
It was a cold Tuesday afternoon when a simple request from my wife—"Can you find that photo of our son's first birthday?"—sent a chill down my spine. Of course, I could. I had meticulously archived years of family memories into a single, heavily encrypted container file. It was my digital fortress, safe from data loss or prying eyes. But as I typed in the password I was so sure I remembered, the system responded with a blunt 'Access Denied.' I tried again. And again. The horrifying realization slowly dawned on me: I was locked out of my own family's history.
This wasn't just a case where I forgot a PDF password for a single document; this was a decade of irreplaceable moments. As an engineer, I'm paid to solve complex problems logically. Yet, in that moment, all I felt was a rising panic. This is the story of how I almost lost everything and the methodical process I used to get it back.
Table of Contents
The Digital Fortress I Built (And Almost Lost)
Years ago, I decided to consolidate all our digital photos into a single encrypted archive. My logic was sound: cloud services could be breached, and physical hard drives could fail or be stolen. A self-contained, encrypted volume seemed like the perfect solution for long-term preservation. It protected our privacy and ensured the files remained uncorrupted.
I used a well-known open-source tool to create the volume, selecting a strong AES-256 encryption cipher. The final piece of the puzzle was the password—a long, complex passphrase I believed was both secure and memorable. It was a classic mistake of overconfidence, mixing personal trivia with special characters in a way I thought was clever at the time. I had created a vault so secure that even I, its creator, was struggling to get inside.
The Choice of Encryption and Password
Choosing the right tool is only half the battle. The other half is password management. My passphrase was a combination of an old address, a significant date, and a favorite line from a book, interspersed with symbols. On paper, it was strong. In practice, after years of not needing to access the archive, the exact sequence and character substitutions had faded from my memory. This is a common pitfall, whether you're trying to access protected photos or secure a work document.
The Moment of Panic: A Relatable Encrypted File Password Story

Staring at the password prompt, I felt my confidence as a technical professional evaporate. I tried every variation I could think of. Was the 'S' a '5'? Was the '#' at the beginning or the end? Each failed attempt amplified my anxiety. The archive contained everything: baby photos, family vacations, pictures of loved ones who were no longer with us. The thought of them being lost forever, trapped behind a digital wall of my own making, was devastating.
My initial attempts were frantic and disorganized. I searched old notebooks, dug through ancient text files on backup drives, and tried to recall the exact mindset I was in when I created the password. This chaotic approach yielded nothing but frustration. It became clear that I needed to stop guessing and start thinking like an engineer again.
My Initial Failed Attempts
My first hour was a blur of brute-force guessing based on memory. I tried common substitutions, capitalization variations, and different orderings of the phrases I thought I'd used. This is a classic first step for anyone trying to recover encrypted files, but without a system, it's incredibly inefficient. The encryption was designed to resist exactly this kind of attack, and I was just wasting time and increasing my stress levels.
A Systematic Approach to Document Password Recovery
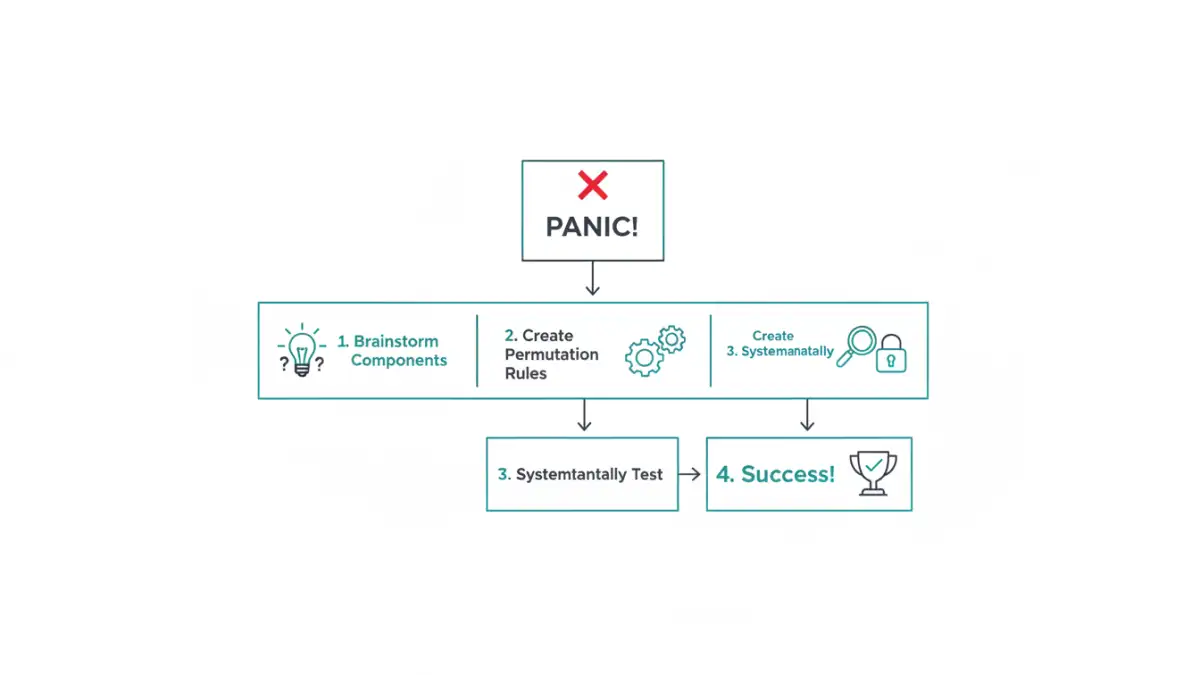
I stepped away from the computer, took a deep breath, and grabbed a whiteboard. It was time to approach this not as a panicked father but as a software engineer debugging a critical system. I broke the problem down into manageable parts.
First, I listed every possible component of the password I could remember: names, dates, places, special characters, and phrases. I created a mind map, linking concepts and trying to reconstruct the logic I used years ago. I then wrote a small Python script to generate permutations based on these components. Instead of guessing randomly, I was now systematically testing logical combinations. This methodical process is crucial for any kind of document password recovery.
Leveraging Tools with Caution
While my script ran, I researched specialized password recovery tools. There are many applications designed to perform dictionary or brute-force attacks on encrypted files. However, a word of caution: never upload sensitive files to an unknown online recovery service. For my precious family photos, that was a risk I was unwilling to take. I focused on reputable, offline software that I could run on my own machine, giving me full control over the process and my data. These tools can accelerate the process, but they are only as good as the password list you provide them.
The Breakthrough and Lessons Learned for the Future
After nearly a full day of systematic testing, the breakthrough came from an unexpected place. While looking at the file's creation date, I remembered the specific project I was working on at the time. That project had a specific naming convention that I often reused for personal things. I had forgotten one small, seemingly insignificant prefix. I added that prefix to my list of password components, reran my script, and within minutes, the program returned a match. The archive mounted, and the folder of photos appeared on my screen. The relief was immense.
This harrowing experience taught me several invaluable lessons. First, a complex password you can't remember is just as bad as a weak one. Second, password managers are not optional; they are essential infrastructure for modern digital life. Finally, for truly irreplaceable data, have a recovery plan. This could be a securely stored copy of the password or a trusted family member who also has access. My close call with this encrypted file password story fundamentally changed how I manage digital assets for my family.
Password Recovery Method Comparison
| Recovery Method | Pros | Cons | Best For |
|---|---|---|---|
| Memory Jogging & Manual Guessing | Free, no software required, completely private. | Time-consuming, unreliable for complex passwords, can be frustrating. | Simple passwords or when you have a strong hint. |
| Custom Scripts (Permutation Generators) | Highly targeted, full control over the logic, private. | Requires technical/programming skills to create. | Complex passwords where components are known. |
| Offline Recovery Software | Faster than manual attempts, uses hardware acceleration (GPU). | Can be expensive, effectiveness depends on password complexity. | When you need to test millions of combinations quickly. |
| Online Recovery Services | Easy to use, no technical setup needed. | Major security and privacy risk; not for sensitive data. | Non-sensitive files where privacy is not a concern. |
| Password Manager Records | Instant access, highly reliable and secure. | Useless if the password was never stored in the first place. | Proactive prevention rather than recovery. |