
Securing sensitive documents is a paramount concern for businesses and individuals alike. Whether you're developing an application that handles confidential client data or a personal tool for safeguarding important files, robust encryption is non-negotiable. For developers, integrating reliable security features often means leveraging specialized tools, and a well-chosen pdf encryption api can be a game-changer.
The challenge lies in finding an API that is not only powerful and flexible but also straightforward to integrate into existing workflows. Over my years in software development, I've encountered numerous scenarios where implementing secure document handling was critical. This guide aims to demystify the process, offering practical insights and a clear path forward for developers looking to enhance their applications with strong PDF security.
Table of Contents
Understanding PDF Encryption APIs
At its core, a PDF encryption API provides programmatic access to encrypt and decrypt PDF documents. This allows developers to embed security functionalities directly into their applications without needing to manually handle complex cryptographic algorithms or PDF manipulation.
Core Concepts
When you use a PDF encryption API, you're typically dealing with concepts like symmetric encryption (using a single key for both encryption and decryption, often a password) and standard algorithms like AES. The API abstracts away the low-level details, letting you specify the desired encryption level and the password or key to be used.
Integrating a PDF Encryption API

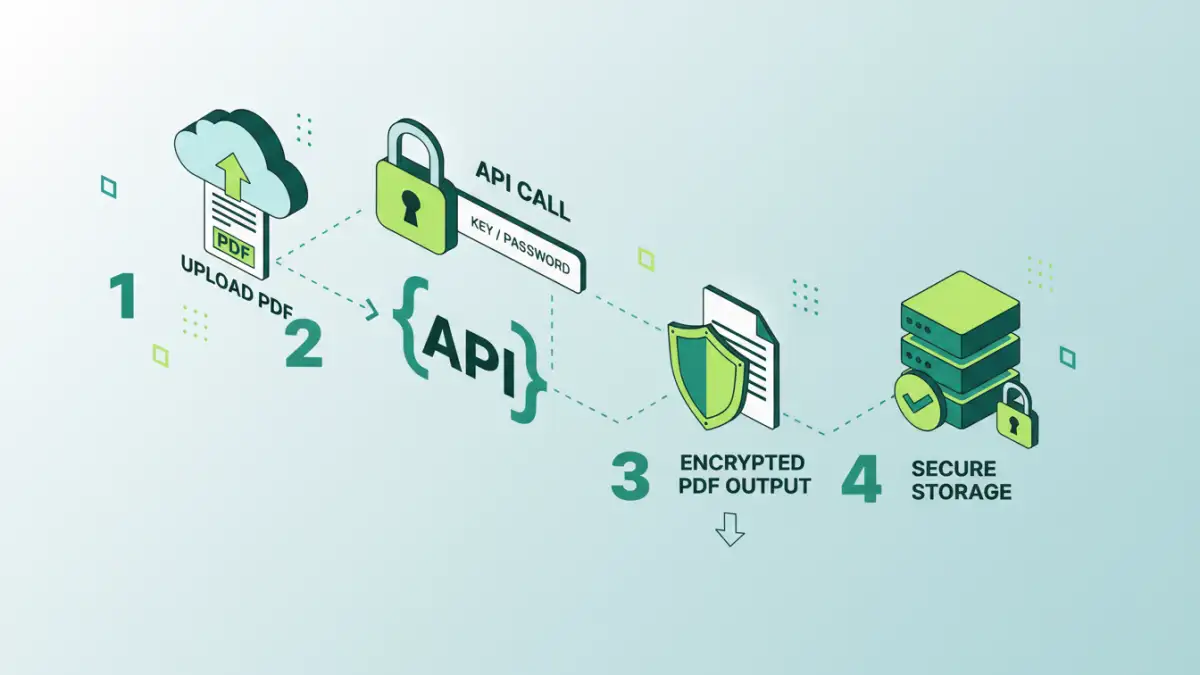
Integrating an API usually involves a few key steps. First, you'll need to choose an API provider or library that suits your needs. This might be a cloud-based service or a downloadable SDK. Once you have access, you'll typically make API calls from your application's backend or frontend code.
Example Workflow
A common workflow might look like this: your application receives a PDF file, sends it to the API endpoint with a specified password, receives the encrypted PDF back, and then stores or delivers it to the user. Decryption follows a similar process in reverse when a user needs to access the protected document.
Key Features to Look For
Not all PDF encryption APIs are created equal. When evaluating options, consider the breadth of features they offer. This includes support for different encryption standards (like AES-128, AES-256), the ability to set permissions (e.g., prevent printing or copying), and ease of use.
Security Standards
Ensure the API supports modern, strong encryption algorithms. AES-256 is generally considered the industry standard for robust security. The API should also clearly define how it handles password management and key rotation if applicable.
Best Practices for Secure Implementation
Implementing security features requires careful planning. Always use strong, unique passwords and avoid hardcoding them directly into your source code. Instead, use environment variables or secure secret management systems.
Handling Passwords
For user-facing encryption, guide users to create strong passwords. If your application manages passwords programmatically, implement secure storage solutions. Regularly review and update your security protocols to stay ahead of potential threats.
Alternatives and Considerations
While a dedicated PDF encryption API is often the most robust solution, there might be simpler, built-in options available depending on your platform or programming language. Some libraries offer basic PDF manipulation, including password protection, though they might lack advanced features.
Comparison Table: PDF Security Integration Methods
| Method | Pros | Cons | Use Case |
|---|---|---|---|
| Dedicated PDF Encryption API | High security, advanced features (permissions), scalable, developer-friendly | Can be costly, requires integration effort | Enterprise applications, sensitive data handling |
| Built-in Library Functions | Often free, easier for basic tasks | Limited encryption strength, fewer features, platform-dependent | Simple password protection for personal use |
| Online PDF Tools | Convenient for one-off tasks, no installation | Privacy concerns, file size limits, less control | Occasional use, non-sensitive documents |
| Desktop PDF Software | Feature-rich, full control over encryption | Requires installation, can be expensive, not easily integrated into apps | Professional document management, offline security |
Extra tips before you try to pdf encryption api
First, confirm what kind of protection you are dealing with. Some PDFs require a password to open (user password), while others only restrict printing/copying/editing (owner password). The safest approach depends on which one you have.
For sensitive documents, prefer offline tools and avoid uploading confidential files to unknown websites. If you must use an online tool, read the privacy policy and delete uploaded files immediately after processing.
- Try a different PDF viewer (some apps cache old permissions)
- Re-download the file (corruption can cause false password errors)
- Check caps lock / keyboard layout for password entry
- Differentiate “permission password” vs “open password” prompts
- If it is not your file, request access from the owner