
Working with password-protected documents on cloud platforms can sometimes present unique challenges, especially when it comes time to remove them. Whether you're trying to clean up old files, ensure sensitive information is no longer accessible, or simply manage your cloud storage space, understanding the process is key. It's not always as straightforward as a simple delete command, particularly if the protection mechanism is tied to the file itself.
My experience in software engineering has shown me that while cloud providers offer robust security features, the final layer of protection often rests with the user's actions. This guide aims to demystify the process of removing these secured files, offering practical steps and insights to ensure your data is handled correctly and securely.
Table of Contents
Understanding the Nuances
When a document is password-protected, the security is typically embedded within the file itself or managed by a specific application. Cloud storage services like Google Drive, Dropbox, or OneDrive generally treat these files as any other – they store them and sync them. The cloud platform itself doesn't inherently 'understand' the password protection unless it's a feature integrated with their service, like Google Workspace's built-in encryption.
This means that simply selecting a password-protected file in your cloud interface and hitting delete might not always be the complete solution. The file might be removed from the cloud's active view, but if its underlying structure is still intact, there could be residual data or metadata that needs addressing. Understanding how the protection was applied is the first step to effective removal.
Types of Document Protection
Documents can be protected in several ways: application-level passwords (like in Microsoft Office or Adobe Acrobat), file system encryption, or through third-party encryption tools. Each method has implications for how the file can be deleted and secured. For instance, a PDF password applied directly in Adobe Reader is part of the PDF structure, while a file encrypted using VeraCrypt is a container that the cloud service sees as a single encrypted blob.
Direct Deletion Methods

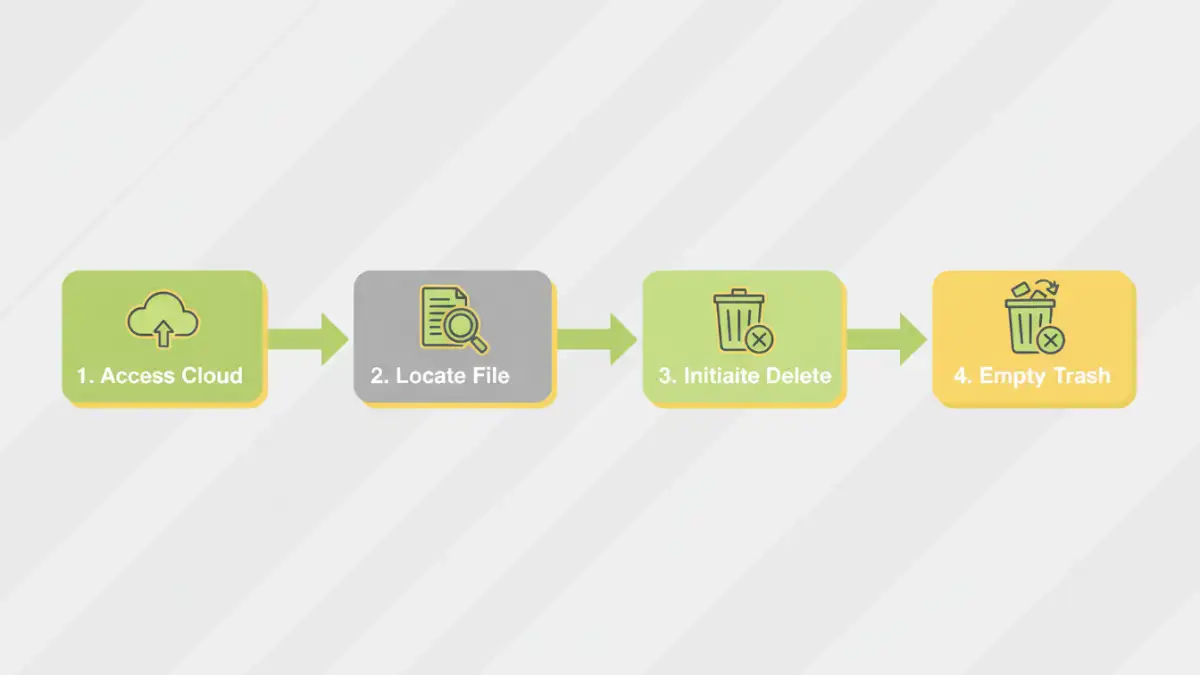
In many common scenarios, the process to delete password protected documents from cloud storage is quite straightforward. If you are the owner of the file and have access to your cloud account, the standard deletion process usually suffices. This involves navigating to the file's location in your cloud service's web interface or desktop app and initiating a delete command.
Once deleted, the file is typically moved to a 'trash' or 'recycle bin' folder within the cloud service. It remains there for a set period, allowing for recovery, before being permanently purged. For most users, this two-step deletion process is enough to remove the file from active access and storage. However, it's crucial to remember to also empty this trash folder for complete removal.
Standard Deletion Workflow
1. Log in to your cloud storage account.
2. Navigate to the folder containing the password-protected document.
3. Select the file.
4. Click the 'Delete' or 'Remove' option.
5. Access the 'Trash' or 'Recycle Bin'.
6. Permanently delete the file from the trash.
Indirect Removal Techniques
Sometimes, direct deletion might not feel sufficient, especially if you're concerned about lingering data or if the file was protected using a method that bypasses simple file deletion. In such cases, employing indirect methods ensures that any potential remnants are also cleared. This often involves ensuring the file is no longer accessible or functional before the final deletion.
One common indirect approach is to try and 'unlock' or 'decrypt' the file first, if possible, and then delete it. If you have the password, you can often open the document in its native application, save it as a new, unprotected file, and then delete both the original protected version and the newly created unprotected version. This ensures no encrypted data remains linked to your account.
Decrypt and Delete Strategy
For files protected by application-level passwords (e.g., Word or Excel files), you can often open them using the correct password in the respective software. Once open, you can save the document with a new name or in a different location, effectively creating an unprotected copy. After verifying the copy is indeed unprotected, you can then proceed to delete the original password-protected file from your cloud storage, and importantly, from the trash/recycle bin.
Security Considerations
When dealing with sensitive documents, the act of deletion itself should be treated with care. Simply deleting a file from cloud storage doesn't always mean it's immediately and irrecoverably gone. As mentioned, most services have a grace period in their trash folders. Furthermore, depending on the cloud provider's infrastructure and your account's sync settings, there might be temporary local copies or backups that need consideration.
For extremely sensitive data, consider using the cloud provider's built-in secure deletion features if available, or ensure that any encryption used was strong and that the decryption keys or passwords are no longer accessible. If you're removing files that were protected with a password you no longer have, the situation becomes more complex, often requiring specialized tools or accepting the potential for data recovery if the file wasn't truly overwritten.
Best Practices
To effectively manage and remove password protected documents from your cloud storage, adopting a few best practices can save you time and potential security headaches. Always ensure you have the correct password before attempting to manage or delete a secured file. If you've lost the password, be aware that removing the file might be your only option, and recovery of the content will likely be impossible.
Regularly audit your cloud storage for files you no longer need, especially those containing sensitive information. Utilize the 'empty trash' feature consistently. For maximum security, consider using end-to-end encryption services for highly confidential documents, where even the cloud provider cannot access your data, though this also means you are solely responsible for managing access and recovery.
Comparison Table: Document Removal Methods
| Method | Ease of Use | Security Effectiveness | Data Remnants Risk | When to Use |
|---|---|---|---|---|
| Standard Cloud Deletion (Move to Trash) | High | Moderate (file removed from active view) | Low to Moderate (depends on service's purge policy) | General file removal |
| Emptying Trash/Recycle Bin | High | High (permanent deletion by service) | Very Low | Finalizing deletion |
| Decrypt, Save As New, Then Delete | Moderate (requires password and software) | High (ensures unprotected copy is deleted) | Low | When confident in removal; sensitive data |
| Using Third-Party Decryption Tools (if password known) | Moderate to Low (tool dependent) | High (if tool is reputable) | Low | Complex encryption types |
| Ignoring Password (if lost) and Deleting | High | Moderate (file removed, but content inaccessible) | High (if file is not overwritten) | When recovery is impossible and file must be gone |