
When you purchase or stream digital content, from movies and music to e-books and software, you might encounter restrictions on how you can use it. These limitations are often enforced by a system designed to protect the intellectual property of content creators and distributors. This system is known as digital rights management, or DRM.
As someone who has worked on various software projects involving content distribution and access control, I've seen firsthand how crucial these mechanisms are for businesses to monetize their creations while trying to prevent piracy. It’s a complex balance between protecting assets and providing a good user experience.
Table of Contents
What is Digital Rights Management (DRM)?
At its core, digital rights management is a set of technologies and policies used to control the use, modification, and distribution of copyrighted digital works. The primary goal is to prevent unauthorized copying, sharing, or usage of media files, thereby protecting the interests of content owners.
Think of it as a digital lockbox for your media. It ensures that only authorized individuals can access and use the content, and often dictates specific terms of use, such as how many devices it can be installed on or whether it can be shared.
The Purpose of Copyright Control
DRM is intrinsically linked to copyright control. It provides a technical means to enforce the legal rights granted by copyright law. Without effective methods like DRM, enforcing these rights in the digital realm would be significantly more challenging, potentially leading to widespread piracy and reduced incentives for creators to produce new content.
How Does DRM Work?
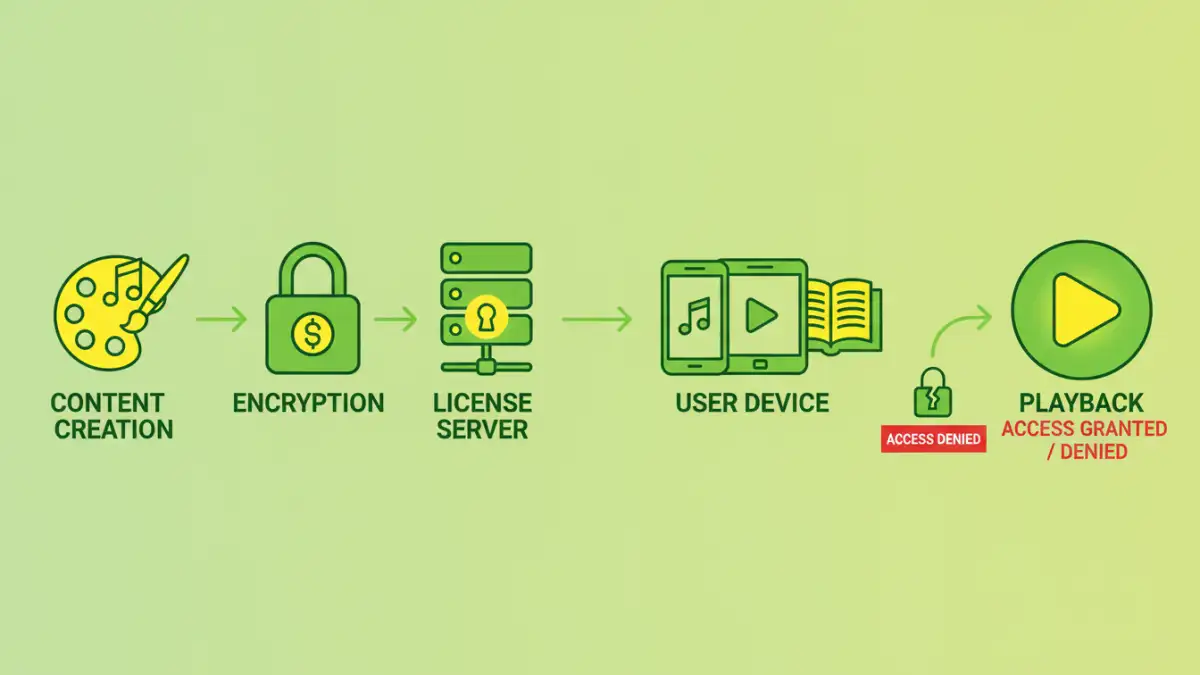
DRM systems typically involve several components working together. This usually includes encryption of the media file, a license server that issues access tokens, and client software that enforces the usage rules. When you try to access a DRM-protected file, your device's software communicates with the license server.
If your request is valid and you have the proper license, the server grants permission, often through a unique key or token. This key then allows your software to decrypt and play or view the content according to the predefined rules. These rules can limit playback to specific devices, prevent screenshots, or restrict the duration of access.
Common DRM Technologies and Techniques
Several methods are employed under the umbrella of DRM. Encryption is fundamental, scrambling the data so it's unreadable without the correct decryption key. This key is usually tied to a specific user, device, or session.
Another common technique is watermarking, which embeds hidden information within the media file to identify its origin or owner, even if it's copied. Digital fingerprinting is similar, creating a unique identifier for each copy distributed, making it traceable. Some systems also employ access control mechanisms that limit functionality, such as preventing printing or copying.
DRM Explained in Practice
For example, when you buy a movie on a digital store, you're often purchasing a license to view it, not outright ownership. The file itself is encrypted, and your account or device is authorized to decrypt and play it. If you try to play it on an unauthorized device, the DRM system will block access, even if you have the file.
Benefits of DRM
For content creators and distributors, DRM offers significant advantages. It allows for controlled distribution, helps prevent piracy, and enables new business models like subscriptions and pay-per-view. This helps ensure that creators are compensated for their work, fostering continued innovation and production of high-quality content.
DRM can also provide consumers with access to a wider range of content through legitimate channels, often at more accessible price points than physical media. It can facilitate convenient access across multiple authorized devices for subscription services.
Challenges and Criticisms of DRM
Despite its benefits, DRM is a contentious topic. Critics argue that it can be overly restrictive, hindering legitimate uses of purchased content, such as fair use for education or backup copies for personal use. It can also create compatibility issues across different devices and platforms, leading to a frustrating user experience.
Furthermore, some DRM implementations have been criticized for their security vulnerabilities, with hackers often finding ways to circumvent them. This raises questions about the effectiveness and necessity of some DRM measures, especially when they inconvenience legitimate users.
Alternatives to DRM
Recognizing the drawbacks of strict DRM, many content providers are exploring alternative strategies. A popular approach is a relaxed DRM model, which might involve content watermarking for traceability rather than outright encryption. Another strategy is to focus on providing superior value and user experience through legitimate channels, making piracy less appealing.
Building strong customer relationships and offering flexible licensing options can also be effective. Ultimately, the goal is to find a balance that protects content while respecting user freedoms and fostering a healthy digital ecosystem.
Comparison Table: DRM Approaches
| Approach | Description | Pros | Cons | Best For |
|---|---|---|---|---|
| Strict Encryption DRM | Scrambles content, requires license key for playback on authorized devices/platforms. | Strongest protection against unauthorized copying. | Can be restrictive, compatibility issues, potential user frustration. | High-value content, Hollywood movies, AAA game titles. |
| Watermarking/Fingerprinting | Embeds hidden identifiers in content to trace unauthorized distribution. | Less restrictive for users, preserves content quality, allows legitimate sharing. | Does not prevent copying, relies on post-distribution tracking. | Music, news articles, user-generated content. |
| No DRM (Open Access) | Content is freely available for copying and distribution, often under permissive licenses (e.g., Creative Commons). | Maximum accessibility, encourages wide dissemination, fosters community. | Potential for piracy, requires alternative revenue models (e.g., donations, premium services). | Open-source software, academic research, creative commons works. |