
Working with password-protected documents can be frustrating, especially when you've forgotten the password or inherited a file without one. This is a common scenario, and thankfully, there are often ways to regain access. My own experience, particularly when dealing with legacy files or assisting colleagues, has shown me that while robust security is essential, accessibility shouldn't be an insurmountable barrier.
Many users seek straightforward solutions for regaining access to their OpenDocument files. Whether it's a spreadsheet, presentation, or text document, losing access can halt productivity. This guide will walk you through what you need to know, covering various approaches and considerations for handling these situations.
Table of Contents
Understanding OpenDocument Security
OpenDocument files, like .odt, .ods, and .odp, can be protected with passwords to prevent unauthorized access. This encryption is a valuable tool for safeguarding sensitive information. It ensures that only individuals with the correct password can open and modify the document. Understanding how this protection works is the first step in addressing situations where access is lost.
How Encryption Works
The security applied to OpenDocument files typically uses symmetric encryption algorithms. This means the same key (derived from your password) is used to both encrypt and decrypt the file's content. If the password is weak or forgotten, the protective layer becomes a significant obstacle.
Basic Password Removal Techniques

When faced with a forgotten password, the first instinct is often to look for simple, direct methods. While there isn't a universal 'master key' for OpenDocument files, certain approaches can be effective, especially for older or less complex protections. These methods often involve exploiting how the password information is stored or how the application handles file access.
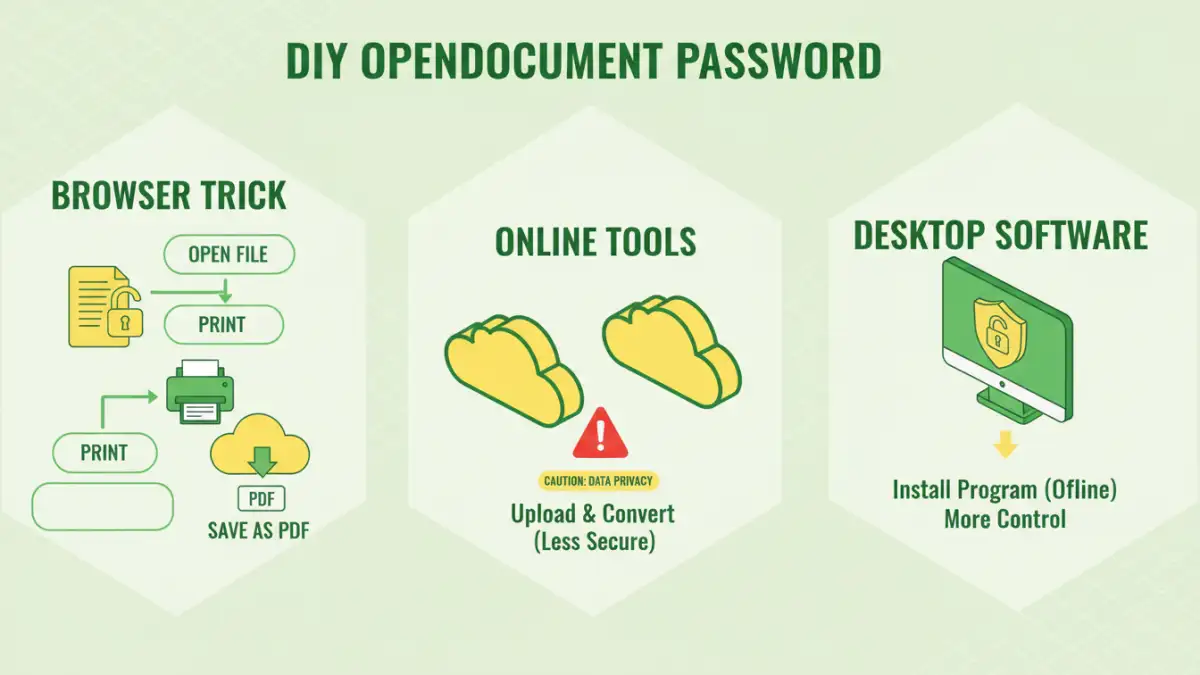
The Browser Trick (for Owner Passwords)
For some OpenDocument files, particularly those protected with an 'owner password' (which restricts editing rather than opening), a simple trick might work. This involves opening the document in a compatible viewer or editor, going to the print function, and saving it as a PDF. Sometimes, this process can strip away certain levels of protection, making the content accessible. This is one of the most accessible forms of manual password removal for specific scenarios.
Using Online Tools
Numerous online services claim to help remove passwords from various document types, including OpenDocument files. These tools often work by trying to brute-force or exploit known vulnerabilities. While convenient, it's crucial to exercise caution. Uploading sensitive documents to third-party websites carries privacy risks. Always research the reputation of any online tool before using it, and be wary of those that ask for payment upfront or seem too good to be true.
Advanced File Access Solutions
When simpler methods fail, or if the document uses stronger encryption, more advanced techniques might be necessary. These often involve specialized software or a deeper understanding of file structures. These file access solutions are typically more robust but may require more technical expertise or investment.
Desktop Software for Password Recovery
There are specialized desktop applications designed to recover or remove passwords from various file types, including OpenDocument formats. These programs often employ sophisticated cracking techniques, such as brute-force attacks (trying every possible combination) or dictionary attacks (using lists of common words and phrases). The effectiveness of these tools depends heavily on the password's complexity and the encryption strength used by the original software. Some of these tools are commercial, while others might be open-source.
Understanding Encryption Strength
The security of your OpenDocument file depends on the encryption standard used. Newer versions of office suites and more recent security settings generally employ stronger encryption algorithms (like AES-256) that are much harder to break. Older files or those saved with default settings might use weaker encryption, making them more susceptible to recovery methods. This is a key factor when considering the viability of any diy open document password attempt.
Best Practices for Document Management
While recovering lost passwords is sometimes necessary, proactive measures in document management are far more effective. Implementing good security habits can prevent you from needing to remove passwords in the first place. This involves secure storage, clear documentation, and using password managers.
Secure Password Practices
Always use strong, unique passwords for your sensitive documents. A strong password typically includes a mix of uppercase and lowercase letters, numbers, and symbols, and is at least 12 characters long. Consider using a password manager to generate and store complex passwords securely. This also helps prevent the need for manual password removal later.
Regular Backups
Maintain regular backups of your important files. Storing backups in multiple secure locations (e.g., external hard drive, secure cloud storage) ensures that you have access to your data even if the original file becomes inaccessible due to a forgotten password or other issues. This is a fundamental aspect of robust document management.
Comparison Table: OpenDocument Password Removal Methods
| Method | Pros | Cons | Best For |
|---|---|---|---|
| Browser Trick (Owner Password) | Free, no extra software needed, quick for specific cases | Only works for owner passwords, not opening passwords; limited effectiveness | Quickly removing editing restrictions on less sensitive files |
| Online Password Removal Tools | Convenient, accessible from anywhere, often free for basic use | Privacy and security risks, potential for malware, limited functionality, may not work for strong encryption | Non-sensitive documents where privacy is less of a concern and a quick solution is needed |
| Desktop Password Recovery Software | More powerful and comprehensive, can handle stronger encryption, offline processing | Often paid software, can be complex to use, requires installation, success not guaranteed for very strong passwords | Recovering access to important documents with strong encryption where privacy is maintained |