
Working with password-protected documents can be frustrating, especially when you've forgotten the password or inherited a file without one. While many applications offer built-in security, losing access to crucial information can halt workflows and cause significant stress. I've seen many situations where a simple forgotten password turns into a major roadblock.
The good news is that for most common document formats, there are ways to regain access. However, not all password issues are simple. Sometimes, the complexity of the encryption or the sensitivity of the data demands a more robust approach than what a quick online search might suggest. This is where understanding when to call in the experts becomes crucial.
Table of Contents
Understanding the Basics of Document Protection
OpenDocument formats, like .odt for text documents and .ods for spreadsheets, offer robust password protection features. These are designed to safeguard sensitive information from unauthorized access. When you set a password, the application encrypts the file's content. This means without the correct password, the data is essentially scrambled and unreadable.
Types of Encryption
The strength of this protection varies. Older or simpler password settings might rely on less sophisticated encryption methods that can sometimes be bypassed with specialized tools. However, modern applications often employ strong encryption algorithms, making brute-force attacks or simple bypasses extremely difficult and time-consuming. My experience shows that the type of encryption is a key factor in whether a DIY approach will succeed.
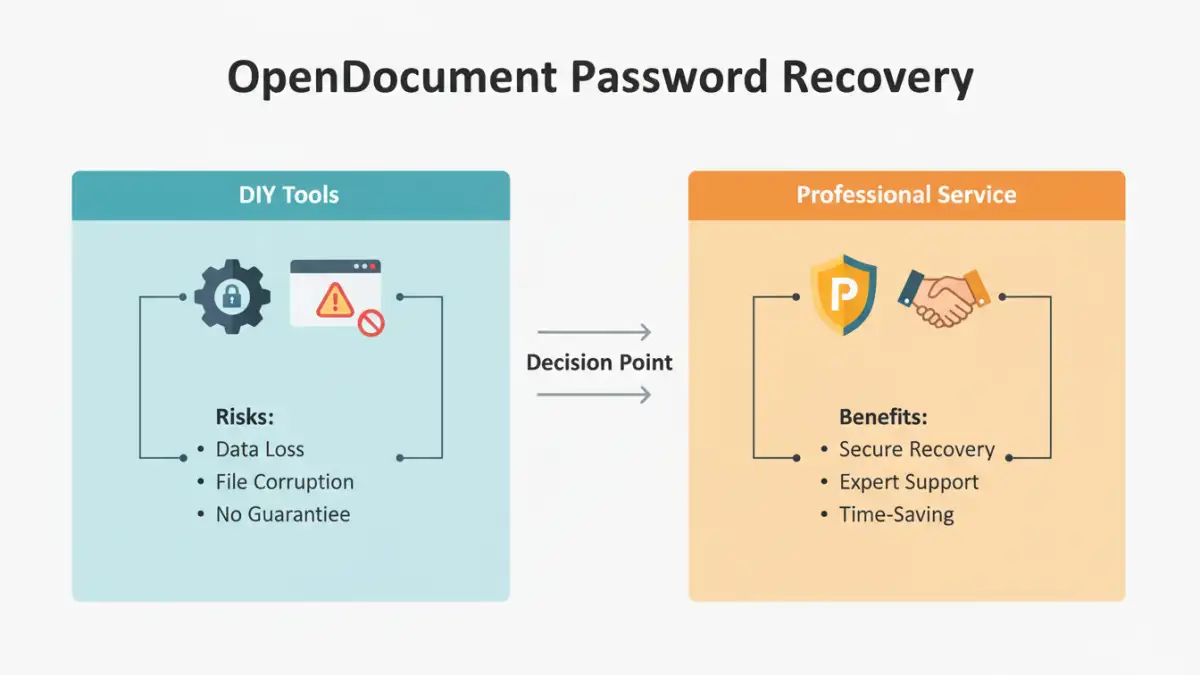
DIY Methods vs. Professional Help
For many users, the first instinct when facing a forgotten password is to try online tools or simple software that claims to crack passwords. These methods can sometimes work, particularly for older or less securely encrypted files. However, they come with significant risks.
The danger with DIY solutions, especially free online tools, involves potential data corruption or security breaches. Uploading sensitive documents to untrusted websites can expose your data to malicious actors. Furthermore, aggressive attempts to bypass passwords can sometimes permanently damage the file structure, making data recovery impossible even for professionals.
When to Call the Professionals
There are several clear indicators that you should consider seeking professional open document password removal assistance. The most obvious is when your DIY attempts fail. If you've tried multiple software options or online services without success, it's a strong sign that the file's encryption is more complex than these tools can handle.
Another critical factor is the sensitivity of the data. If the document contains confidential business information, personal financial details, or any data that absolutely cannot be compromised, the risk associated with DIY methods is too high. Engaging data recovery services ensures that the process is handled by experts who prioritize data integrity and security. They have specialized tools and techniques that are far more advanced than consumer-level software.
Complex Encryption Scenarios
Sometimes, the password protection might have been applied using specific software or a very strong, custom encryption algorithm. In such cases, generic password recovery tools are unlikely to work. Professionals have the capability to analyze the encryption method and employ tailored strategies. This is often the only viable path to recovering data from highly secured files.
File Corruption or Damage
If a file is already partially corrupted, or if your own attempts to recover the password have caused further damage, professional data recovery services are essential. They possess advanced techniques to reconstruct damaged file structures and extract the data, even when standard methods fail. Relying on them minimizes the risk of losing the data permanently.
Choosing a Professional Provider
When selecting a service for professional open document password assistance, look for established companies with a proven track record. Check for reviews, testimonials, and clear service level agreements. Ensure they have expertise in handling various file formats and encryption types.
Transparency is key. A reputable provider will explain the process, potential risks, and expected outcomes upfront. They should also have strong confidentiality agreements in place to protect your sensitive data. Don't hesitate to ask about their success rates and the security measures they employ to safeguard your information throughout the recovery process.
Preventative Measures
The best approach to password-protected documents is, of course, prevention. Always store your passwords in a secure password manager. For critical documents, consider keeping a secure backup of the password separately, perhaps in encrypted cloud storage or a physical secure location. If you're setting passwords for important files, use strong, unique passwords and document them carefully.
For business environments, implementing clear policies for password management and document security is vital. Regular training for employees on best practices can prevent many password-related data access issues. Remembering or securely storing passwords is far less costly and stressful than needing to recover lost access.
Comparison Table: Password Recovery Methods
| Method | Pros | Cons | Best For |
|---|---|---|---|
| DIY Software/Online Tools | Free or low cost, readily available | Risk of data corruption, privacy concerns, limited effectiveness on strong encryption | Simple passwords, non-sensitive files, quick fixes |
| Professional Data Recovery Services | High success rate, handles complex encryption, preserves data integrity | Higher cost, requires shipping data or device | Highly sensitive data, complex encryption, damaged files, failed DIY attempts |
| Password Managers | Secure storage, auto-generation, easy access to multiple passwords | Requires setup, potential subscription costs, not a recovery tool for forgotten passwords themselves | Managing and remembering strong passwords for ongoing access |