
Have you ever wondered why you can't copy text from a purchased ebook or easily share a movie file you bought online? The technology behind these restrictions is Digital Rights Management, or DRM. It's a set of access control technologies that creators and publishers use to limit the use of their digital content and devices after sale.
From my perspective as an engineer who has worked on content delivery pipelines, DRM is a fascinating and often controversial piece of the puzzle. It's not just a simple lock; it's a complex system of encryption, licenses, and validation rules designed to enforce the terms of a digital sale. Understanding it is key to grasping how modern digital media works.
Table of Contents
What is DRM and Why Does It Matter?
At its core, Digital Rights Management is about controlling what a user can do with digital media. The primary goal is to prevent unauthorized redistribution of digital media and restrict the ways consumers can copy content they've purchased. Think of it as the digital equivalent of a bouncer at a club, checking your ticket and ensuring you follow the house rules.
This matters immensely for content creators—authors, musicians, filmmakers, and software developers. It's their primary tool against piracy, which can significantly impact their revenue. By implementing DRM, they aim to ensure that only legitimate, paying customers can access their work, preserving the value of their intellectual property in an age where copying a file is trivial.
The Scope of DRM Protection
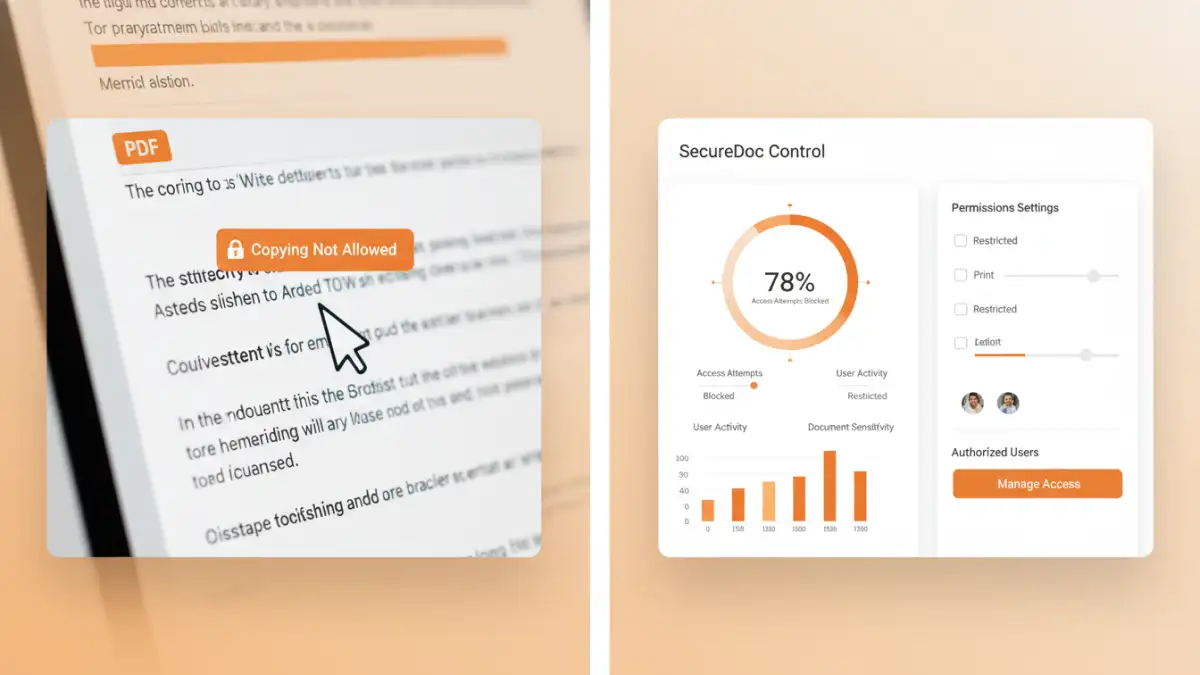
DRM isn't a single technology but a broad category. It can be applied to almost any digital file, including ebooks (like Amazon's Kindle format), music (Apple's old FairPlay system), videos (Netflix and Disney+ streaming), software, games, and even sensitive corporate documents. The rules can be granular, controlling whether you can print, copy, edit, or even access the content after a certain date or on a specific device. This level of control is what makes document drm security a powerful tool for enterprises.
How DRM Technology Actually Works
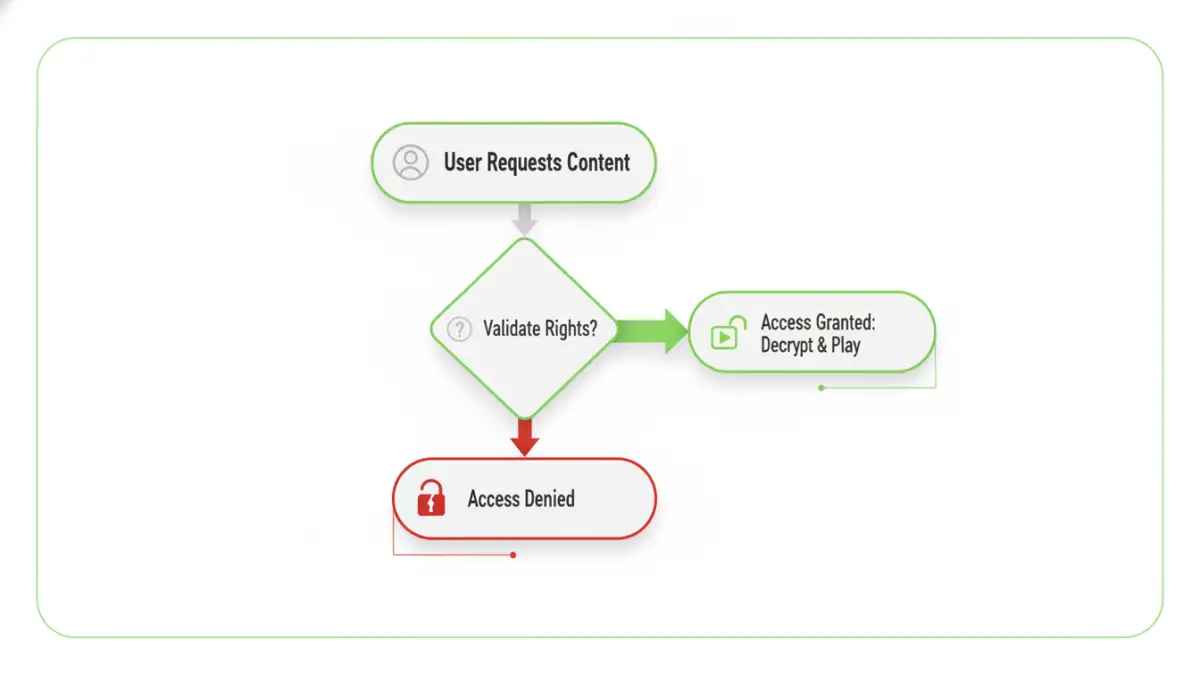
The magic behind DRM lies in a multi-step process involving encryption and licensing. It's not just about slapping a password on a file; it's a dynamic system that verifies rights in real-time. When you build or integrate these systems, you quickly realize how many moving parts are involved.
Encryption and Keys
First, the content itself is encrypted. This means the data is scrambled into an unreadable format using a complex algorithm. To unscramble it, you need a specific digital key. This encrypted content can be freely distributed, but it's useless without the corresponding decryption key. The real trick is managing how that key is delivered to a legitimate user.
This is where the license server comes in. When you try to open a DRM-protected file, your device or application sends a request to a remote license server. The server authenticates you (checks if you've paid, are logged in, etc.) and, if everything checks out, sends back the decryption key. This key is often stored securely on your device and may come with its own set of rules, like an expiration date.
Common DRM Implementations in the Wild
You interact with DRM every day, often without realizing it. The specific implementation varies depending on the content type and the company providing it. Reviewing different DRM software and platforms shows a wide range of approaches, from heavyweight protection to more subtle methods.
For example, the video streaming industry relies heavily on DRM. Systems like Google Widevine, Microsoft PlayReady, and Apple FairPlay are built into browsers and operating systems to secure the streaming pipeline from the server to your screen. This is why you can't simply use a screen recorder to capture Netflix content—the DRM system blocks it at the operating system level.
In the world of documents, Adobe's DRM is a classic example of pdf copy protection. It's used by libraries and publishers to manage ebook lending and sales. It can restrict printing, prevent copy-pasting, and set expiration dates on files, offering a high degree of secure document control.
The Challenges and Controversies of DRM
Despite its benefits for creators, DRM is not without its critics. A major pain point is the user experience. Legitimate customers can be locked out of content they paid for due to server issues, device changes, or a company going out of business. I've personally run into issues where I couldn't access a purchased technical ebook on a new e-reader because of compatibility conflicts between DRM systems.
This raises a fundamental question: When you buy a digital product, do you own it, or are you just licensing it? DRM enforces the latter, which can feel unfair to consumers accustomed to the ownership rights associated with physical goods. Furthermore, determined pirates often find ways to break DRM, meaning the restrictions primarily affect paying customers while failing to stop the most dedicated pirates.
DRM Approaches Compared
| DRM Type | How It Works | Pros | Cons |
|---|---|---|---|
| Hard DRM | Strong encryption tied to specific devices or accounts (e.g., Apple FairPlay, Adobe Adept). | High level of copy protection; difficult to bypass. | Poor user experience; compatibility issues; risk of losing access. |
| Soft DRM / Social DRM | Embeds user-identifying information (watermarks) into the file. | User-friendly; no access restrictions; platform-agnostic. | Doesn't prevent copying, only discourages sharing by linking it to the user. |
| Streaming DRM | Content is decrypted in a secure environment on-the-fly (e.g., Widevine). | Very effective for streaming; prevents direct file copying. | Requires constant internet connection; complex to implement. |
| Proprietary Lock-in | Content is tied to a specific hardware/software ecosystem (e.g., Kindle). | Seamless user experience within the ecosystem; boosts platform loyalty. | Limits user freedom; content is not portable to other platforms. |