
Working with sensitive information means that safeguarding your digital documents is paramount. In my work, I've seen firsthand how a single breach can have significant consequences, from financial loss to reputational damage. Ensuring robust digital document portfolio security isn't just about preventing unauthorized access; it's about maintaining trust and compliance with various regulations.
The landscape of digital threats is constantly evolving, making it crucial to adopt proactive and sophisticated security measures. Relying on basic password protection or simple encryption might not be enough anymore. We need to explore a layered approach that covers various aspects of document management and storage.
Table of Contents
Understanding Evolving Threats
The digital realm presents a constant stream of challenges. We face everything from sophisticated phishing attacks designed to steal credentials, to malware that can silently exfiltrate data, and even insider threats from disgruntled employees or accidental data leaks. Understanding these diverse threats is the first step in building effective defenses for your digital document portfolio.
Common Attack Vectors
Attackers often target vulnerabilities in software, exploit human error through social engineering, or leverage weak authentication mechanisms. Keeping software updated and training users on security awareness are foundational, but for advanced protection, we must look beyond these basics. This involves understanding how each threat specifically targets digital assets.
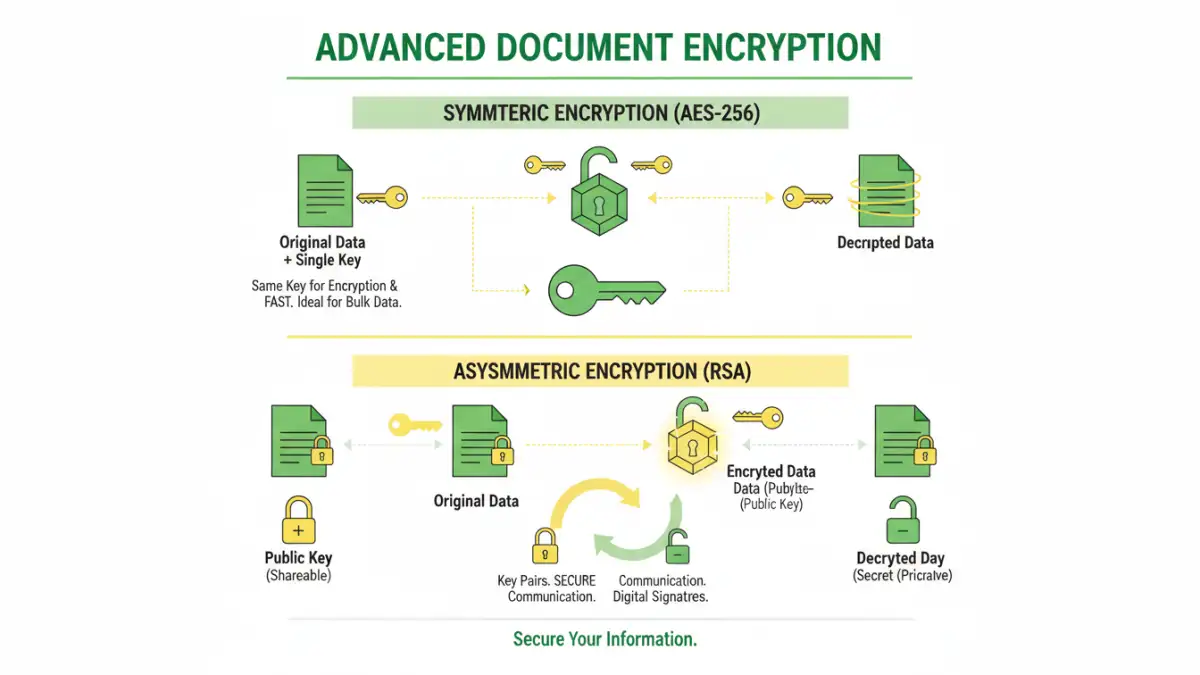
Advanced Encryption Techniques
Encryption is a cornerstone of digital document security. While basic file encryption is common, advanced techniques offer stronger protection. End-to-end encryption ensures that your data is protected from the moment it's created until it's accessed by an authorized recipient, with no intermediary able to decrypt it.
Choosing the Right Encryption Standard
For sensitive documents, AES-256 is the industry standard for symmetric encryption, offering a very high level of security. Asymmetric encryption, using public and private keys, is crucial for secure communication and digital signatures, ensuring both confidentiality and authenticity. My experience shows that implementing strong, standardized encryption protocols significantly reduces the risk of data compromise.
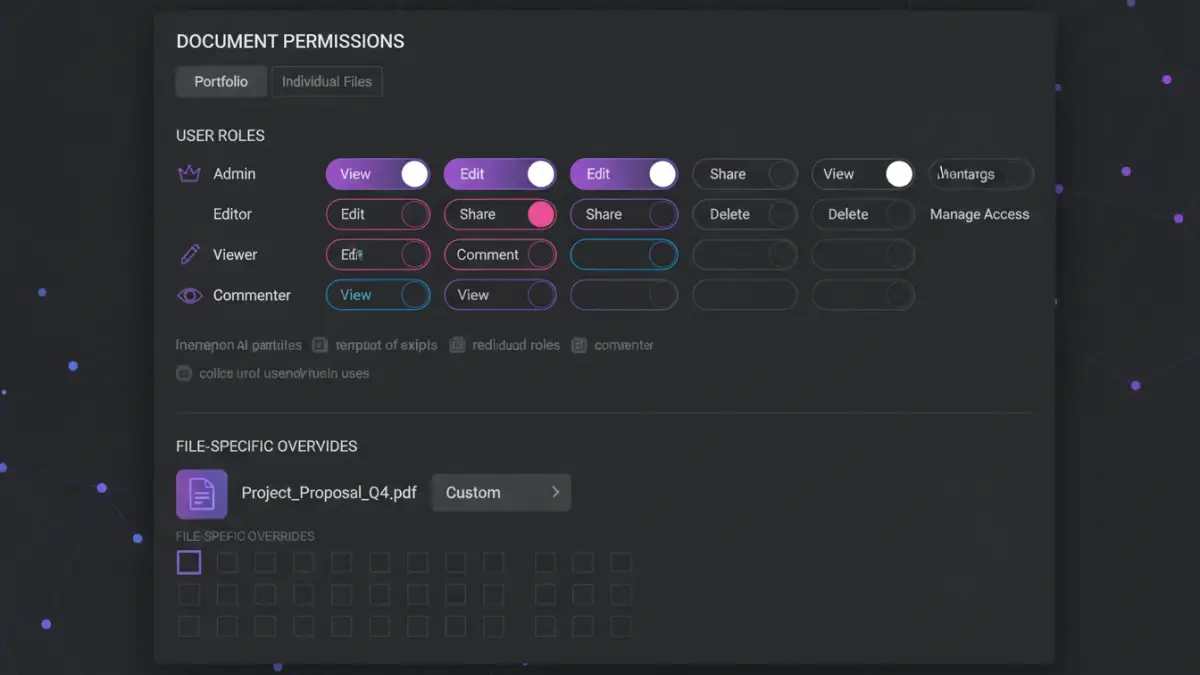
Implementing Granular Access Control
Beyond just encrypting files, controlling who can access what and under what conditions is vital. This involves setting up robust access control policies. Role-based access control (RBAC) is a common method, assigning permissions based on a user's role within an organization.
Least Privilege Principle
The principle of least privilege dictates that users should only have access to the information and resources necessary to perform their job functions. This minimizes the potential damage from compromised accounts or insider misuse. Implementing this principle across your digital document portfolio can prevent unauthorized data exposure.
Secure Storage and Backup Strategies
Where you store your documents and how you back them up are critical components of overall security. Cloud storage solutions offer convenience but require careful configuration to ensure they are secure. Always opt for providers that offer strong encryption at rest and in transit, and enable multi-factor authentication (MFA) on your accounts.
Redundant and Encrypted Backups
Regular, encrypted backups are essential for disaster recovery and protecting against ransomware. Storing backups in multiple locations, including offsite or offline, provides an additional layer of resilience. This ensures that even if one backup location is compromised, your data remains safe.
Ongoing Best Practices
Maintaining digital document portfolio security is not a one-time task; it's an ongoing process. Regularly reviewing access logs, updating security software, and conducting periodic security audits are crucial. Staying informed about emerging threats and security best practices ensures your defenses remain effective.
Comparison Table
| Security Measure | Description | Effectiveness | Implementation Complexity |
|---|---|---|---|
| Basic Password Protection | Sets a password for file access/editing | Low to Moderate | Very Low |
| AES-256 Encryption | Uses a strong, symmetric algorithm | High | Moderate |
| End-to-End Encryption | Data encrypted from sender to receiver | Very High | Moderate to High |
| Role-Based Access Control (RBAC) | Permissions based on user roles | High | Moderate |
| Multi-Factor Authentication (MFA) | Requires multiple verification methods | High | Low to Moderate |
Extra tips before you try to digital document portfolio security
First, confirm what kind of protection you are dealing with. Some PDFs require a password to open (user password), while others only restrict printing/copying/editing (owner password). The safest approach depends on which one you have.
For sensitive documents, prefer offline tools and avoid uploading confidential files to unknown websites. If you must use an online tool, read the privacy policy and delete uploaded files immediately after processing.
- Try a different PDF viewer (some apps cache old permissions)
- Re-download the file (corruption can cause false password errors)
- Check caps lock / keyboard layout for password entry
- Differentiate “permission password” vs “open password” prompts
- If it is not your file, request access from the owner