce policies and investigate incidents effectively.
The first pillar is accountability. When employees know that their actions are being logged, it inherently discourages unauthorized or malicious behavior. If an incident does occur, you can trace the action back to a specific individual, removing ambiguity and enabling a targeted response. I've seen this firsthand where the mere presence of detailed logging stopped potential internal data misuse before it started.
Proactive Threat Detection and Rapid Incident Response
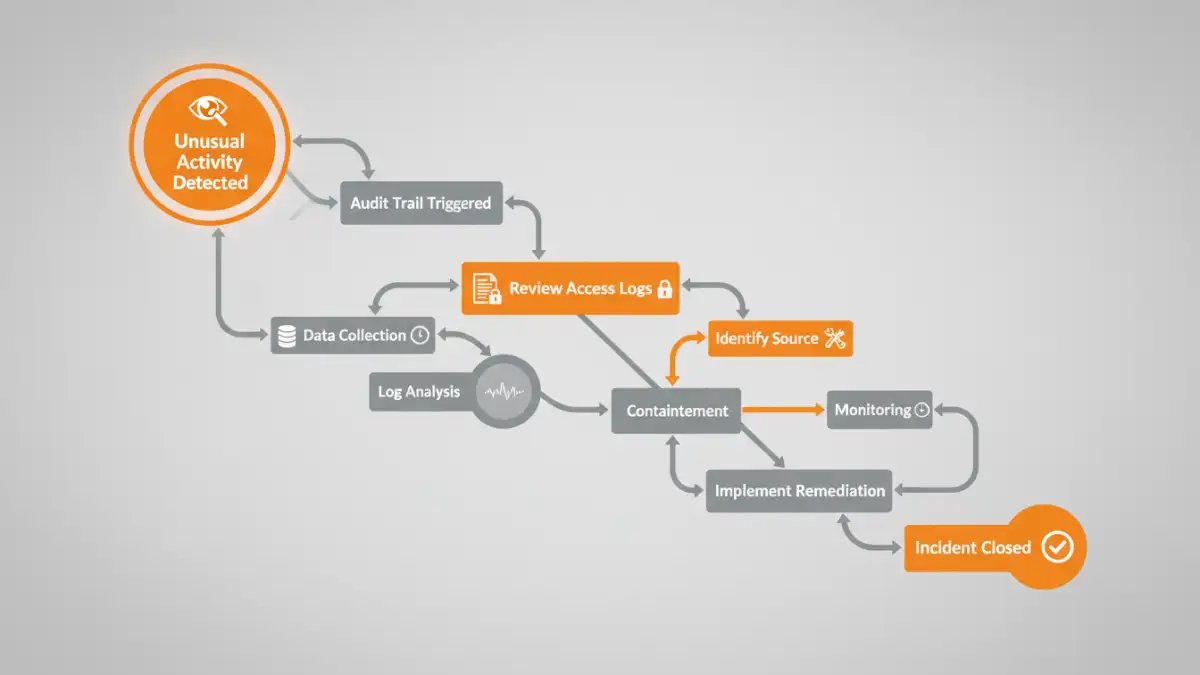
Modern systems can analyze audit trails in real-time to detect anomalous behavior. For example, if a user who normally accesses three files a day suddenly downloads hundreds, an alert can be triggered. This proactive approach to file activity monitoring allows security teams to intervene before a minor issue becomes a major data breach.
When an incident does happen, the security audit trail is the first place investigators turn. It provides the forensic data needed to understand the scope of the breach, identify the compromised accounts or systems, and determine what data was accessed or exfiltrated. A swift and accurate response is impossible without this detailed historical context.
Meeting Compliance Mandates with Confidence
For organizations in regulated industries, audit trails are not optional—they are a legal requirement. Regulations like GDPR, HIPAA, SOX, and PCI DSS all mandate that companies maintain detailed records of access to sensitive data. Failure to do so can result in severe financial penalties and reputational damage.
A well-maintained audit trail serves as concrete proof that you are enforcing access controls and monitoring sensitive information. During an audit, you can quickly generate reports to demonstrate compliance. This process, known as compliance reporting, is streamlined when all the necessary data is already being collected in a structured, searchable format.
Implementing Effective File Activity Monitoring
Setting up a useful audit trail system requires a strategic approach. You can't simply turn on logging for everything, as this can create an overwhelming amount of data that is difficult to analyze. The first step is to identify your most sensitive data and define what constitutes normal versus suspicious activity.
Focus on logging high-risk events: changes to user permissions, access to files containing PII or financial data, failed login attempts, and large-scale data exports or deletions. Centralizing these logs from various systems into a single platform (like a SIEM solution) is crucial for correlation and analysis. This unified view is essential for a robust enterprise file security strategy, allowing you to see the complete picture of activity across your network.
Audit Trail Feature Comparison
| Feature | Description | Importance for Security |
|---|---|---|
| User Identification | Logs the specific user account associated with an action. | Crucial for accountability and tracing actions to an individual. |
| Event Timestamps | Records the exact date and time of every event. | Essential for creating a chronological timeline during an investigation. |
| Event Type | Specifies the action taken (e.g., read, write, delete, permission change). | Provides context to understand the user's intent and impact. |
| Source IP/Location | Captures the originating IP address or geographic location of the user. | Helps identify unauthorized access from unusual or blacklisted locations. |
| Immutability | Ensures that log entries cannot be altered or deleted. | Guarantees the integrity of the audit trail for forensic and legal purposes. |
| Automated Alerting | Triggers notifications based on predefined rules for suspicious activity. | Enables proactive threat detection and rapid response. |