
The digital age has democratized image creation and sharing, but this ease of access also brings significant challenges in protecting intellectual property. As a software engineer who has spent over a decade building and securing digital assets, I've seen firsthand how easily valuable visual content can be misused. Implementing robust protection measures is no longer optional; it's a necessity for photographers, designers, and businesses alike. Advanced watermarking offers a powerful layer of defense against unauthorized use and copyright infringement.
Table of Contents
Understanding Advanced Watermarking
Watermarking, at its core, is the process of embedding a visible or invisible mark onto an image to identify its owner or convey specific information. While simple visible watermarks (like a logo in a corner) are common, advanced techniques go much further. These methods are designed to be robust, difficult to remove without damaging the image, and often provide additional layers of security for visual media security.
The Goal: Deterrence and Identification
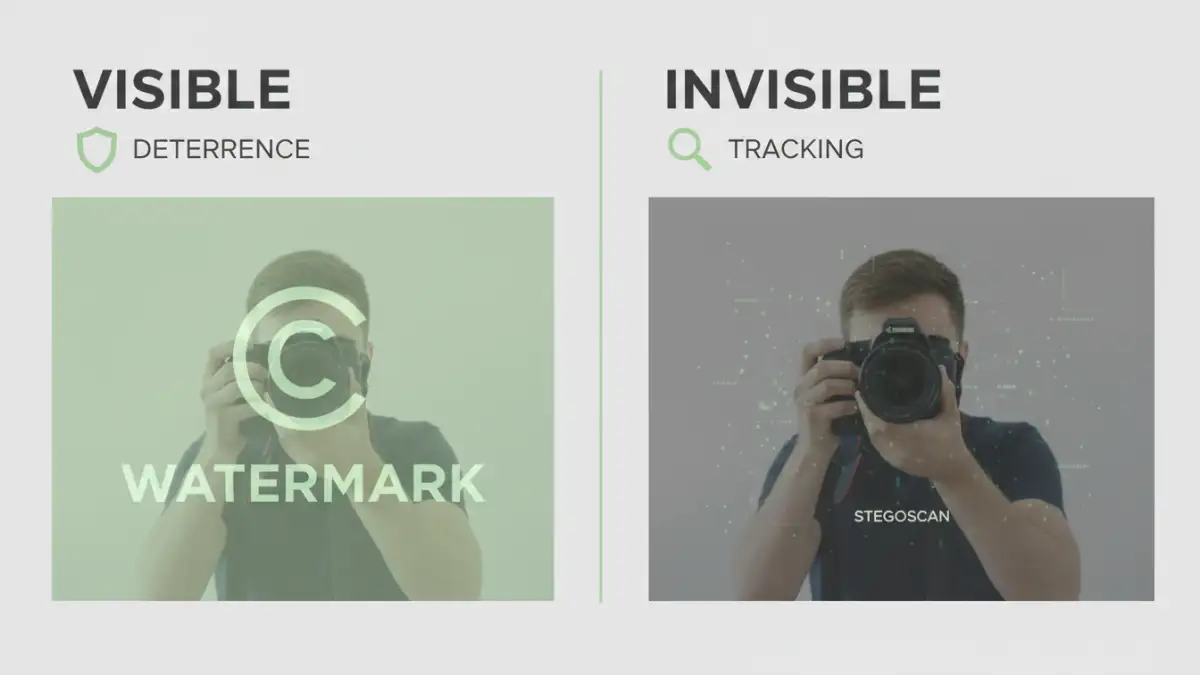
The primary goals of advanced watermarking are deterrence and identification. A well-placed, sophisticated watermark can discourage unauthorized use by making it clear that the image is protected and owned. If an image is still used without permission, the watermark serves as irrefutable proof of ownership, aiding in copyright enforcement and legal action.
Types of Advanced Watermarks

Beyond simple logos, several advanced watermarking techniques offer enhanced security. These can be broadly categorized into visible and invisible types, each with its own strengths and use cases for image file protection.
Visible Watermarks
These are the most straightforward and include semi-transparent logos, text overlays, or patterns. While they can be visually distracting, their primary benefit is immediate deterrence. Advanced visible watermarks might be tiled across the entire image or strategically placed to be hard to crop out without significant image alteration. Some systems even allow for dynamic watermarking, where information like the viewer's IP address or timestamp is embedded.
Invisible (Steganographic) Watermarks
Invisible watermarks embed data directly into the image pixels in a way that is imperceptible to the human eye. This is often achieved using steganographic techniques, where information is hidden within the least significant bits (LSBs) of pixel data or through more complex transformations like the Discrete Cosine Transform (DCT). These are incredibly difficult to detect and remove without specialized software, making them ideal for tracking image distribution and verifying authenticity.
Implementation Strategies
Choosing the right watermarking strategy depends on the specific needs and the type of images being protected. My experience suggests that a multi-layered approach often yields the best results for comprehensive digital image security.
Batch Processing and Automation
For large collections of images, manual watermarking is impractical. Implementing automated workflows using scripting or specialized software is crucial. This ensures consistency across all assets and saves significant time. Many professional photo editing suites and dedicated watermarking tools offer batch processing capabilities.
Embedding Metadata
Beyond pixel-level embedding, watermarks can also be embedded within the image's metadata (EXIF data). This includes fields for copyright notices, creator information, and usage rights. While easily stripped by some tools, embedding this data is a fundamental step and can be combined with other methods for a more robust solution.
Detection and Enforcement
Once watermarked, the next challenge is detecting unauthorized use and enforcing your rights. This is where the choice of watermark significantly impacts your ability to act.
Automated Detection Services
Several online services specialize in scanning the web for unauthorized use of images. They use sophisticated algorithms to identify images that match your watermarked originals, even if the watermark itself has been partially altered. This proactive approach helps catch infringements early.
Legal Ramifications
When an infringement is detected, the embedded watermark provides the necessary evidence for legal action. This could range from sending a cease-and-desist letter to pursuing damages in court. The robustness and visibility of the watermark can significantly influence the strength of your legal case.
Best Practices for Image File Protection
To maximize the effectiveness of your watermarking strategy and ensure strong image file protection, consider these best practices. They are critical for maintaining control over your visual assets in the digital landscape.
- Choose the Right Type: Select visible watermarks for deterrence and invisible ones for tracking and authentication. Often, a combination is best.
- Placement Matters: For visible watermarks, place them strategically to cover important parts of the image and make them difficult to remove without damage. Tiling is often effective.
- Consider Intensity: Visible watermarks should be noticeable enough to deter but not so overpowering that they ruin the aesthetic of the image.
- Use Strong Algorithms: For invisible watermarks, opt for robust algorithms that are resistant to common image manipulations.
- Regularly Audit: Periodically check for unauthorized usage and update your watermarking strategy as needed.
- Educate Your Audience: Clearly state your copyright and usage policies to inform users about your protection measures.
Comparison Table: Watermarking Techniques
| Method | Pros | Cons | Best For |
|---|---|---|---|
| Simple Visible Logo | Easy to implement, direct deterrence | Easily cropped or removed, can be distracting | Quick branding, basic protection |
| Tiled Visible Pattern | Harder to remove, covers entire image | Can be visually intrusive, less subtle | High-traffic images, stock photos |
| Invisible (Steganographic) | Imperceptible, robust against manipulation | Requires specialized software for detection, no direct deterrence | Copyright tracking, authenticity verification |
| Metadata Embedding | Non-intrusive, standard practice | Easily stripped, not visible proof on image itself | Basic copyright info, creator attribution |