
When dealing with sensitive information, the way we store and manage our digital files is just as crucial as the content itself. I've encountered many situations where critical documents were compromised not due to sophisticated cyberattacks, but simply because they weren't organized or protected properly. This oversight can lead to data breaches, loss of proprietary information, and significant reputational damage.
Effectively organizing your Microsoft Word files goes beyond just creating folders. It involves implementing robust strategies to ensure the safety and accessibility of your data. This means understanding the built-in security features of Word and adopting best practices for file management. Let's explore how to achieve this.
Table of Contents
Understanding the Basics of Document Security
At its core, document safety involves protecting your files from unauthorized access, modification, or deletion. For Microsoft Word, this starts with understanding the different levels of protection available. It's not just about passwords; it's about creating a secure environment for your digital assets. Thinking about the lifecycle of your document, from creation to archiving, is key.
Core Security Principles
Several fundamental principles underpin effective file security. These include confidentiality (ensuring only authorized individuals can access the data), integrity (ensuring data is accurate and hasn't been tampered with), and availability (ensuring authorized users can access data when needed). Applying these principles to your word documents forms the foundation of good practice.
Strategies for Organizing Word Files

Good organization is the first line of defense for any file. When you know where your documents are and how they are categorized, it's easier to identify and secure them. This involves a systematic approach to naming conventions, folder structures, and version control.
Logical Folder Structures
Creating a clear and logical folder hierarchy is essential. Instead of dumping all documents into one large folder, break them down by project, department, date, or document type. For instance, a 'Projects' folder could contain subfolders for each active project, with further subfolders for 'Drafts,' 'Final Versions,' and 'Supporting Documents.' This makes locating specific files much faster and helps in applying security measures uniformly.
Consistent Naming Conventions
Adopt a consistent naming convention for your files. This might include a date prefix (e.g., YYYY-MM-DD), a project code, and a brief description (e.g., 2023-10-27_ProjectAlpha_MeetingNotes_v3.docx). Consistent naming aids in sorting, searching, and version tracking, which are all components of effective microsoft word file organization.
Securing Your Word Documents
Microsoft Word offers several built-in features to protect your documents. Leveraging these can significantly enhance document safety. The most common method is password protection, but there are other important considerations.
Password Protection
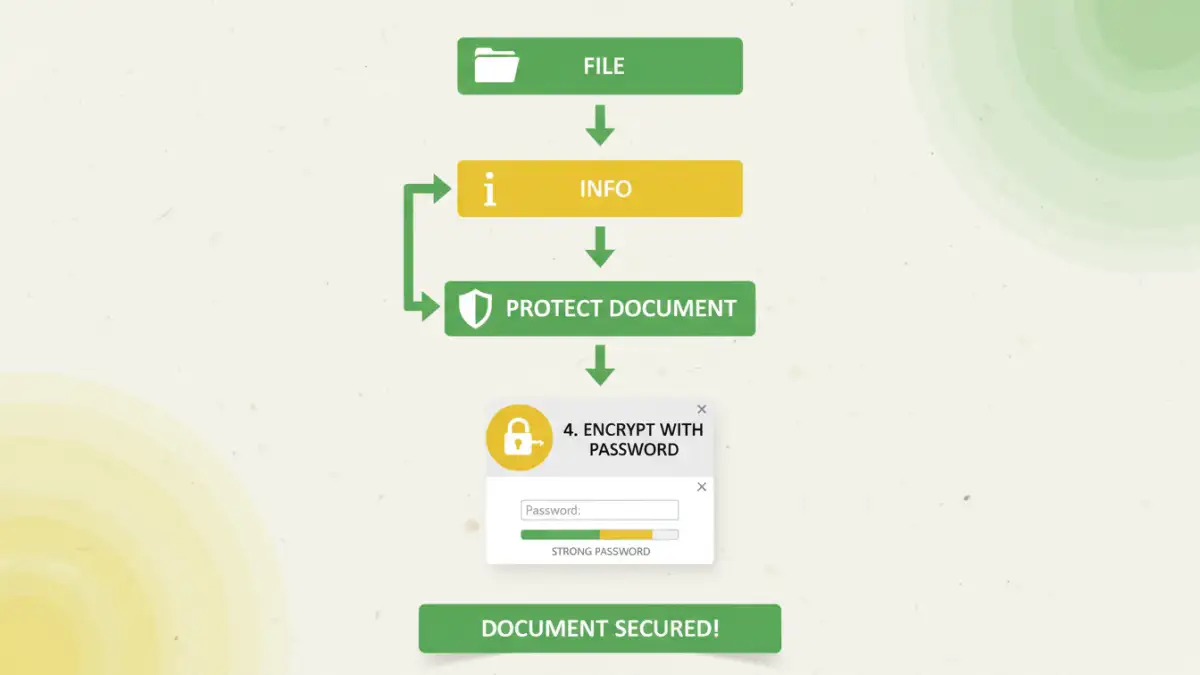
Word allows you to set passwords to open a document or to modify it. To do this, go to File > Info > Protect Document > Encrypt with Password. It's crucial to use strong, unique passwords that are difficult to guess. Avoid common words, personal information, or sequential numbers. A password manager can be invaluable for generating and storing these complex passwords securely.
Restricting Editing
Beyond just opening, you can restrict editing permissions. Under the 'Protect Document' menu, you can choose to 'Restrict Editing.' This allows you to limit who can make changes and to what extent, such as allowing only comments or specific types of formatting. This is particularly useful when collaborating or sharing drafts.
Advanced Security Techniques
For highly sensitive information, basic password protection might not be enough. More advanced techniques can provide an extra layer of security for your word documents.
Digital Signatures
Digital signatures verify the identity of the document's author and ensure the document's integrity. They use encryption to create a unique digital certificate tied to the author. This is different from password protection but adds a layer of authenticity and non-repudiation.
Information Rights Management (IRM)
IRM, often implemented through enterprise solutions like Azure Information Protection, offers granular control over document access and usage. You can set permissions that follow the document even when it's shared, restricting actions like printing, copying, or forwarding. This is a powerful tool for organizations dealing with confidential data.
Best Practices for Ongoing Document Safety
Maintaining document safety is an ongoing process, not a one-time setup. Regularly reviewing your security measures and adapting to new threats is essential. Effective microsoft word file organization and security are intertwined.
Regular Backups
Always maintain regular backups of your important documents. Store these backups in a separate, secure location, preferably both locally and in the cloud. This ensures you can recover your data in case of accidental deletion, hardware failure, or a security incident.
Keep Software Updated
Ensure Microsoft Word and your operating system are always updated. Software updates often include patches for security vulnerabilities that could be exploited by malicious actors. Staying current is a simple yet effective way to bolster your overall file security.
Comparison Table: Document Security Features
| Feature | Description | Use Case | Complexity |
|---|---|---|---|
| Password to Open | Requires a password to access the document content. | Protecting sensitive personal or business documents from casual access. | Low |
| Password to Modify | Allows opening but requires a password to make changes. | Sharing drafts where you want to prevent accidental edits by recipients. | Low |
| Restrict Editing | Limits specific editing capabilities (e.g., comments only, no changes). | Collaborative environments, review processes, or when sharing templates. | Medium |
| Digital Signatures | Verifies author identity and document integrity using certificates. | Ensuring authenticity and preventing tampering in formal documents. | Medium |
| Information Rights Management (IRM) | Granular control over permissions (e.g., no printing, no copying) that travel with the document. | Enterprise environments handling highly confidential or regulated data. | High |