
When we talk about protecting digital content, two terms often come up: Digital Rights Management (DRM) and standard file encryption. While both aim to secure information, they operate on fundamentally different principles and serve distinct purposes. Understanding these differences is crucial for anyone looking to safeguard their data or manage digital assets effectively. I've spent years working with various security protocols, and the nuances between these two are often overlooked, leading to misapplied solutions.
The core confusion arises because both methods involve making data inaccessible to unauthorized parties. However, the 'who' and 'why' behind that restriction are where they diverge significantly. Standard encryption is a technical process, while DRM is a business and legal framework enforced through technology.
Table of Contents
Understanding the Basics
At its heart, security for digital assets boils down to controlling access. Whether it's a personal document, a sensitive company report, or a copyrighted movie, the goal is to ensure only intended recipients can view, modify, or distribute it. This is where the paths of DRM and standard encryption begin to diverge, each offering a unique approach to achieving this control.
Purpose of Protection
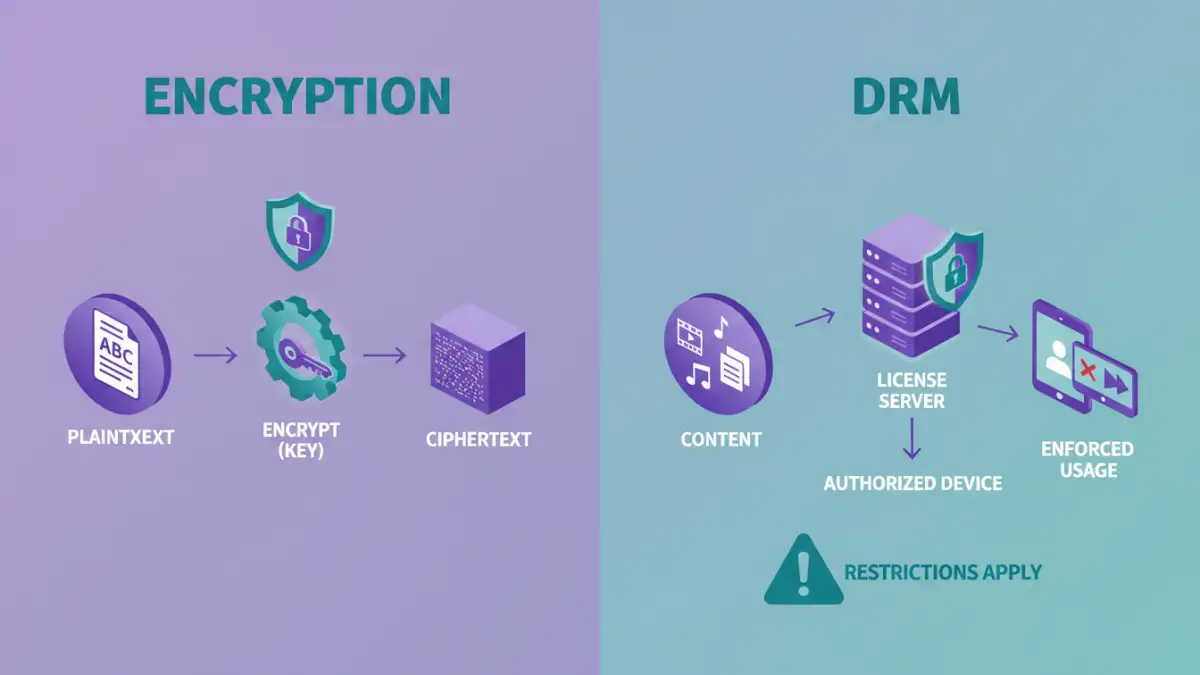
Standard file encryption is primarily about data confidentiality and integrity. Its main goal is to prevent unauthorized individuals from reading the content of a file, regardless of who they are or what their intentions might be. DRM, on the other hand, is focused on controlling how authorized users can interact with content, often for commercial purposes, enforcing licensing terms and preventing piracy.
Standard File Encryption Explained
Standard file encryption is a mathematical process that transforms readable data (plaintext) into an unreadable format (ciphertext) using an algorithm and a secret key. Only someone with the correct key can reverse this process and decrypt the data back into its original form. This is a fundamental technique used across many aspects of digital security, from securing emails to protecting hard drives.
When I implement file encryption for a client, the focus is purely on the technical barrier. If someone gets the key, they get the data. There are no granular permissions built into the encryption itself; it's an all-or-nothing proposition. Common examples include encrypting a ZIP file with a password or using full-disk encryption on a laptop.
How It Works
Encryption algorithms like AES (Advanced Encryption Standard) are widely used for their robust security. The strength of the encryption depends on the algorithm used and, crucially, the complexity and secrecy of the encryption key. Without the key, even with the most advanced computing power, decrypting the data is practically impossible within a reasonable timeframe. This makes it an excellent method for securing data at rest or in transit.
DRM Technology Explained
Digital Rights Management (DRM) is a broader system that uses a combination of technologies to control the use, modification, and distribution of copyrighted digital works. Unlike standard encryption, which often protects the file itself, DRM typically wraps content with layers of access control and usage policies. This is commonly seen with digital music, e-books, streaming video, and software.
I've encountered DRM extensively when dealing with media distribution platforms. The goal isn't just to prevent unauthorized copying but to dictate exactly how a piece of content can be consumed. For instance, a movie purchased through a streaming service might be DRM-protected to only play on authorized devices or for a limited time, even after purchase. This involves more than just a simple encryption key; it often includes license servers, device authentication, and sophisticated watermarking.
Components of DRM
DRM systems often involve multiple components: encryption to protect the content, a license server to issue usage rights, and client software or hardware that enforces these rights. This allows for fine-grained control over actions like copying, printing, or sharing, based on the terms defined by the content owner.
Key Differences Between DRM and Encryption
The fundamental difference lies in their scope and objective. Standard encryption is a technical tool for data confidentiality. DRM is a business strategy that *uses* encryption as one of its tools, but its primary goal is to manage and enforce rights over content. I see DRM as a gatekeeper with specific rules, while encryption is a locked vault. You need the key for the vault, but you need permission and perhaps a special key to get past the gatekeeper.
Another significant distinction is the target audience and control mechanism. Standard encryption typically protects against external threats – hackers, unauthorized access. DRM, however, often controls the actions of legitimate, authorized users, preventing them from exceeding their permitted usage rights. This is why DRM can sometimes feel restrictive to end-users.
Control vs. Confidentiality
Confidentiality is the main concern for standard encryption; ensuring only authorized parties can access the data. With DRM, the concern is broader: it's about controlling the 'digital rights' associated with the content – who can view it, on what devices, for how long, and whether they can share or modify it. This makes DRM a more complex system, integrating technology with legal and business policies.
Practical Use Cases
Standard file encryption is ideal for protecting sensitive personal or business data where the primary concern is preventing unauthorized access. This includes encrypting financial records, confidential emails, or intellectual property before it's shared. It's about securing the data itself.
DRM technology is employed when the creator or distributor wants to maintain control over how their content is used after it's distributed. This is prevalent in the entertainment industry (movies, music), publishing (e-books, digital magazines), and software licensing. It's about managing the lifecycle and usage of the digital asset.
Comparison Table
| Feature | Standard File Encryption | DRM Technology |
|---|---|---|
| Primary Goal | Data Confidentiality & Integrity | Content Usage Control & Rights Management |
| Mechanism | Mathematical algorithms and keys | Encryption, licensing, access control policies, device authentication |
| Scope | Secures the file/data itself | Manages how authorized users interact with content |
| Control Granularity | All or nothing (access granted/denied) | Fine-grained control over usage (view, copy, print, duration) |
| Use Cases | Securing sensitive documents, emails, data at rest/in transit | Digital media distribution (movies, music, e-books), software licensing |
| Enforcement | Key possession | License servers, client-side enforcement, device restrictions |
| Focus | Preventing unauthorized access | Preventing unauthorized use/distribution by authorized users |