
Handling sensitive citizen data is one of the most critical responsibilities for any public sector organization. A few years ago, I was brought in to consult on a project where a municipal agency had a close call with a data leak. An unencrypted drive containing tax records was misplaced, and it was pure luck that it was recovered before falling into the wrong hands. This incident served as a stark reminder that good intentions aren't enough; robust, enforceable security protocols are essential.
The foundation of modern data security, especially in government, is encryption. It’s not just a technical checkbox; it's a fundamental pillar of public trust. When we talk about protecting files containing everything from social security numbers to healthcare information, we're really talking about protecting people. Let's walk through the principles and practices that make this possible.
Table of Contents
Why Encryption is Non-Negotiable for Public Data
In the public sector, data isn't just data—it's a collection of individual lives, private details, and sensitive information. The stakes are incredibly high. A breach can lead to identity theft, financial fraud, and a catastrophic loss of public confidence that can take years, if not decades, to rebuild. This is where citizen data protection becomes a core mission.
Regulatory compliance is another major driver. Frameworks like HIPAA for healthcare data, CJIS for criminal justice information, and GDPR for citizen data in Europe (and its equivalents worldwide) mandate strict security controls. Encryption is almost always a specified requirement. Failing to comply doesn't just risk a data breach; it can result in severe financial penalties and legal action.
Core Encryption Concepts for Government Agencies

To implement encryption effectively, it's helpful to understand a few basic concepts. You don't need to be a cryptographer, but knowing the landscape helps in making informed decisions about tools and policies. From my experience, teams that grasp these fundamentals build much more resilient systems.
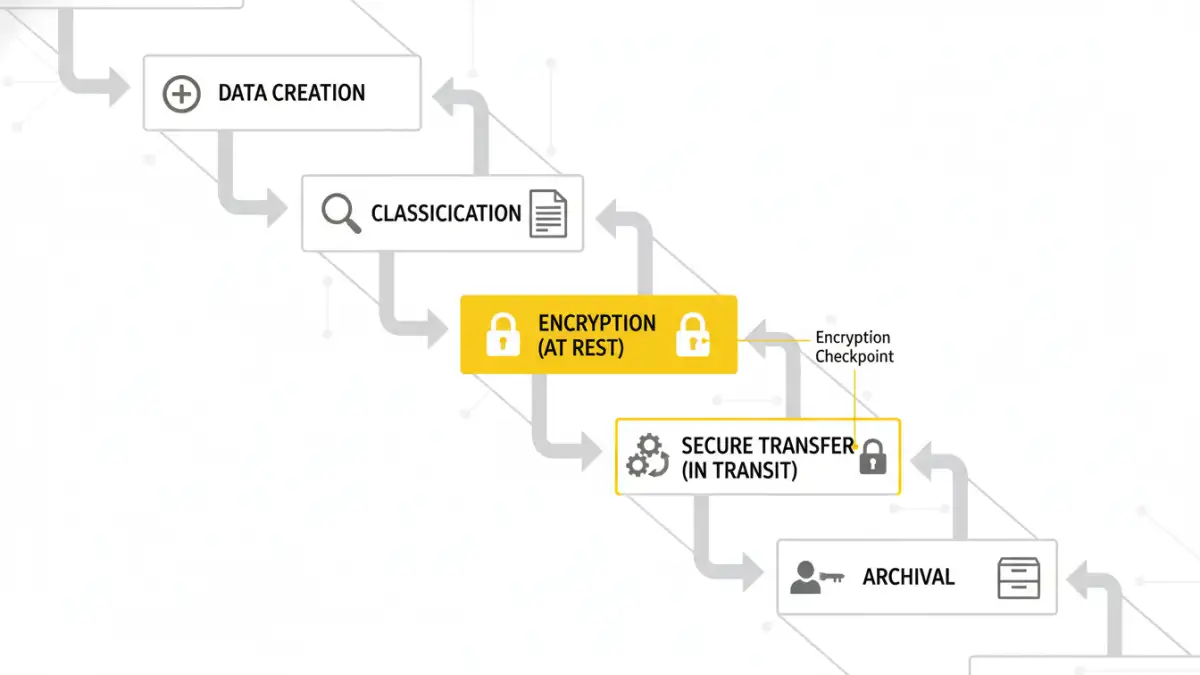
Encryption at Rest vs. In Transit
Data has two primary states: at rest and in transit. 'Data at rest' refers to information stored on a physical or virtual medium, like a hard drive, a server in a data center, or a cloud storage bucket. Think of it as a document locked in a safe. Full-disk encryption tools like BitLocker (Windows) and FileVault (macOS) are common solutions for protecting data at rest.
'Data in transit' is data actively moving from one location to another, such as being sent over a network, the internet, or between applications. This is like using an armored truck to move valuables. Protocols like TLS (Transport Layer Security), which powers HTTPS, and SFTP (Secure File Transfer Protocol) are designed to protect data in transit, ensuring it can't be intercepted and read by unauthorized parties.
Symmetric vs. Asymmetric Encryption
Symmetric encryption uses a single key to both encrypt and decrypt information. It's fast and efficient, making it ideal for encrypting large volumes of data, like an entire hard drive. The challenge, however, is securely sharing that single key with the intended recipient. If the key is intercepted, the security is compromised.
Asymmetric encryption, also known as public-key cryptography, uses a pair of keys: a public key and a private key. The public key can be shared freely and is used to encrypt data, but only the corresponding private key can decrypt it. This method is slower but solves the key-sharing problem, making it perfect for secure communications and digital signatures.
Practical Encryption Strategies and Tools
Theory is great, but implementation is what counts. Effective government file security relies on a multi-layered approach using reliable tools. The goal is to make encryption a seamless part of the workflow, not a cumbersome obstacle that employees try to bypass.
For individual workstations and laptops, enabling built-in full-disk encryption is the first line of defense. For shared network drives and cloud storage, you need more granular control. This is where enterprise-grade solutions come in. These platforms often provide centralized key management, detailed audit logs (who accessed what, when), and role-based access controls. This ensures that only authorized personnel can decrypt and view specific files.
When sharing files externally with other agencies or contractors, using a secure, managed file transfer (MFT) solution is far superior to email. MFT systems enforce encryption in transit, provide delivery confirmation, and often include features for scanning files for malware before they are downloaded. This level of control is crucial for maintaining a secure data perimeter.
Establishing a Secure File Handling Policy
Technology alone is never the complete answer. The strongest encryption algorithm is useless if an employee accidentally emails a sensitive file to the wrong person. A comprehensive policy, coupled with continuous training, is what ties everything together. I've seen organizations with cutting-edge tools fail because their human processes were weak.
A strong policy should clearly define a few key areas. First is data classification: categorizing data based on its sensitivity (e.g., Public, Internal, Confidential, Restricted). This dictates the level of encryption and handling required for each file type. Second is access control, based on the principle of least privilege—employees should only have access to the data absolutely necessary to perform their jobs.
Finally, the policy must outline procedures for key management and incident response. Who has the authority to manage encryption keys? What is the process for revoking access when an employee leaves? And what are the immediate steps to take if a potential breach is detected? Answering these questions before a crisis occurs is the hallmark of a mature security posture. The right approach to public sector file encryption integrates technology, policy, and people.
Comparison of Common Data Encryption Standards
| Standard | Key Type | Key Lengths (bits) | Common Use Case |
|---|---|---|---|
| AES (Advanced Encryption Standard) | Symmetric | 128, 192, 256 | Securing data at rest (files, disks) and in transit (TLS). The U.S. government standard. |
| RSA (Rivest-Shamir-Adleman) | Asymmetric | 2048, 4096 | Digital signatures, secure key exchange, and data in transit. |
| Triple DES (3DES) | Symmetric | 112, 168 | Legacy systems. Being phased out in favor of AES due to smaller key size and slower speed. |
| Twofish | Symmetric | Up to 256 | A flexible and fast alternative to AES, often used in security software and hardware. |