
Working with sensitive information requires a robust approach to safeguarding digital assets. Whether you're a freelancer managing client contracts, a small business owner handling financial records, or an individual protecting personal documents, ensuring the security of your digital portfolio is paramount. This guide will walk you through the essential strategies and techniques to build a strong defense for your valuable files.
From understanding the basics of encryption to implementing advanced access controls, we'll cover the critical aspects of portfolio file protection. My experience has shown me that a layered security approach is always the most effective. This means not relying on a single method but combining several strategies to create a resilient system against unauthorized access and data breaches.
Table of Contents
- Understanding the Basics
- Core Concepts in Document Security
- Practical Methods for Protection
- The Browser 'Trick' for Password-Protected PDFs
- Leveraging Online Document Security Tools
- Using Desktop Software for Enhanced Security
- Advanced Techniques for Portfolio Security
- Implementing Access Control and Permissions
- Best Practices for Ongoing Security
- Regular Audits and Updates
Understanding the Basics
At its core, document portfolio security is about preventing unauthorized access, modification, or deletion of your digital files. This involves a combination of technical measures and diligent practices. It's not just about locking a single file; it's about creating a secure environment for your entire collection of documents.
Core Concepts in Document Security
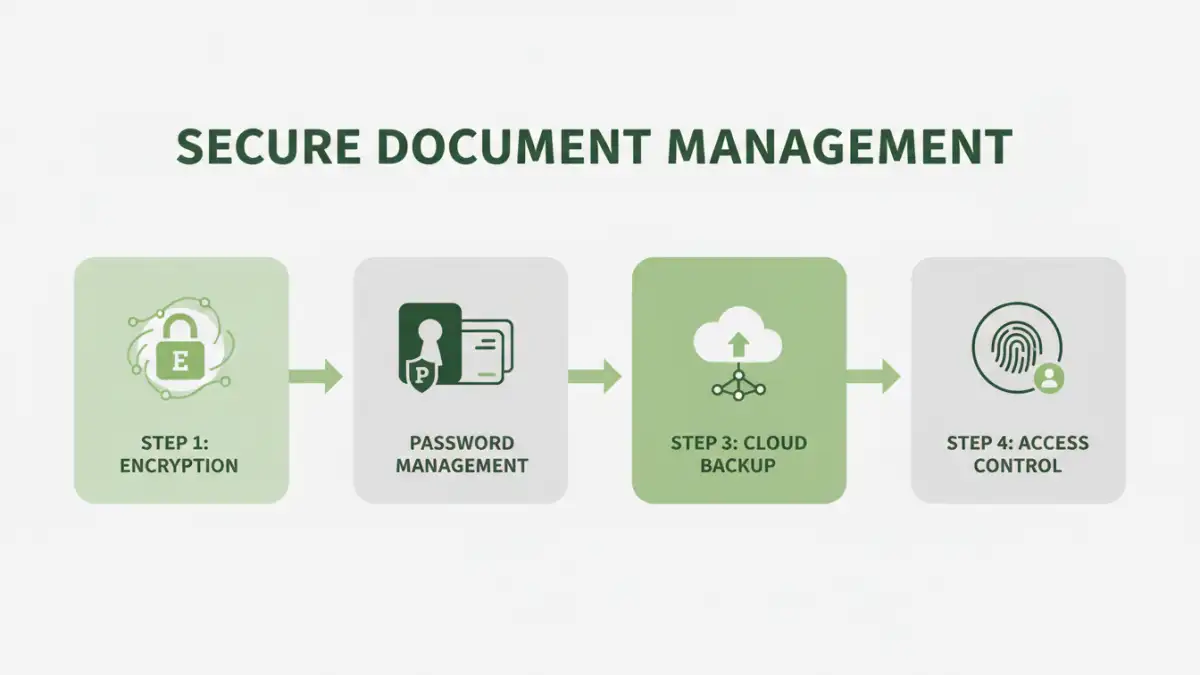
Several fundamental concepts underpin effective document security. Encryption is the process of scrambling data so it can only be read with a specific key or password. Access control involves setting permissions to determine who can view, edit, or share files. Data integrity ensures that documents haven't been tampered with since they were last saved.
Practical Methods for Protection

There are numerous ways to secure your documents, ranging from simple built-in features to sophisticated software solutions. The best approach often depends on the sensitivity of the data, your technical comfort level, and the types of documents you handle. I've found that combining methods often yields the best results.
The Browser 'Trick' for Password-Protected PDFs
One common scenario involves needing to remove a password from a PDF that you rightfully own but have forgotten the password for. While not a true security measure, a common workaround for PDFs protected with a user/owner password (not an open password) is to use your web browser. You can open the encrypted PDF in a browser like Chrome or Firefox, then use the print function to save it as a new PDF. This often strips the owner password, allowing you to save it as an unprotected file. This method only works for certain types of PDF restrictions.
Leveraging Online Document Security Tools
Numerous online platforms offer services for encrypting, decrypting, and password-protecting various file types. These tools are often user-friendly, requiring just an upload and a few clicks. They can be excellent for quick tasks, but it's crucial to consider the privacy policies of these services, as you are entrusting your files to a third party.
Using Desktop Software for Enhanced Security
For more robust and private document portfolio security, dedicated desktop software is often the best choice. Applications like VeraCrypt, AxCrypt, or even built-in features in operating systems like Windows BitLocker or macOS FileVault provide strong encryption and can create secure containers for your files. These solutions keep your data on your local machine, offering greater control and privacy.
Advanced Techniques for Portfolio Security
Beyond basic password protection and encryption, advanced techniques can significantly bolster your document portfolio security. These methods require a deeper understanding but offer a higher level of protection against sophisticated threats.
Implementing Access Control and Permissions
For collaborative environments or shared drives, managing access control is vital. This involves setting granular permissions for different users or groups, ensuring they only have access to the files and folders necessary for their roles. Most cloud storage services and network-attached storage (NAS) devices offer sophisticated permission management tools.
Regular Audits and Updates
Security is not a one-time setup; it's an ongoing process. Regularly auditing your security measures, reviewing access logs, and updating your software are crucial. This helps identify potential vulnerabilities before they can be exploited. Keeping your operating system, antivirus software, and any document security applications up-to-date is fundamental.
Best Practices for Ongoing Security
Implementing strong passwords and multi-factor authentication (MFA) for any accounts that manage your documents is non-negotiable. Avoid using simple or easily guessable passwords. For sensitive files, consider encrypting them individually or within a secure container, even if they are stored on a password-protected computer. Regularly backing up your data to a secure, separate location (like an encrypted external drive or a trusted cloud backup service) is also a critical safeguard against data loss.
Comparison Table
| Method | Pros | Cons | Use Case |
|---|---|---|---|
| Browser 'Trick' | Free, no extra software | Only for specific PDF owner passwords, not secure | Quick removal of forgotten owner password |
| Online Tools | Easy to use, accessible anywhere | Privacy concerns, potential data exposure | Non-sensitive files, quick encryption/decryption |
| Desktop Software | Powerful encryption, local control, privacy | Requires installation, can have a learning curve | Sensitive documents, business use, personal data |
| Built-in OS Encryption (e.g. BitLocker, FileVault) | Integrated, strong encryption, often free with OS | Requires OS support, setup can be complex | Full-disk or drive encryption for overall system security |