
Sharing multiple images securely can become a cumbersome task, especially when dealing with sensitive visual data. Whether you're distributing client proofs, internal project visuals, or personal photos, ensuring they reach the intended recipients without unauthorized access is paramount. Over my years in software engineering, I've encountered numerous scenarios where standard file sharing methods fall short, leading to potential privacy breaches or data compromises. This is where mastering batch processing for image security becomes not just a convenience, but a necessity.
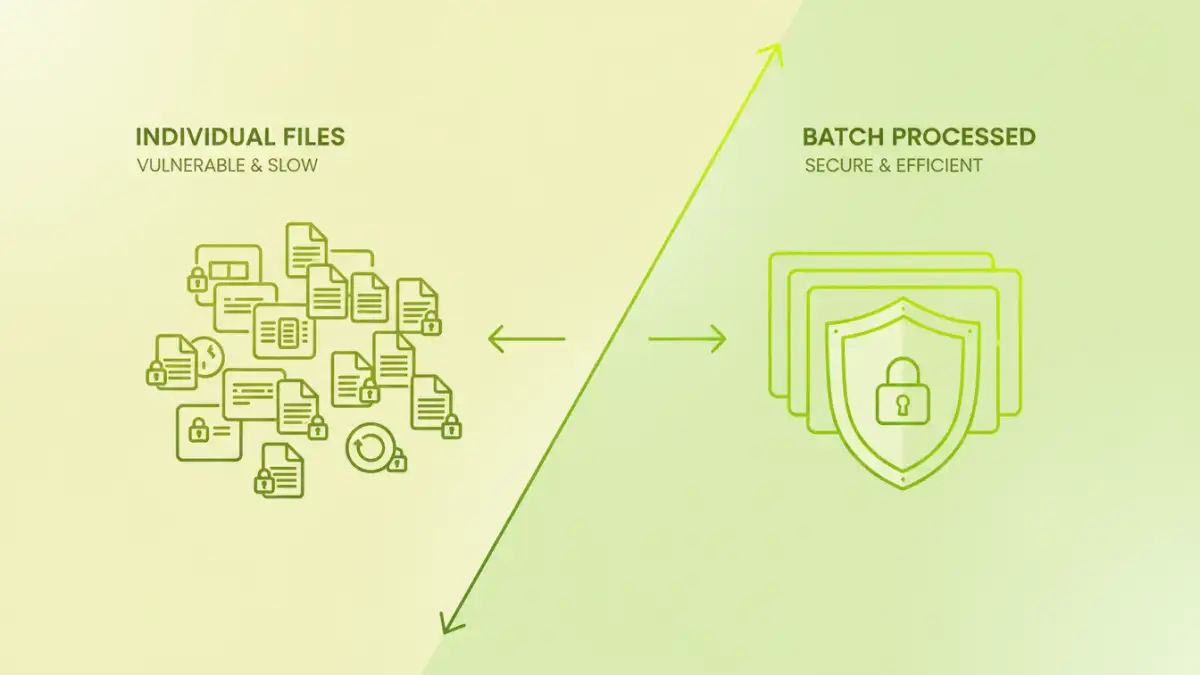
The challenge often lies in applying security measures efficiently across a large volume of files. Manually encrypting or password-protecting each image individually is time-consuming and prone to errors. Fortunately, with the right tools and techniques, you can streamline this process significantly, ensuring both the integrity of your files and the privacy of your information during bulk image distribution.
Table of Contents
Understanding Image Security Needs
Before diving into methods, it's crucial to understand why securing images is important. Images can contain sensitive information, from proprietary designs and confidential client data to personally identifiable information (PII) embedded within the metadata. Unauthorized access to these visuals can lead to intellectual property theft, privacy violations, and reputational damage. Therefore, implementing robust file safety measures is essential.
Why Secure Images?
Images might seem harmless, but they can be vectors for data leakage. Consider architectural plans, medical scans, or even personal photos containing identifiable landmarks or individuals. Ensuring secure document sharing extends to all forms of digital assets, including image files, to maintain trust and compliance with data protection regulations.
Benefits of Batch Processing

Batch processing allows you to apply a specific action or set of actions to multiple files simultaneously. When it comes to image security, this translates to significant time savings and increased efficiency. Instead of tedious manual work, you can encrypt, compress, or apply watermarks to hundreds or thousands of images with just a few clicks or commands.
This automation is key for any professional workflow involving bulk image distribution. It minimizes the risk of human error, ensuring that every file in the batch receives the intended security treatment. This consistency is vital for maintaining a high standard of file safety across your entire dataset.
Methods for Secure Batch File Sharing
Several approaches can be employed for securing batches of images. The method chosen often depends on the level of security required, the type of files, and your technical comfort level. Understanding these options allows for a tailored approach to your specific needs for secure batch file sharing.
Encryption and Password Protection
One of the most common methods is encrypting the files or placing them within a password-protected archive. Tools can often automate the creation of password-protected ZIP or RAR files, applying a single password to the entire batch. This is effective for preventing casual access but may not withstand sophisticated decryption attempts if weak passwords are used.
Secure Cloud Storage and Sharing Platforms
Many cloud storage services offer robust security features, including end-to-end encryption and granular access controls. You can upload your batch of images and then share them via secure links with specific permissions. Some platforms also allow for time-limited access or password protection on shared links, adding another layer of file safety.
Watermarking and Metadata Stripping
While not strictly encryption, watermarking can deter unauthorized use by visibly marking ownership. Additionally, stripping EXIF metadata from images can remove potentially sensitive information like location data, camera models, and timestamps, enhancing privacy before bulk image distribution.
Tools and Software Solutions
Leveraging the right software is crucial for efficient batch processing. Many applications are designed to handle these tasks, ranging from simple utilities to professional-grade software.
Command-Line Utilities
For users comfortable with the command line, tools like `7-Zip` (for creating password-protected archives) or `ImageMagick` (for batch operations like watermarking or metadata stripping) offer powerful automation capabilities. Scripting these commands allows for highly customizable and repeatable workflows.
Dedicated Batch Processing Software
There are numerous third-party applications specifically designed for batch image processing. These often provide user-friendly interfaces for applying various security measures, resizing, watermarking, and converting images in bulk. Look for software that supports encryption or secure archiving features.
Best Practices for File Safety
Beyond the tools, adopting good practices is fundamental for maintaining file safety. Always use strong, unique passwords for encrypted archives. Regularly update your security software and operating system to patch vulnerabilities. Educate yourself and your team on potential threats and secure sharing protocols.
Consider the principle of least privilege: only grant the necessary access levels to recipients. For highly sensitive data, explore more advanced encryption methods like PGP or secure file transfer protocols (SFTP). Combining multiple layers of security often provides the most robust protection for your bulk image distribution needs.
Comparison Table: Batch Security Methods
| Method | Pros | Cons | Best For |
|---|---|---|---|
| Password-Protected Archives (ZIP/RAR) | Widely compatible, simple to implement, single password for many files | Password strength is critical, can be vulnerable to brute-force attacks if weak passwords are used, metadata may remain | General secure document sharing of multiple files where strong encryption isn't the absolute top priority |
| Secure Cloud Sharing Links | Convenient for recipients, granular access controls, often includes encryption in transit and at rest | Reliance on third-party provider's security, potential privacy concerns with some providers, requires internet access | Collaborative projects, sharing with external parties, controlled access |
| Batch Watermarking & Metadata Stripping | Deters unauthorized use, removes sensitive metadata, useful for public distribution | Does not prevent access to the image content itself, watermarks can be removed with advanced tools | Protecting images from theft or misuse when sharing publicly or with many parties |
| Dedicated Batch Encryption Software | High level of security, robust encryption algorithms, automation features | May require purchase, learning curve for advanced features, software installation needed | High-security requirements, frequent batch operations, sensitive data protection |