
Have you ever sent a sensitive file and worried about who might intercept it? Whether it's a financial document, a confidential business proposal, or personal records, once a file leaves your device, its security is out of your hands—unless you use the right technology.
This is where the concept of end-to-end encryption comes in. It's a term you've likely seen used by messaging apps and secure cloud services, but what does it actually mean for sharing files? It’s a fundamental shift from simply trusting a service provider to mathematically ensuring privacy.
Table of Contents
What is End-to-End Encryption?
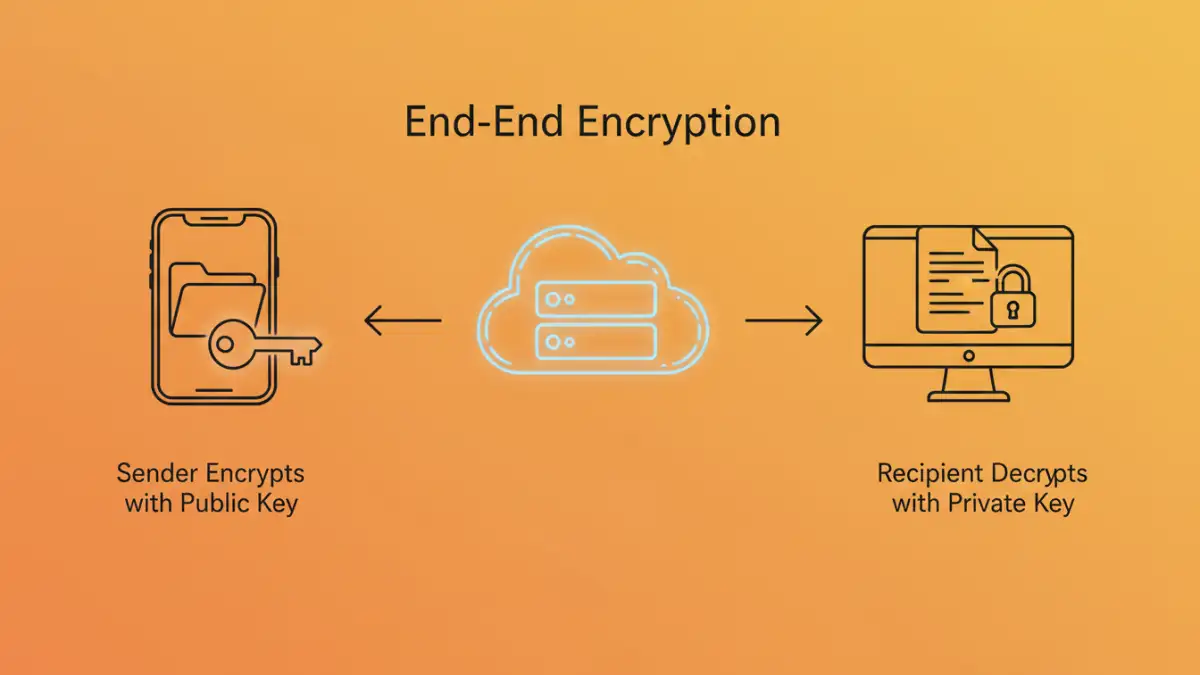
At its core, end-to-end encryption (E2EE) is a method of secure communication that prevents any third party from accessing data while it's transferred from one system or device to another. This includes the service provider, internet service providers (ISPs), and any potential attackers.
When you send a file using an E2EE system, the data is encrypted on your device before it's even uploaded. It remains encrypted as it travels across the internet and sits on the service's servers. It can only be decrypted by the intended recipient on their device using a key that only they possess. The server simply moves a blob of unintelligible data from point A to point B.
Encryption in Transit vs. E2EE
It's crucial to distinguish E2EE from a more common security measure: encryption in transit. When you see a padlock icon in your web browser (HTTPS), that indicates encryption in transit. Your data is encrypted between your browser and the server, but the server can decrypt and see your data. With E2EE, the server has no ability to decrypt the content at all.
How E2EE Protocols Work in Practice

E2EE relies on a principle called asymmetric cryptography, also known as public-key cryptography. Each user has a pair of mathematically linked keys: a public key and a private key. The public key can be shared with anyone, while the private key must be kept secret on the user's device.
To send a file securely, you encrypt it using the recipient's public key. Once encrypted, that file can *only* be decrypted with the corresponding private key, which only the recipient has. This ensures that even if the service provider is compromised, the file's contents remain confidential.
The Signal Protocol Explained
One of the most respected and widely adopted E2EE systems is the Signal Protocol. It's the engine behind apps like Signal and WhatsApp. It uses a clever technique called the "Double Ratchet Algorithm" to provide exceptionally strong security for ongoing conversations and file transfers.
The protocol continuously generates new, temporary encryption keys for every message or file sent. This property, known as "perfect forward secrecy," means that even if an attacker managed to steal a key for a single message, they couldn't use it to decrypt past or future messages. It's a constantly evolving lock that makes long-term eavesdropping nearly impossible.
Zero-Knowledge vs. End-to-End Encryption
You'll often hear the term "zero-knowledge" used alongside E2EE. While related, they aren't the same. E2EE describes how data is protected between users. Zero-knowledge is a system architecture where the service provider has zero knowledge of your data, including your password or encryption keys.
In a true zero-knowledge system, your password is used on your device to derive your encryption keys. The provider never sees your password in plain text. This is why if you forget your password for a zero-knowledge service, they can't help you recover it—they simply don't have the information. This architecture is a prerequisite for a trustworthy **end to end file encryption** service.
Choosing a Secure File Transfer Service
When evaluating a service for secure file transfer, technical claims matter. I always look for a few key indicators to verify that a platform takes security seriously and isn't just using buzzwords for marketing.
First, the service should explicitly state it uses end-to-end and zero-knowledge encryption. Second, look for transparency. Is the code open source? Do they publish third-party security audits? These actions demonstrate confidence in their security model. Finally, consider the user experience. The best security is the kind that's easy to use; otherwise, people will find workarounds that compromise safety.
Encryption Method Comparison
| Encryption Type | How It Works | Key Vulnerability Point | Best For |
|---|---|---|---|
| Encryption-in-Transit (TLS/SSL) | Encrypts data between your device and the server. | The server itself, where data is decrypted. | General web browsing, online shopping. |
| Encryption-at-Rest | Encrypts data stored on the server's hard drives. | A compromised server with access to decryption keys. | Protecting data from physical theft of servers. |
| End-to-End Encryption (E2EE) | Encrypts data on the sender's device; only the recipient can decrypt. | Compromised user devices (endpoints). The server is not a risk. | Confidential messaging and secure file transfer. |
| Zero-Knowledge Encryption | A system where the service provider cannot access user keys or data. | The user forgetting their password (unrecoverable). | Services where user privacy is paramount. |