
The need to share sensitive information securely is paramount in today's digital landscape. Whether it's confidential business proposals, client data, or personal documents, ensuring that only authorized individuals can access them is critical. Implementing robust security measures directly into your applications can prevent unauthorized access and maintain data integrity.
For developers, this often means looking for tools that can handle encryption, access control, and other security features programmatically. My experience has shown that a well-chosen PDF security SDK can significantly streamline this process, offering a powerful way to manage document protection without reinventing the wheel.
Table of Contents
Understanding the PDF Security SDK
A PDF security SDK (Software Development Kit) is a collection of tools, libraries, and documentation that allows developers to add PDF security functionalities to their own applications. This typically includes features like password protection, encryption, digital signatures, and watermarking.
Instead of building complex encryption algorithms from scratch, developers can leverage the pre-built, tested, and optimized functions provided by an SDK. This not only saves development time but also ensures a higher level of security due to the expertise embedded within the SDK. A good pdf security sdk acts as a foundational layer for secure document management.
Core Functionalities Provided
At its core, a PDF security SDK enables developers to control access to PDF documents. This is primarily achieved through password-based protection, where a password is required to open or edit the document. More advanced SDKs also offer AES encryption, ensuring that even if a document is intercepted, its contents remain unreadable without the correct decryption key.
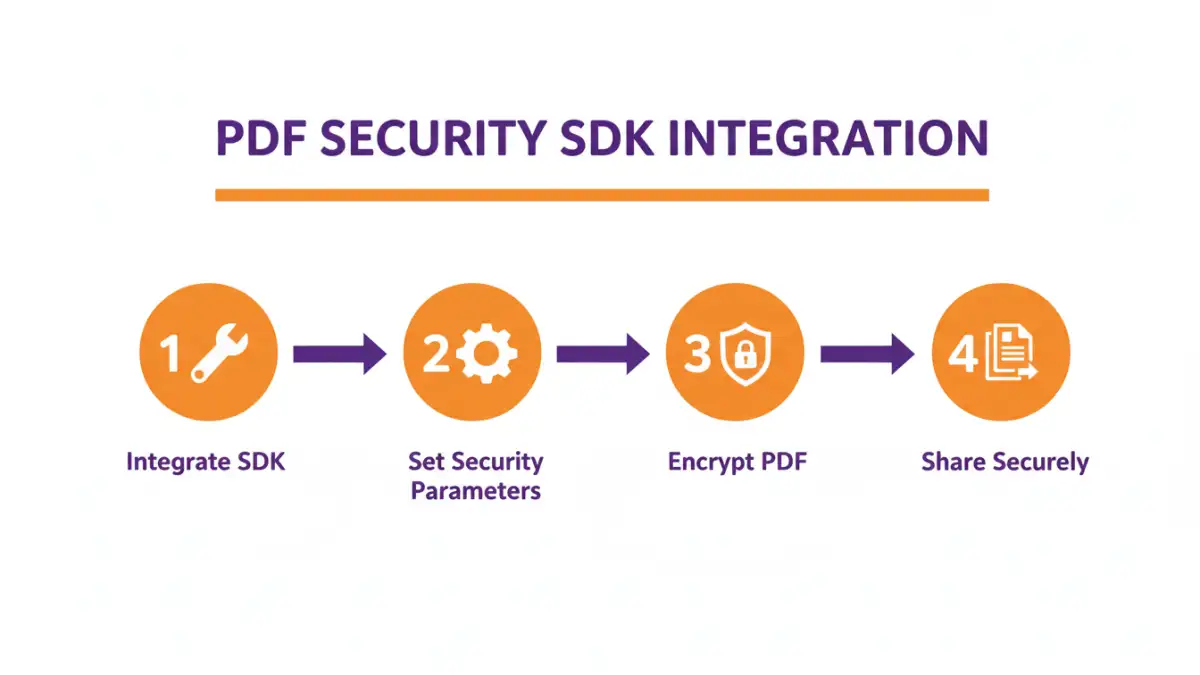
Integration Process
Integrating a PDF security SDK usually involves adding the SDK's libraries to your project and then calling its provided functions through your application's code. The exact steps will vary depending on the SDK and the programming language you are using, but the general workflow remains consistent.
Typically, you'll initialize the SDK, specify the PDF file you want to secure, set the desired security parameters (like passwords or encryption levels), and then execute the operation. The SDK handles the underlying PDF manipulation, returning a secured file or applying changes in place.
API Interaction Example
Imagine you need to encrypt a PDF before sending it to a client. Using a hypothetical Java-based PDF encryption SDK, the code might look something like this: `PdfSecurer securer = new PdfSecurer(); securer.encryptFile("path/to/input.pdf", "path/to/output.pdf", "client_password", EncryptionAlgorithm.AES_256);` This simple call abstracts away the complexities of AES-256 encryption, making secure document sharing much more accessible.
Key Features to Look For
When selecting a PDF security SDK, several features are crucial for robust document protection and secure document sharing. Beyond basic password protection, consider the encryption standards supported. Strong encryption algorithms like AES-256 are essential for high-level security.
Look for SDKs that offer granular permissions, allowing you to restrict actions like printing, copying text, or modifying the document, even after it's opened. Support for digital signatures is also vital for verifying document authenticity and integrity. Finally, consider the platform compatibility and ease of integration with your existing tech stack.
Real-World Implementation Scenarios
The applications for a PDF security SDK are vast. In a legal context, law firms can use it to protect client confidentiality agreements and case files before sharing them with opposing counsel or clients. Healthcare providers can encrypt patient records and medical reports to comply with HIPAA regulations.
Financial institutions can secure sensitive financial statements and transaction reports. E-commerce platforms might use it to protect invoices or order confirmations. Essentially, any business dealing with confidential or sensitive documents can benefit from integrating a robust pdf security sdk.
Best Practices for Secure Document Sharing
Beyond implementing technical security measures, effective secure document sharing relies on good practices. Educate your team on the importance of strong, unique passwords and secure password management. Implement multi-factor authentication wherever possible for accessing applications that handle sensitive documents.
Regularly review access permissions, revoking access for individuals who no longer require it. Utilize audit trails provided by your SDK or platform to track who accesses and modifies documents. This comprehensive approach ensures that your secure document sharing strategy is effective and resilient.
Comparison Table: PDF Security SDK Integration Methods
| Method | Pros | Cons | Ease of Integration | Scalability |
|---|---|---|---|---|
| Using a Dedicated PDF Security SDK | High security, advanced features (encryption, digital signatures), reliable performance, often well-documented | Can be costly, may require specific development skills, adds dependency | Moderate to High | High |
| Leveraging Built-in OS/Application Features | Free, readily available (e.g., OS-level encryption, Word/Excel password protection) | Limited PDF-specific features, often basic encryption, less control over permissions | High | Low to Moderate |
| Developing Custom Encryption Logic | Complete control, potentially free if using open-source libraries | Extremely complex, high risk of security vulnerabilities if not expertly implemented, time-consuming | Very Low | Moderate |
| Third-Party Online Tools | Quick, easy for one-off tasks, no installation required | Privacy concerns, limited features, potential data breaches, not suitable for sensitive or bulk operations | Very High | Low |