
Working in or with the public sector means handling data that isn't just sensitive—it's foundational to public trust and national security. A breach isn't just a financial problem; it can erode citizen confidence and disrupt essential services. That's why simply password-protecting a document is no longer sufficient. We need a comprehensive strategy for protecting information at every stage of its lifecycle.
The responsibility for citizen data protection is immense, and getting it right requires more than just buying a piece of software. It involves understanding the principles, implementing the right tools, and fostering a culture of security. From health records to infrastructure plans, the integrity of this data is paramount.
Table of Contents
Why Encryption is Critical for Government Agencies
For government bodies, data isn't just an asset; it's a liability if not properly managed. The primary goal of encryption is to render data unreadable and unusable to anyone without the proper authorization key. This is the last and strongest line of defense in a multi-layered security approach.
A few years ago, I consulted on a project for a municipal agency that suffered a ransomware attack. Their backups were intact, but because the source files weren't encrypted at rest, the attackers exfiltrated and threatened to release sensitive citizen information. This incident highlighted that preventing access is only half the battle; making the data itself useless to attackers is the other, equally critical half.
Understanding the Risks of Unencrypted Data
The risks extend far beyond simple data loss. For public sector organizations, a breach can lead to identity theft, foreign espionage, disruption of critical services, and significant legal and financial penalties. Strong government file security is a matter of national security and public safety.
Key Compliance Frameworks to Consider
Compliance is a major driver for robust encryption. Regulations like GDPR in Europe, HIPAA for healthcare data in the US, and various state-level privacy laws mandate specific security controls. Adhering to standards from NIST (National Institute of Standards and Technology) also provides a strong framework for implementing effective security measures.
Core Encryption Principles for Public Data

Effective encryption isn't just about applying an algorithm; it's about protecting data throughout its journey. This is generally broken down into two states: data at rest and data in transit.
Protecting Data at Rest
Data at rest is information that is not actively moving between devices or networks. This includes files saved on a server, a laptop's hard drive, a USB stick, or in cloud storage. Full-Disk Encryption (FDE) tools like BitLocker (Windows) and FileVault (macOS) are excellent for securing entire devices. For specific folders or files, file-level encryption provides more granular control.
Securing Data in Transit
Data in transit is information moving between locations, such as being sent over email or accessed from a cloud server. This is where protocols like TLS (Transport Layer Security) are essential for securing the communication channel. For file transfers, using SFTP (Secure File Transfer Protocol) or end-to-end encrypted messaging platforms ensures the data is protected from eavesdropping while on the move.
Practical Encryption Methods for Public Agencies
Choosing the right tool depends on the specific use case, from securing an individual employee's laptop to enabling secure collaboration between departments. A multi-pronged approach is always the most effective strategy for public sector file encryption.
Full-Disk Encryption (FDE)
This should be the default for all government-issued laptops and mobile devices. FDE encrypts the entire storage drive, meaning that if a device is lost or stolen, the data on it is completely inaccessible without the user's credentials. It's a foundational layer of security that protects against physical theft.
End-to-End Encrypted (E2EE) Collaboration Platforms
When sharing files and messages, E2EE platforms ensure that only the sender and intended recipient can read the information. The service provider itself cannot access the unencrypted data. This is crucial for inter-agency communication or sharing sensitive documents with external partners, ensuring complete confidentiality.
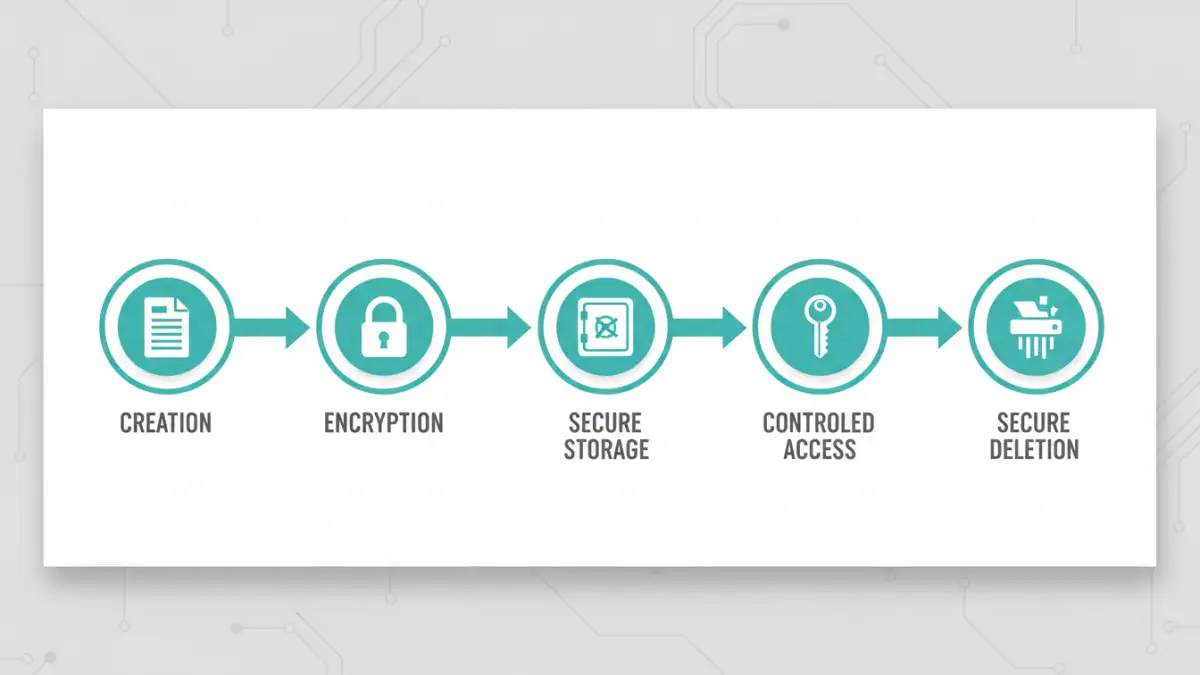
Building a Secure File Management Lifecycle
Encryption is just one part of a larger strategy. A secure file lifecycle considers how data is handled from creation to deletion, ensuring security is maintained at every step.
Robust Access Control and Key Management
Encryption is only as strong as the security of its keys. Implementing a robust key management system is critical. This includes policies for key generation, storage, rotation, and revocation. Furthermore, access should be granted based on the principle of least privilege—users should only have access to the specific data they need to perform their jobs.
Secure Deletion and Data Retention
When a file is no longer needed, simply deleting it isn't enough. The data can often be recovered. Secure deletion techniques, also known as cryptographic erasure or shredding, ensure that the data is permanently destroyed. This must be paired with a clear data retention policy that dictates how long specific types of information should be kept before being securely disposed of.
Data Encryption Standards Comparison
Choosing the right standard is crucial for ensuring the long-term security of sensitive public files. Here’s a look at some of the most common and trusted standards.
| Standard | Type | Key Size(s) | Best Use Case |
|---|---|---|---|
| AES (Advanced Encryption Standard) | Symmetric | 128, 192, 256-bit | Securing data at rest (files, databases, full-disk). The global standard. |
| RSA (Rivest-Shamir-Adleman) | Asymmetric | 2048, 4096-bit | Securing data in transit (TLS/SSL), digital signatures, secure key exchange. |
| ECC (Elliptic Curve Cryptography) | Asymmetric | 256, 384-bit | Mobile devices and IoT where computational power is limited. Offers similar strength to RSA with smaller key sizes. |
| Twofish | Symmetric | Up to 256-bit | An alternative to AES, often used in file encryption software. Known for its speed and flexibility. |
| Serpent | Symmetric | 128, 192, 256-bit | Considered highly secure, though slightly slower than AES. Used in high-security applications. |