Have you ever wondered how a simple password can encrypt a massive ZIP archive in seconds, yet sending a truly secure email involves a more complex process of exchanging keys? The answer lies in the two fundamental approaches to cryptography: symmetric and asymmetric encryption. Understanding the difference isn't just academic; it's crucial for making smart decisions about how you protect your sensitive documents, from personal financial records to confidential business plans.
Choosing the right approach depends entirely on your goal. Are you encrypting a file for your own use on your hard drive, or are you trying to send it securely to a colleague across the internet? Each scenario calls for a different tool, and I've seen firsthand how picking the wrong one can lead to either security gaps or unnecessary complexity.
Table of Contents
Encryption Fundamentals: A Quick Refresher
At its core, encryption is the process of converting readable data, called plaintext, into an unreadable format called ciphertext. This is done using an algorithm and a 'key'. Only someone with the correct key can reverse the process, known as decryption, to turn the ciphertext back into readable plaintext. This simple concept is the foundation of modern data security.
The strength of the encryption depends on both the complexity of the algorithm and the length of the key. Longer keys provide exponentially more possible combinations, making it computationally infeasible for an attacker to guess the key through brute force. Common data security algorithms like AES (Advanced Encryption Standard) and RSA are the mathematical engines that perform this transformation.
The Key is Everything
Think of the encryption algorithm as the design of a lock and the key as the unique item that opens it. You can have the most advanced lock in the world, but if someone steals your key, the lock is useless. This is why key management—how you store, share, and protect your keys—is just as important as the encryption itself. The primary difference between symmetric and asymmetric systems lies in how they handle these keys.
Symmetric Encryption: The Single Key Workhorse
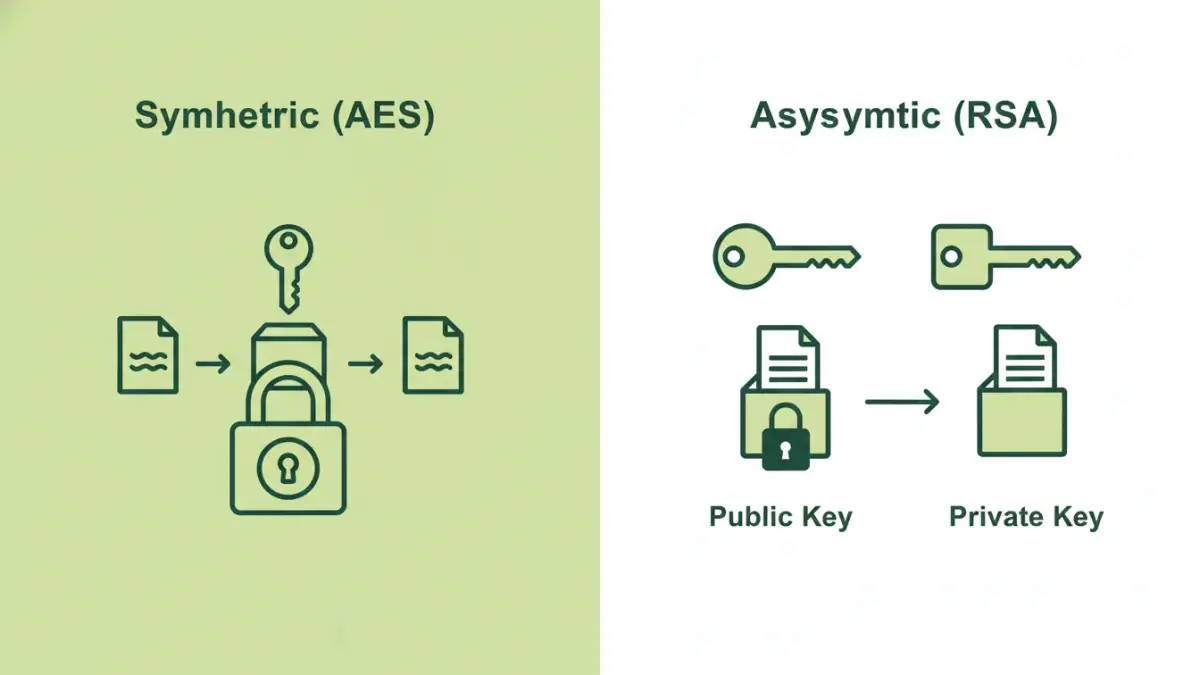
Symmetric key encryption is the most straightforward of the file encryption methods. It uses a single, shared secret key to both encrypt and decrypt data. If you and I want to share an encrypted file, we must both have the exact same key. It's like using a physical key to lock a box; the same key is needed to open it again.
This method is incredibly fast and efficient. Algorithms like AES are optimized for encrypting large volumes of data quickly, which is why they are used for things like full-disk encryption (BitLocker, FileVault) and securing files in archives like ZIP or 7z. The main challenge, however, is key distribution. How do you securely share the secret key with the intended recipient in the first place? Sending it over an unsecured channel defeats the purpose of the encryption.
Common Use Cases for Symmetric Encryption
Because of its speed, symmetric encryption is ideal for encrypting data at rest—files stored on your computer, a backup drive, or in the cloud. You are the only one who needs the key (or password), so the key distribution problem doesn't exist. It's perfect for personal data protection where speed and efficiency are paramount.
Asymmetric Encryption: The Secure Handshake
Asymmetric key cryptography, also known as public-key cryptography, solves the key distribution problem by using a pair of mathematically linked keys: a public key and a private key. The public key can be shared freely with anyone. It's used only to encrypt data. The private key, however, must be kept secret by its owner. It is the only key capable of decrypting data that was encrypted with its corresponding public key.
Imagine a mailbox with a slot. Anyone can drop a letter (encrypted data) into the slot using the publicly known mailbox address (public key). But only the person with the unique key to the mailbox (private key) can open it and read the letters. This is the magic of asymmetric encryption. It allows for secure communication without ever having to share a secret key over an insecure channel. Algorithms like RSA are the most well-known examples.
Where Asymmetric Shines: Digital Signatures and Key Exchange
While effective, asymmetric encryption is much slower and more computationally intensive than its symmetric counterpart. It's not practical for encrypting large files directly. Instead, its primary use is for securely exchanging small amounts of data, like a symmetric key, or for creating digital signatures to verify the identity of a sender. This is the foundation of technologies like SSL/TLS that secure website traffic.
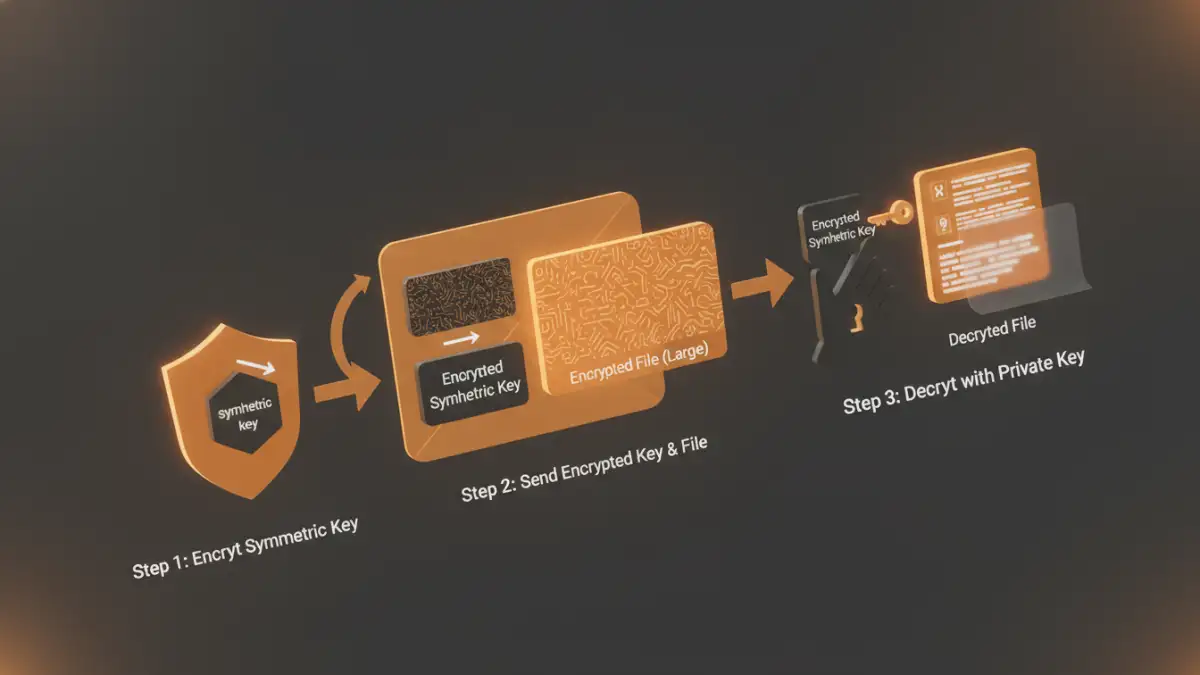
Hybrid Encryption: The Best of Both Worlds
In practice, most modern systems use a hybrid approach that combines the strengths of both types of encryption. When you connect to a secure website (HTTPS) or use a secure messaging app, you're using hybrid encryption. Here’s how it typically works for sending a large file securely:
- The system generates a new, one-time symmetric key.
- It uses this fast symmetric key to encrypt the large file.
- It then uses the recipient's public key (asymmetric) to encrypt only the small symmetric key.
- Both the encrypted file and the encrypted symmetric key are sent to the recipient.
- The recipient uses their private key to decrypt the symmetric key, and then uses that symmetric key to quickly decrypt the large file.
This method provides the speed of symmetric encryption for the bulk data and the security of asymmetric encryption for the crucial key exchange. It's a clever and efficient solution that underpins much of our digital security infrastructure.
Comparison Table: Encryption Types
| Feature | Symmetric Encryption (e.g., AES) | Asymmetric Encryption (e.g., RSA) |
|---|---|---|
| Key Used | One single, shared secret key | A pair of keys: one public, one private |
| Speed | Very fast and efficient | Significantly slower and resource-intensive |
| Key Management | Difficult; secure key distribution is a major challenge | Simpler; public key can be shared openly |
| Best For | Encrypting large amounts of data at rest (disk encryption, file archives) | Secure key exchange, digital signatures, encrypting small data |
| Common Analogy | A single key for a physical lockbox | A public mailbox with a private key to open it |