Working with sensitive documents in a business environment presents a constant challenge: how to protect them effectively without hindering productivity. I've seen many organizations struggle with manual processes for securing PDFs, leading to inconsistencies and potential vulnerabilities. The need for a robust, yet streamlined, approach to PDF security is paramount in today's digital landscape.
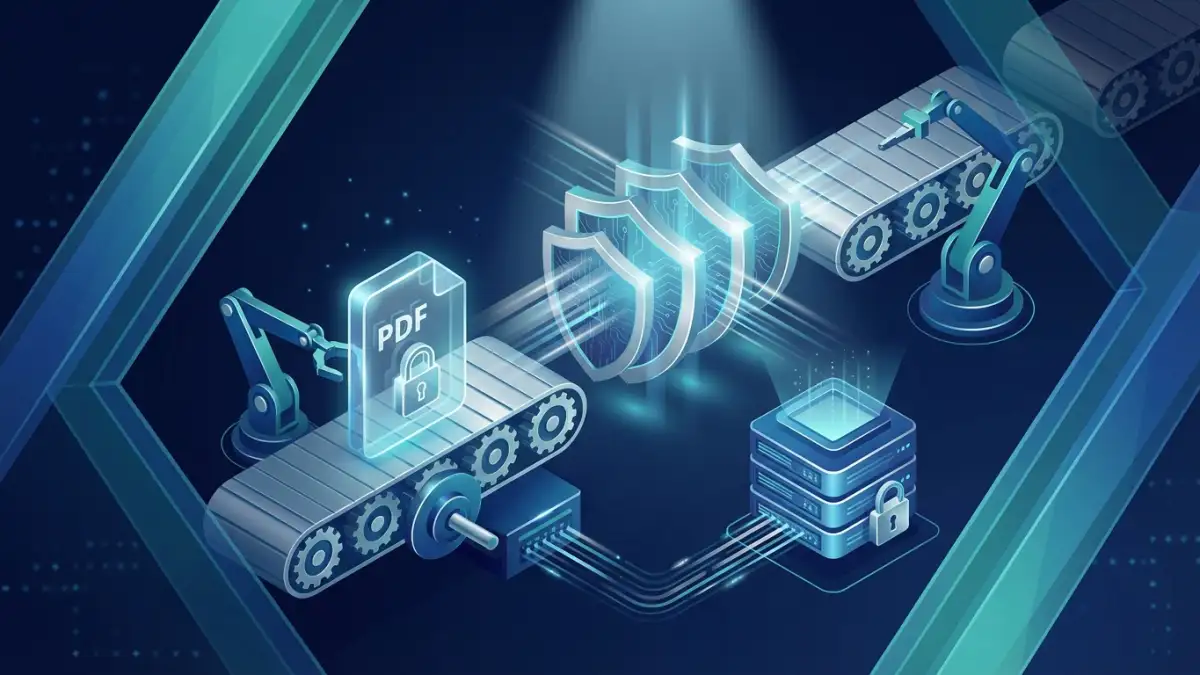
Implementing an automated PDF security workflow can significantly mitigate these risks. It ensures that critical business documents are protected consistently, reducing the chances of human error and unauthorized access. This not only safeguards confidential information but also helps in maintaining compliance with various data protection regulations. Let's explore how to build such a system.
Table of Contents
Understanding the Need for Automation
Manual PDF security, such as password protection applied one by one, is time-consuming and prone to errors. A single missed document can become a critical security breach. Automation ensures that every document requiring protection, based on predefined rules, receives it consistently. This is fundamental for maintaining business pdf security.
The Risks of Manual Processes
When employees manually handle PDF security, there's a high chance of oversight. Forgetting to password-protect a sensitive file, using weak passwords, or not applying the correct permissions can all lead to data leaks. This inconsistency undermines the entire security strategy, leaving the business exposed to significant risks like data theft, reputational damage, and regulatory fines.
Designing Your Automated Workflow
A well-designed automated workflow is the backbone of effective PDF security. It involves defining clear rules about which documents need protection, what level of protection is required, and how this process will be triggered and managed. This is where workflow automation security becomes crucial.
Defining Security Policies
Start by identifying types of documents that require protection – for example, financial reports, client contracts, HR records, or intellectual property. Then, determine the specific security measures needed for each type. This might include password protection, encryption, restricting printing or copying, or setting expiration dates for access.
Choosing the Right Tools
Several software solutions and platforms can help automate PDF security. These range from dedicated document management systems with built-in security features to specialized PDF security software and even custom scripting solutions. The choice depends on your business size, budget, existing infrastructure, and the complexity of your security requirements.
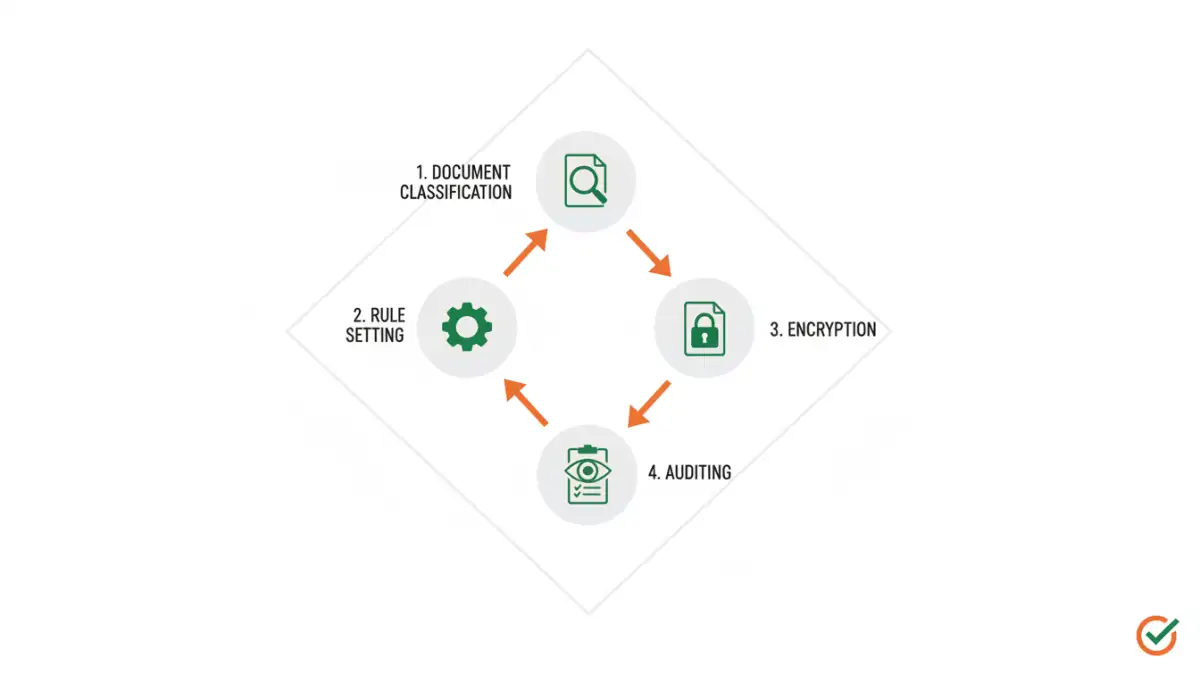
Key Implementation Steps
Implementing an automated PDF security workflow requires careful planning and execution. It's not just about deploying software; it's about integrating security seamlessly into your daily operations.
Step 1: Document Classification
Categorize your business documents based on their sensitivity. This classification will drive which security policies are applied. For instance, highly sensitive documents might require stronger encryption and stricter access controls than moderately sensitive ones.
Step 2: Automation Tool Setup
Configure your chosen automation tool according to your defined policies. This typically involves setting up rules that automatically apply passwords, encryption, or specific permissions to documents based on their type, location, or metadata. A good secure document process relies on precise configuration.
Step 3: Integration with Existing Systems
Ensure the automation tool integrates smoothly with your current document management systems, cloud storage, or email platforms. This allows for seamless processing of documents as they are created, shared, or stored, minimizing disruption.
Step 4: Testing and Refinement
Thoroughly test the automated workflow with various document types and scenarios. Monitor its performance, check for any unintended consequences, and refine the rules and settings as needed. User feedback is invaluable during this phase.
Advanced Security Features
Beyond basic password protection, modern automated PDF security workflows can incorporate more sophisticated measures. These features enhance protection and control over your sensitive documents.
Watermarking and Redaction
Automated watermarking can deter unauthorized sharing by clearly marking documents with ownership or confidentiality statements. For highly sensitive information, automated redaction tools can permanently remove specific content, ensuring only permitted data is visible.
Access Control and Auditing
Implement granular access controls to ensure only authorized personnel can view or modify specific documents. Robust auditing capabilities provide a clear trail of who accessed which document, when, and what actions they performed, which is critical for compliance and investigation.
Best Practices for Success
To maximize the effectiveness of your automated PDF security, adhere to these best practices. They ensure your system remains robust and user-friendly.
Regular Review and Updates
Periodically review your security policies and the performance of your automated workflow. Update them as your business needs evolve or new security threats emerge. Stay informed about the latest advancements in PDF protection technology.
Employee Training
Educate your employees about the importance of PDF security and how the automated system works. Ensure they understand their role in the secure document process, including how to handle documents that require manual intervention or exceptions.
Comparison Table: PDF Security Automation Methods
| Method | Pros | Cons | Best For |
|---|---|---|---|
| Manual Application | No cost, simple for single documents | Time-consuming, error-prone, inconsistent | Occasional, low-volume, non-critical documents |
| Desktop Software (Batch Processing) | Handles large volumes, customizable rules | Requires installation, potential cost, learning curve | Medium to large businesses with internal IT |
| Cloud-Based Services/APIs | Scalable, accessible anywhere, often integrates easily | Subscription costs, potential privacy concerns, reliance on vendor | Businesses of all sizes needing flexibility and integration |
| Custom Scripting | Highly tailored to specific needs, full control | Requires significant technical expertise, development time, ongoing maintenance | Large enterprises with unique requirements and development resources |