
Working with password-protected documents can be frustrating, especially when you genuinely need access but have forgotten the password or received a file from someone else. This is a common scenario, and understanding the underlying technology, like OpenDocument encryption, becomes crucial. My experience has shown that while encryption is vital for security, the process of managing or recovering access needs to be approached with a clear understanding of the methods involved.
The OpenDocument Format (ODF) is widely used, particularly with open-source office suites like LibreOffice and OpenOffice. When you encrypt a document in this format, you're essentially scrambling its contents so that only someone with the correct password can unscramble and read it. This process is fundamental to secure document handling, protecting sensitive information from unauthorized eyes. However, life happens, and sometimes you need to bypass this protection.
Table of Contents
Understanding OpenDocument Encryption
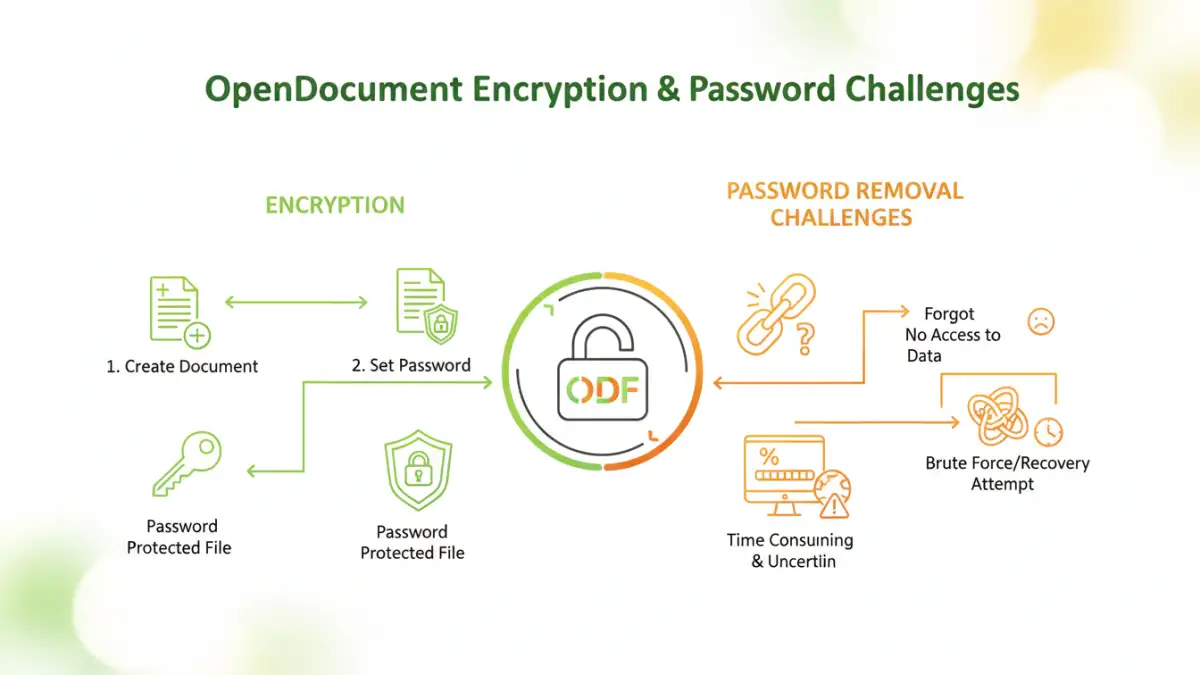
OpenDocument encryption typically uses symmetric encryption algorithms. This means the same key (derived from your password) is used to both encrypt and decrypt the file's content. When you set a password, the software generates a cryptographic key based on that password. This key is then used to transform the document's data into an unreadable format. Without the correct password, the key cannot be derived, rendering the document inaccessible.
Key Concepts
The strength of the encryption directly depends on the password's complexity and the algorithm used by the software. Strong passwords, combining uppercase and lowercase letters, numbers, and symbols, make it significantly harder for brute-force attacks to guess the password and derive the encryption key. File encryption methods vary, but ODF generally aims for robust protection.
Why is Encryption Important?
In today's digital landscape, protecting sensitive information is paramount. Whether it's personal financial data, confidential business documents, or private correspondence, encryption acts as a vital barrier against unauthorized access. It ensures that even if a file falls into the wrong hands, the data remains unintelligible without the correct password. This is a cornerstone of secure document handling.
Password Removal Methods
It's important to preface this section by stating that attempting to remove passwords from documents you do not own or have legitimate access to can have legal and ethical implications. These methods are generally intended for situations where you have forgotten the password to your own file or have received a file with a password you were given but no longer have. There isn't a single magic bullet for all password removal scenarios, as the effectiveness depends heavily on the type of password set and the software used.
The Browser Trick (for Owner Passwords)
One of the more ingenious methods, often referred to as the 'browser trick,' can sometimes work for documents that were encrypted using only an 'owner password' in older versions or certain implementations of ODF (though this is less common now). This method involves renaming the file extension to `.zip` and then extracting its contents. Inside, you'll find an XML file (like `content.xml`). If the password was only for ownership and not for encrypting the content itself, you might be able to edit this XML file, remove the password protection tags, and then re-zip the contents, renaming it back to `.odt`. However, this is highly dependent on the specific encryption applied and often fails with stronger, content-level encryption.
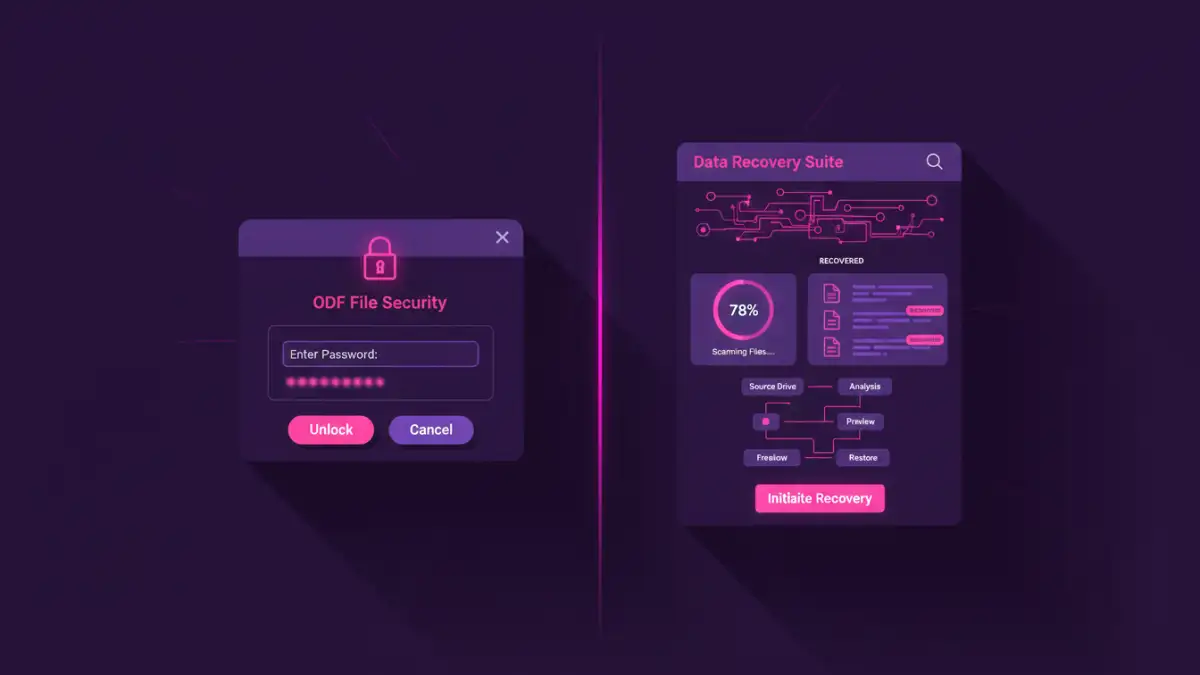
Using Online Decryption Tools
Numerous online services claim to remove passwords from various document types, including ODF files. These tools typically work by uploading your encrypted file, and their servers attempt to decrypt it. While convenient and often free for basic use, there are significant privacy and security concerns. You are entrusting your sensitive data to a third-party service, and there's no guarantee of its security or that your files won't be misused. Furthermore, their effectiveness can be limited, especially against strong encryption.
Desktop Software Solutions
For more robust solutions, dedicated desktop software can be used. Some programs are designed specifically for password recovery or removal for various file formats. These might employ brute-force attacks (trying many password combinations) or dictionary attacks (using lists of common words). This process can be time-consuming and computationally intensive, often requiring a powerful computer and considerable patience. Some software might offer specialized ODF decryption capabilities. Again, ensure you are using legitimate software for your own files.
Best Practices for Secure Document Handling
While understanding password removal is useful, the best approach is always strong password security and proper document handling from the outset. Use strong, unique passwords for your encrypted documents. Consider using a password manager to generate and store complex passwords securely. Regularly back up your important files, and keep these backups in a secure location. If you're sharing sensitive documents, explore secure sharing platforms that offer end-to-end encryption rather than relying solely on document-level passwords.
Final Thoughts
OpenDocument encryption provides a valuable layer of security for your digital documents. While methods for password removal exist, they often come with limitations, privacy risks, or require significant effort. Prioritizing strong password creation and secure handling practices is always the most effective strategy for protecting your sensitive information. Understanding the nuances of file encryption methods can empower you to make informed decisions about how you protect your data.
Comparison Table: Document Security Methods
| Method | Pros | Cons | Best For |
|---|---|---|---|
| Owner Password (ODF) | Simple to set, prevents basic editing/viewing | Easily bypassed by some tools, doesn't encrypt content strongly | Quickly preventing casual access |
| Content Encryption (ODF) | Strong encryption, secures entire document content | Requires strong password, removal is difficult | Protecting sensitive data from unauthorized access |
| Online Decryption Tools | Convenient, often free for basic use | Privacy/security risks, limited effectiveness | Non-sensitive files, quick one-off needs (with caution) |
| Desktop Password Recovery Software | Can be powerful, handles various encryption types | Time-consuming, requires technical knowledge, potential cost | Recovering forgotten passwords for owned files |
| Password Managers | Generate and store strong, unique passwords securely | Requires setup, subscription cost for advanced features | Managing all passwords for various encrypted files and services |