
Working with password-protected documents can be frustrating, especially when you've forgotten the password or need to access a file shared by a colleague. OpenDocument files, commonly used by LibreOffice and OpenOffice, are no exception. While encryption is vital for protecting sensitive information, it can become a barrier if not managed properly.
My experience has shown that the need to access these secured files often arises from legitimate reasons, like regaining access to your own lost password-protected work or helping a team member. It's crucial to approach this task with a clear understanding of the security implications and the available methods, always prioritizing data integrity and ethical considerations.
Table of Contents
Understanding OpenDocument Security
OpenDocument files (.odt, .ods, .odp) can be protected using password encryption. This feature is designed to prevent unauthorized access to the content within the document. The strength of this protection can vary depending on the software version and the encryption algorithm used.
When a password is set, the file's content is scrambled, and a specific key derived from the password is required to decrypt and view it. Without the correct password, the data remains inaccessible, highlighting the importance of remembering or securely storing it.
How Encryption Works
The encryption process typically involves transforming the readable document data into an unreadable format using a secret key. This key is generated based on the password you set. When you attempt to open the document, the software uses the provided password to derive the same key and reverse the transformation, making the document readable again.
Different versions of OpenDocument software may employ varying encryption standards. Older versions might use weaker encryption methods, making them potentially more susceptible to brute-force attacks or recovery tools. Newer versions generally implement stronger, more secure encryption algorithms.
Common Methods for Password Removal

Accessing a password-protected OpenDocument file without the password can be challenging, and the effectiveness of different methods varies greatly. It's important to understand that attempting to bypass security on files you don't own or have permission to access is unethical and potentially illegal.
For files where you have legitimate access but have forgotten the password, several approaches can be explored. These range from simple workarounds to more technical solutions, often depending on the specific type of OpenDocument file and the encryption method used.
The 'Owner' Password Bypass (for older versions)
In some older versions of OpenDocument software, there was a distinction between an 'owner' password (which could restrict editing or printing) and a document content password. If the file was only protected by an 'owner' password and not a full content encryption, certain text editors or conversion tools might have been able to access the content by ignoring these restrictions.
This method is largely obsolete with modern encryption standards that apply a single, strong password to the entire document's content. It's less of a password removal technique and more of a legacy vulnerability that is generally no longer applicable.
Using Online Password Recovery Tools
Several online services claim to remove passwords from various document types, including OpenDocument files. These tools often work by attempting brute-force attacks or by exploiting known vulnerabilities. You typically upload your file, and the service attempts to crack the password.
While convenient, using online tools comes with significant risks. You are uploading potentially sensitive data to a third-party server, which could compromise your privacy and security. Furthermore, the success rate can be low, especially for files protected with strong, complex passwords.
Desktop Software for Password Recovery
Dedicated desktop software offers a more robust approach to password recovery for OpenDocument files. These applications can be installed on your computer and often provide more advanced features, such as customizable brute-force attacks, dictionary attacks, or GPU acceleration to speed up the process.
These tools can be effective for recovering forgotten passwords, but they require patience, as cracking strong passwords can take a considerable amount of time and computational resources. It's essential to download such software only from reputable sources to avoid malware.
Ethical and Security Considerations
Before attempting any password removal, it's paramount to consider the ethical and legal implications. Password protection is a security feature. Attempting to bypass it on files you do not own or have explicit permission to access is a breach of privacy and can have serious consequences.
Always ensure you have the right to access the file. If the file belongs to you and you've forgotten the password, proceed with caution, especially when using third-party tools. Understand the risks associated with data privacy and potential malware infections.
Data Privacy Risks
When using online tools or downloading software, your file is either uploaded to a remote server or processed locally. In either scenario, there's a risk of data exposure. Sensitive information within the document could be intercepted, stored improperly, or accessed by unauthorized parties.
It's crucial to vet any service or software thoroughly. Look for reviews, check privacy policies, and understand how your data is handled. For highly sensitive documents, local software solutions from trusted vendors are generally preferred over online services.
The Importance of Strong Passwords
The best approach to managing document security is to prevent the need for password removal in the first place. This means creating and securely storing strong, unique passwords for your important files. Using a password manager can greatly assist in this regard.
A strong password typically includes a mix of uppercase and lowercase letters, numbers, and symbols, and is long enough to resist brute-force attacks. Regularly updating passwords and avoiding easily guessable information further enhances security.
Prevention Strategies
The most effective way to deal with lost passwords is to prevent losing them. Implementing good document password management practices from the outset can save a lot of trouble.
Utilize Password Managers
Password managers are invaluable tools for generating, storing, and managing complex passwords. They create strong, unique passwords for each file or service and store them securely in an encrypted vault. This eliminates the need to memorize numerous passwords and reduces the risk of using weak or reused ones.
By using a password manager, you can assign a strong password to your OpenDocument files and trust the manager to keep it safe. This ensures that when you need access, the password is readily available and secure.
Securely Store Passwords
If you choose not to use a password manager, ensure you have a secure method for storing your file passwords. This could involve encrypted notes, secure physical storage for written passwords, or other methods that protect the password from unauthorized viewing.
Avoid storing passwords in plain text files on your computer or in easily accessible cloud storage. The goal is to make the password readily available to you but inaccessible to others.
OpenDocument Password Removal Best Practices Summary
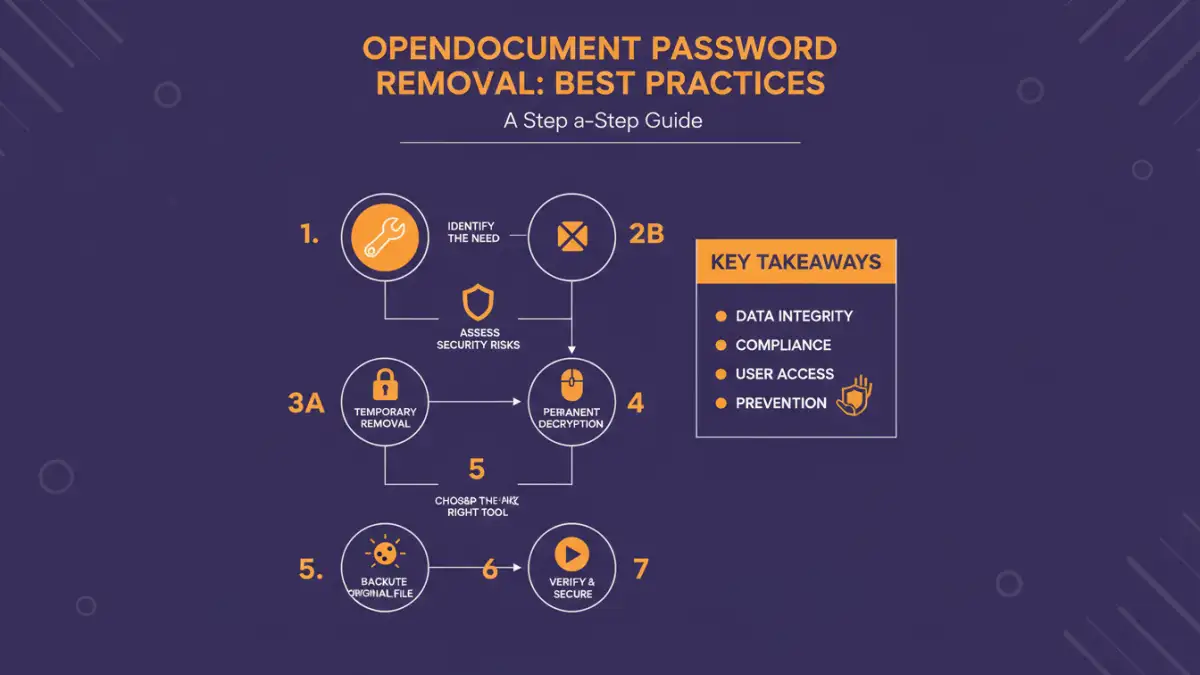
When dealing with password-protected OpenDocument files, always prioritize legitimate access and ethical conduct. If you have forgotten the password to your own file, consider the following best practices for OpenDocument password removal:
- Verify Ownership: Ensure you have the legal right and permission to access the file.
- Attempt Legitimate Recovery First: If possible, try to recover the password through the original application's features or by contacting the person who shared the file.
- Use Reputable Tools: If using third-party software or online services, choose well-known, trusted vendors with strong privacy policies.
- Understand Risks: Be aware of data privacy and security risks, especially with online tools.
- Prioritize Prevention: Implement strong password management strategies, such as using password managers, to avoid future issues.
Adhering to these guidelines will help you manage your secure documents effectively while maintaining data integrity and security.
Comparison Table: Password Recovery Methods
| Method | Pros | Cons | Best For |
|---|---|---|---|
| Browser/Text Editor Trick (Legacy) | Free, No extra software needed | Only works for very old, specific 'owner' password types; largely obsolete | Accessing older, less securely protected files |
| Online Password Recovery Tools | Convenient, accessible from anywhere, often free for basic use | Significant privacy/security risks (uploading data), variable success rates, potential for malware | Non-sensitive files where privacy is not a major concern; quick, simple password types |
| Desktop Password Recovery Software | More powerful, advanced features (brute-force, dictionary attacks), runs locally (better privacy) | Can be costly, requires installation, can be time-consuming for strong passwords, potential for malware if not from reputable source | Recovering passwords for personal files with forgotten passwords; strong encryption |
| Password Managers | Secure generation and storage of strong passwords, eliminates memorization | Requires setup and management, potential costs for premium features, reliance on the manager's security | Proactive security; preventing password loss for all digital assets, including documents |