
Protecting digital content has become paramount in today's interconnected world. Creators and distributors of media files, from music and videos to e-books and software, face constant challenges in preventing unauthorized copying, sharing, and usage. Implementing robust Digital Rights Management (DRM) strategies is no longer an option but a necessity for safeguarding intellectual property and revenue streams.
As someone who has navigated the complexities of software development and digital asset protection for over a decade, I've seen firsthand how crucial effective DRM solutions are. It's about more than just encryption; it's about controlling how your digital assets are accessed and consumed. This article will guide you through the essential aspects of implementing DRM for your media files, ensuring your content remains secure and valuable.
Table of Contents
Understanding Digital Rights Management (DRM)
Digital Rights Management (DRM) refers to a set of technologies used by hardware manufacturers, publishers, and rights holders to control the use and distribution of digital content. The primary goal is to prevent piracy and unauthorized access, thereby protecting the intellectual property and commercial value of the media. This encompasses a wide range of media, including music, movies, software, e-books, and even images.
Core Objectives of DRM
At its heart, DRM aims to enforce the terms of a license agreement between the content provider and the consumer. This typically involves restricting actions such as copying, printing, sharing, or even viewing the content beyond the agreed-upon parameters. By setting these boundaries, creators can maintain better control over their digital assets and ensure they are distributed and consumed as intended.
Key Components of a DRM System

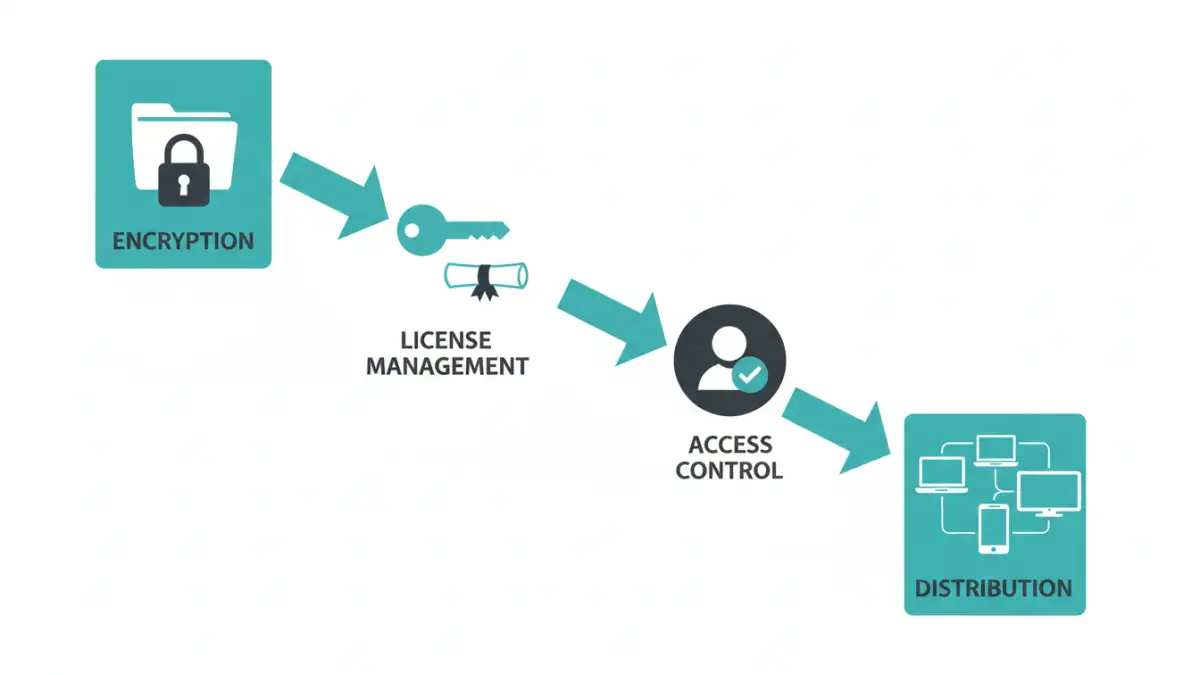
A comprehensive DRM system is built upon several interconnected components. Understanding these elements is crucial for effective implementation and management of your digital assets. These systems are designed to be robust and adaptable to various media types and distribution channels.
Encryption and Packaging
The first line of defense in any DRM system is encryption. Media files are encrypted to render them unreadable without the proper decryption key. This encrypted content is then often packaged into a specific format that can only be opened by authorized players or applications. This packaging process ensures that even if the file is obtained, it cannot be accessed without the necessary components.
License Management
Once a user purchases or obtains a license for the media, a license management system comes into play. This system issues and manages the decryption keys or tokens required to access the content. It tracks which users have licenses, the terms of those licenses (e.g., duration, number of devices), and ensures that access is granted only according to these permissions. This is a critical part of controlling user access.
Access Control Enforcement
The final piece of the puzzle is access control enforcement. This involves the end-user application or device that interacts with the DRM system. When a user attempts to access the media, this component verifies the license with the license server. If the license is valid and the user's actions comply with the terms, the content is decrypted and made available. This ensures that only legitimate users can consume the protected content according to the defined rules.
DRM Implementation Strategies
Implementing DRM can seem daunting, but there are various strategies and levels of complexity to consider. The best approach often depends on the type of media, the distribution model, and the desired level of control. From simple password protection to sophisticated content protection frameworks, the options are diverse.
Watermarking and Fingerprinting
Beyond encryption, watermarking and fingerprinting are valuable techniques. Digital watermarks are embedded within the media file itself and can be visible or invisible. They can identify the source or owner of the content, deterring unauthorized distribution. Fingerprinting involves embedding unique identifiers into each copy of the media distributed to different users. If a pirated copy surfaces, the fingerprint can trace it back to the original licensee, aiding in legal action.
DRM for Streaming Services
For streaming platforms, DRM is essential for preventing unauthorized downloads and sharing of content. Services like Netflix, Spotify, and Amazon Prime Video rely heavily on robust DRM solutions. These systems manage user authentication, session management, and content decryption in real-time, ensuring that content is only accessible through their authorized applications and devices for the duration of a valid subscription.
Choosing the Right DRM Solution
Selecting the appropriate DRM solution requires careful consideration of your specific needs. Factors such as the type of media, target audience, distribution channels, and budget will influence your decision. It's important to evaluate the security features, ease of integration, scalability, and the provider's reputation.
Evaluating Security and Features
When evaluating DRM solutions, look for strong encryption algorithms, secure license management, and robust access control mechanisms. Consider features like device limitations, geographical restrictions, print control, and the ability to revoke licenses. The solution should also be adaptable to future needs and emerging threats, providing a solid foundation for long-term media file security.
Integration and Scalability
The chosen DRM system should integrate seamlessly with your existing content delivery platforms and workflows. Scalability is also crucial; the system must be able to handle a growing library of content and an increasing number of users without performance degradation. A well-integrated and scalable DRM solution ensures smooth operations and a positive user experience.
Best Practices for Media File Security
Beyond implementing a DRM system, adopting best practices for overall media file security is vital. This holistic approach ensures that your valuable digital assets are protected from various threats. Consistent vigilance and up-to-date security measures are key to maintaining robust file security.
Regular Audits and Updates
Like any security system, DRM solutions require regular audits and updates to stay effective against evolving threats. Periodically review your DRM policies, check for vulnerabilities, and ensure your systems are patched with the latest security updates. Staying informed about new piracy methods and security advancements is also critical.
Educate Your Users
While technology plays a significant role, educating your users about the importance of content protection and responsible usage can also be effective. Clear terms of service and user guidelines can help prevent accidental infringements and foster a culture of respect for intellectual property. This user-centric approach complements technical measures, enhancing overall media file security.
Comparison Table: DRM Solution Types
| DRM Type | Pros | Cons | Ideal Use Case |
|---|---|---|---|
| Encryption with Password Protection | Simple, widely understood | Easily bypassed if password is shared | Small-scale distribution, internal use |
| License Server Based DRM | Robust control, flexible licensing | Complex to implement, requires infrastructure | Large-scale commercial distribution (movies, music) |
| Watermarking/Fingerprinting | Deters piracy, aids in tracking | Doesn't prevent access, can degrade quality | Preventing unauthorized sharing, content provenance |
| DRM Platforms (SaaS) | Managed service, scalable, feature-rich | Subscription costs, vendor lock-in | Most modern content providers, app developers |