When dealing with sensitive documents, ensuring their security is paramount. Password protection is a common first step, but the underlying encryption method used by PDF software can significantly impact how robust that protection truly is. For years, developers and users alike have relied on different algorithms to scramble document data, making it unreadable without the correct key or password. Understanding these protocols is key to making informed decisions about document security.
My work often involves ensuring data integrity and security, and I've seen firsthand how the choice of encryption can make or break a system's defense. The evolution of these protocols reflects the ongoing battle between those seeking to protect information and those trying to access it illicitly. This makes a comparison between older and newer standards, like RC4 and AES, particularly insightful.
Table of Contents
Introduction to PDF Encryption
PDF encryption is the process of encoding the content of a PDF file to prevent unauthorized access. This is typically achieved by requiring a password to open or manipulate the document. The strength of this protection hinges on the cryptographic algorithm employed by the PDF software. Different algorithms offer varying levels of security, speed, and complexity.
Modern PDF applications often support multiple encryption methods, giving users choices based on their specific needs. However, not all encryption is created equal. Some older methods, while once considered secure, have known vulnerabilities that can be exploited with today's computing power.
Why Encrypt PDFs?
The primary reasons for encrypting PDFs include protecting confidential business data, safeguarding personal information, complying with regulatory requirements, and preventing unauthorized distribution of sensitive documents. Whether it's financial reports, legal contracts, or private correspondence, encryption adds a critical layer of security.
Understanding RC4 Encryption

RC4 (Rivest Cipher 4) is a stream cipher that was widely used for its speed and simplicity. It was one of the earliest widely adopted encryption algorithms for securing data, including in early PDF specifications. RC4 works by generating a pseudorandom stream of bits that is then XORed with the plaintext to produce ciphertext.
While RC4 was revolutionary for its time, it has significant weaknesses that have become apparent over the years. Cryptanalytic attacks have demonstrated that the output of RC4 is not truly random, and patterns can emerge that allow attackers to recover the key or parts of the plaintext, especially with large amounts of data. This has led to its deprecation in many modern security contexts.
RC4 in PDF Security
In the context of PDFs, RC4 was often used with key lengths of 40-bit or 128-bit. The 40-bit version, in particular, is considered very weak by today's standards and can be broken relatively quickly. The 128-bit version offered better protection but still suffers from the fundamental vulnerabilities of the RC4 algorithm itself.
Exploring AES Encryption
AES (Advanced Encryption Standard) is a symmetric block cipher that has become the gold standard for data encryption worldwide. It was adopted by the U.S. government in 2002 and is now used extensively by governments and industries globally. AES operates on fixed-size blocks of data (128 bits) and supports key sizes of 128, 192, and 256 bits.
AES is known for its robust security, efficiency, and resistance to known cryptanalytic attacks. Unlike stream ciphers like RC4, AES is a block cipher, meaning it encrypts data in fixed-size chunks. The algorithm involves multiple rounds of substitution, permutation, and mixing operations, making it extremely difficult to break without the correct key.
AES in PDF Security
Modern PDF specifications widely support AES encryption, typically AES-128 and AES-256. These provide a much higher level of security compared to RC4. When you encrypt a PDF using AES, the document's content is scrambled using a strong algorithm that is considered secure against even sophisticated attacks, provided a strong password is used.
Key Differences and Use Cases
The fundamental difference lies in their design and security. RC4 is a stream cipher with known vulnerabilities, making it unsuitable for modern high-security applications. AES, on the other hand, is a secure block cipher that is highly resistant to attacks and is the recommended standard for most encryption needs.
For PDF security, RC4 (especially 40-bit) is largely obsolete and should be avoided. If a PDF file is encrypted with RC4, it's advisable to re-encrypt it using AES. AES-128 and AES-256 are the preferred choices for securing PDF documents, offering strong protection for sensitive information.
PDF Security Standards Evolution
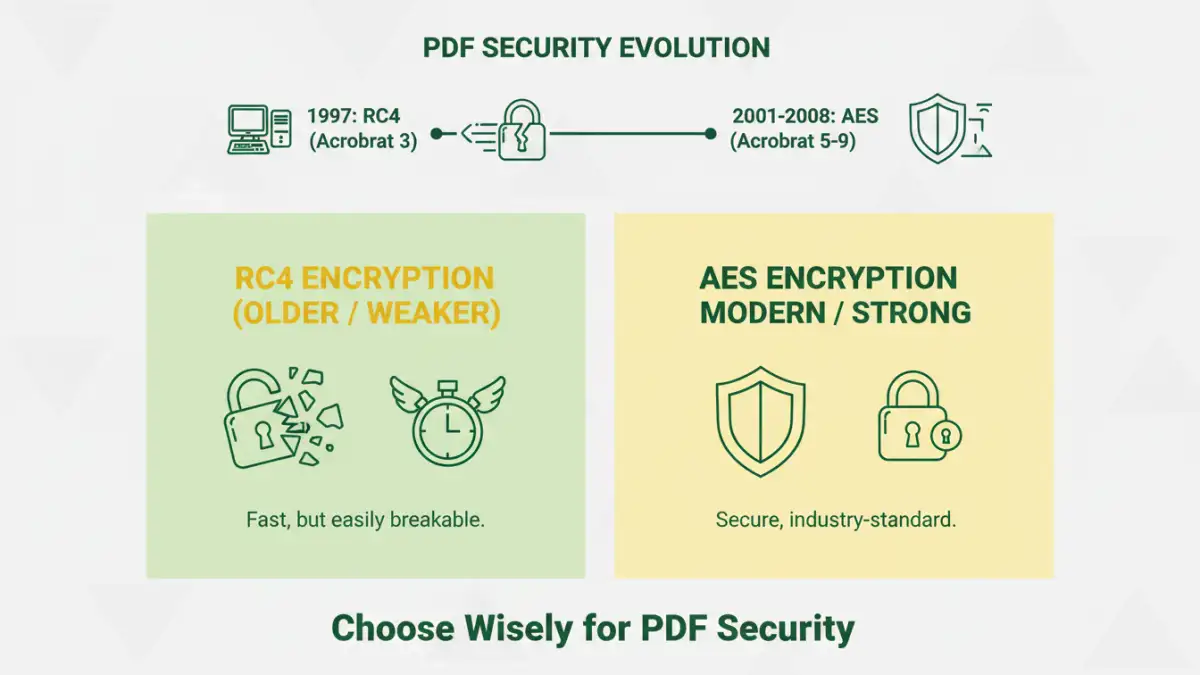
The evolution of pdf encryption protocols mirrors the advancements in cryptography. Early PDF versions relied on weaker algorithms like RC4 to provide basic password protection. As computing power increased and cryptanalysis techniques improved, the need for stronger encryption became evident.
Adobe, the creator of the PDF format, has progressively updated its security standards. The shift towards AES encryption in PDF specifications (starting around PDF 1.4) marked a significant leap forward in document security. Today, most reputable PDF software adheres to these modern standards, ensuring that documents can be protected with algorithms that stand up to current threats.
Comparison Table: RC4 vs. AES for PDF Encryption
| Feature | RC4 Encryption (PDF) | AES Encryption (PDF) |
|---|---|---|
| Algorithm Type | Stream Cipher | Block Cipher |
| Key Sizes Supported | 40-bit, 128-bit | 128-bit, 192-bit, 256-bit |
| Security Level | Low to Moderate (40-bit is very weak) | High to Very High |
| Known Vulnerabilities | Yes, significant | No known practical attacks (with proper implementation) |
| Performance | Generally faster (older hardware) | Efficient on modern hardware, potentially slower on very old systems |
| Current Recommendation | Avoid, obsolete | Recommended for all sensitive documents |
| Use Cases | Legacy systems, older PDFs | Modern document security, sensitive data protection |