
A few years ago, a design agency I was consulting for discovered their confidential mockups were being shared online without credit. This incident highlighted a major gap in their security strategy. While they used passwords and access controls, they had no way to trace the source of the leak or prove ownership once a file was out in the wild. This is where digital watermarking becomes an essential tool.
Unlike encryption, which locks a file, a watermark acts as a persistent identifier. It travels with the document, offering a different but complementary form of security. It's about accountability, ownership, and traceability—critical components for any comprehensive plan to protect document security.
Table of Contents
What is Digital Watermarking?
At its core, digital watermarking is the process of embedding information into a digital file, such as an image, video, or PDF. This embedded information, the 'watermark,' is typically imperceptible or unobtrusive but can be detected by specialized software. It serves as a digital signature or fingerprint for that specific piece of content.
I often explain it to clients by comparing it to the physical watermarks on currency. You might not see it at first glance, but it's there, proving authenticity and origin. A digital watermark does the same for your files, providing a persistent layer of copyright protection and traceability.
Visible vs. Invisible Watermarks
Watermarks generally fall into two categories. Visible watermarks are easy to spot—think of a company logo or a 'DRAFT' text overlay on a document. Their primary function is deterrence. When someone sees a visible watermark, they are immediately aware that the content is protected and monitored, which discourages unauthorized sharing.
Invisible watermarks, on the other hand, are hidden within the file's data. They are not meant to be seen by the naked eye. Their strength lies in forensics. If a watermarked file is leaked, you can use software to read the hidden data, which might reveal who originally accessed the file or when it was downloaded. This is invaluable for tracking leaks and enforcing accountability.
How Watermarks Enhance Document Security

Watermarks are not a replacement for encryption or access controls, but they fill a crucial security gap. Once an authorized user decrypts and accesses a file, traditional security measures end. The user can then share that file freely. A watermark, however, stays with the document wherever it goes.
The primary security benefits include proving ownership, deterring theft, and tracking distribution. For creative professionals, a watermark is a clear statement of copyright. For corporations, a dynamic watermark that includes the viewer's name and timestamp can pinpoint the source of a data leak with precision. This makes it a key tool for secure image sharing and document handling.
Deterring Unauthorized Sharing
The psychological impact of a visible watermark is powerful. When a document is clearly marked with a user's name, email, or IP address, that individual is far less likely to share it illicitly. They know that if the document surfaces elsewhere, it will be traced directly back to them. This personal accountability is a simple yet highly effective deterrent.
I helped a financial services firm implement this for their research reports. They started adding a dynamic PDF watermark with the client's name to each report. Almost overnight, instances of their premium content appearing on public forums dropped to zero.
Types of Digital Watermarks and Their Applications
Beyond the visible/invisible classification, watermarks can be static or dynamic. A static watermark is the same for every copy of a document, like a company logo. This is great for general copyright protection.
A dynamic watermark is far more powerful for security. It changes based on the user, time of access, or other variables. For example, in a secure data room, each user who downloads a sensitive file could get a version with a unique, invisible watermark tied to their identity. This ensures that every single copy is traceable.
This technique is common in the media industry for pre-release movie screeners. Each screener sent to critics has a unique watermark, ensuring that any leak can be traced back to the specific individual who received that copy.
Implementing a Watermarking Strategy
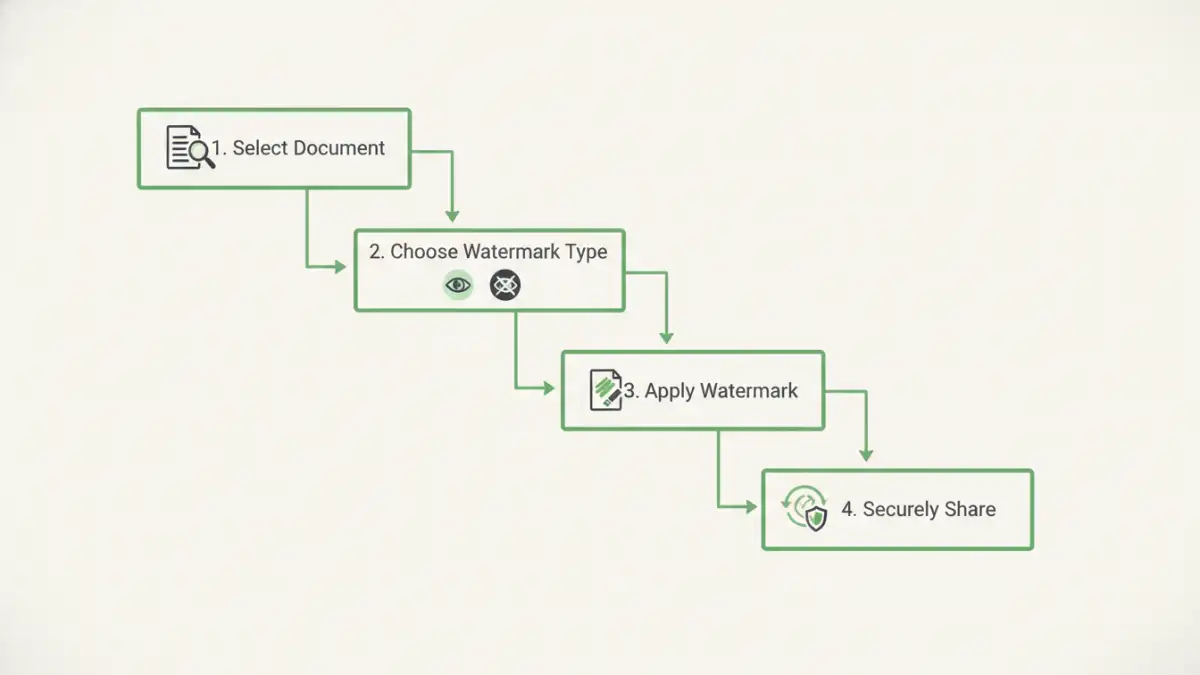
Getting started with digital watermarking doesn't have to be complicated. The first step is to identify which documents need protection and what you want to achieve. Are you trying to prevent casual sharing, or do you need a robust system to trace high-stakes corporate leaks?
For general purposes like protecting a portfolio, many image and PDF editing tools (like Adobe Photoshop or Acrobat) have built-in features to add a visible text or logo watermark. For more advanced needs, dedicated watermarking software and services offer features like invisible watermarking, dynamic generation, and batch processing.
When choosing a solution, consider its robustness. How easily can the watermark be removed? A simple transparent logo can sometimes be edited out, whereas a sophisticated invisible watermark embedded in the file's noise pattern is nearly impossible to remove without damaging the file itself.
Watermarking Method Comparison
| Watermark Type | Primary Goal | Pros | Cons |
|---|---|---|---|
| Visible Static Watermark | Deterrence & Branding | Easy to apply; clearly states ownership. | Can be visually distracting; potentially removable with editing software. |
| Visible Dynamic Watermark | Personal Accountability | Excellent deterrent; links a copy to a specific user. | Requires a system to generate unique watermarks for each user/download. |
| Invisible Static Watermark | Ownership Proof | Doesn't alter the appearance of the content; provides hidden proof. | Doesn't deter sharing as users are unaware of it; requires software to detect. |
| Invisible Dynamic Watermark | Leak Tracking & Forensics | The most secure option for tracing leaks back to a source. | Complex to implement; requires specialized software for embedding and detection. |