I once had a project manager in a panic. A key team member had left the company abruptly, leaving behind a critical project plan locked in an encrypted file. The password was nowhere to be found. The question wasn't just *how* to open it, but *should* we? This scenario cuts to the heart of a complex issue that balances necessity against privacy.
Decrypting a file without a key or clear permission isn't just a technical challenge; it's an ethical minefield. The line between legitimate data recovery and a serious breach of trust is often blurry, and making the wrong call can have significant consequences for everyone involved.
Table of Contents
The Core Dilemma: Intent vs. Impact
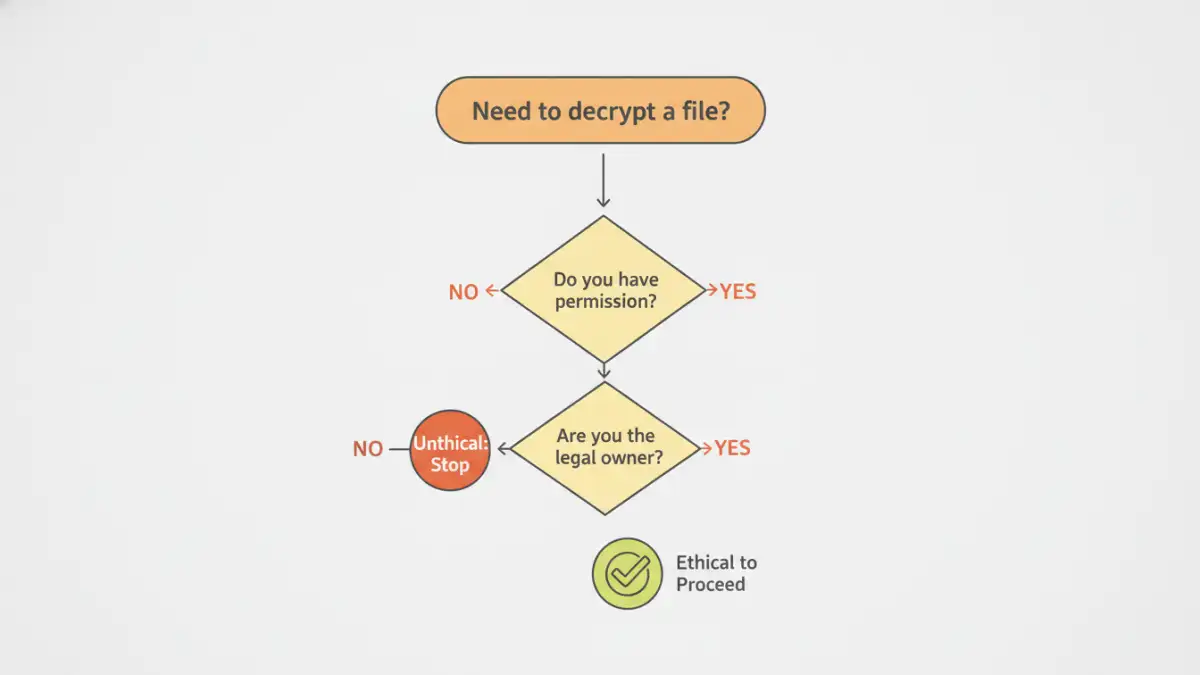
The central question in this debate revolves around your intent. Are you trying to recover company property, access your own forgotten data, or are you trying to snoop on someone else's private information? The 'why' behind your actions is the most critical factor in determining whether the act is ethical.
However, good intentions don't always excuse the impact. Accessing a file, even for a valid reason, can still feel like a violation to the person who encrypted it. This is where formal policies and clear communication become essential tools for any organization.
Understanding File Access Authority
File access authority is a concept that extends beyond simply having the password. It refers to the legitimate right to view or modify data. In a corporate setting, data created for the company on company equipment is generally considered company property. An employee encrypting a work file doesn't necessarily transfer ownership of the data inside it.
However, this authority has limits. It typically doesn't extend to personal files an employee might have stored on a work device, which creates a tricky gray area. Establishing clear and upfront policies on data ownership is the best way to navigate this.
The Importance of Data Decryption Consent
The gold standard is always explicit consent. If you can ask the file's creator for permission and the password, that is the only path that is 100% ethically sound. When that's not possible, you move into a world of justification and risk assessment. Gaining data decryption consent protects both the individual's privacy and the organization from potential legal issues.
When Decryption Might Be Justified

While obtaining consent is ideal, there are situations where decrypting a file without it can be considered necessary and ethical. These cases almost always involve clear, documented authority and a compelling business or legal need.
- Business Continuity: In the scenario with my project manager, the file contained critical business information. Because the work was done for the company, the company had a legitimate claim to access its own data to continue operations. We followed a strict internal protocol that involved documenting the need and getting executive approval before our IT security team intervened.
- Legal and Forensic Investigations: Law enforcement or internal investigators with a legal warrant or clear authority can decrypt files as part of an official investigation into wrongdoing. This process is governed by strict legal rules.
- Personal Data Recovery: If you encrypt your own file and forget the password, you are the owner. Using tools to recover your own data is perfectly ethical. The data belongs to you, and you have complete file access authority.
Crossing the Line: Unethical Decryption
The ethical lines are crossed when the motivation is curiosity, personal gain, or malice. In these instances, decryption becomes a clear violation of privacy boundaries and trust. There is no justification for these actions.
Examples of unethical decryption include accessing a coworker's personal financial spreadsheet saved on a shared server, reading a family member's private journal without their knowledge, or engaging in corporate espionage by stealing and decrypting a competitor's trade secrets. These actions can carry severe legal and professional consequences.
A Framework for Ethical Data Handling
When faced with a locked file and no password, it's crucial to have a process. Rushing to a technical solution without considering the ethics is a mistake. A clear framework helps you make a responsible decision about whether to decrypt files ethically.
- Assess Ownership and Authority: Who owns the data in the file? Is it personal or organizational? Do you have a documented, legitimate claim to access it?
- Evaluate the Necessity: Is accessing this data absolutely critical? Is there any other way to get the information or proceed without it? The bar for necessity should be very high.
- Document Everything: Create a paper trail. Write down the justification, who requested access, who approved it, and why it's necessary. This is crucial for transparency and accountability.
- Choose the Least Intrusive Method: If you must proceed, use a method that is targeted and minimizes collateral privacy invasion. For example, have a trusted, neutral party (like IT security) perform the decryption and extract only the specific data needed.
- Consult Legal or HR: In any ambiguous corporate situation, involve your Human Resources or legal department. They can provide guidance based on company policy and employment law.
Ethical Decryption Scenarios
| Scenario | Ethical Status | Key Consideration | Recommended Action |
|---|---|---|---|
| Accessing your own file after forgetting the password | Ethical | Data Ownership | Proceed with recovery tools. |
| Opening a departed employee's work file for business continuity | Likely Ethical | File Access Authority | Follow company policy, document justification, and get approval. |
| Reading a coworker's encrypted personal folder on a shared drive | Unethical | Privacy Boundaries | Do not attempt. Report to IT if discovered. |
| A legal team accessing files under a court order | Ethical | Legal Mandate | Proceed according to the legal directive. |
| Decrypting a spouse's private diary out of curiosity | Unethical | Data Decryption Consent | Respect their privacy. Do not proceed. |
| Using a found USB drive and decrypting its contents | Unethical | Ownership & Intent | Attempt to return it to the owner without accessing files. |