
The way we handle sensitive information is constantly being reshaped by technological advancements and evolving threat landscapes. For years, the core principles of protecting digital documents have revolved around strong passwords and robust encryption algorithms. However, the sophistication of cyberattacks and the increasing volume of data demand a continuous evolution in how we secure our most critical files.
As someone who has navigated the complexities of software development and data protection for over a decade, I've seen firsthand how crucial effective document security is. It's not just about compliance; it's about safeguarding intellectual property, personal privacy, and business continuity. The challenges are growing, but so are the innovative solutions.
Table of Contents
Emerging Encryption Technologies
The bedrock of document security has always been encryption technology. While AES-256 remains a strong standard, the industry is exploring new frontiers. Homomorphic encryption, for instance, allows computations on encrypted data without decrypting it first. This has profound implications for cloud security and data processing, enabling sensitive information to remain protected even while being analyzed.
Another area of active development is post-quantum cryptography (PQC). As quantum computers become more powerful, they pose a threat to current encryption methods. Researchers are developing new algorithms resistant to quantum attacks, aiming to ensure data remains secure against future computational capabilities.
Advanced Encryption Standards
Beyond AES, there's a continuous push for more efficient and secure algorithms. Lattice-based cryptography and code-based cryptography are showing promise in PQC research. The goal is to create encryption that is not only secure against today's threats but also resilient against the computational power of tomorrow.
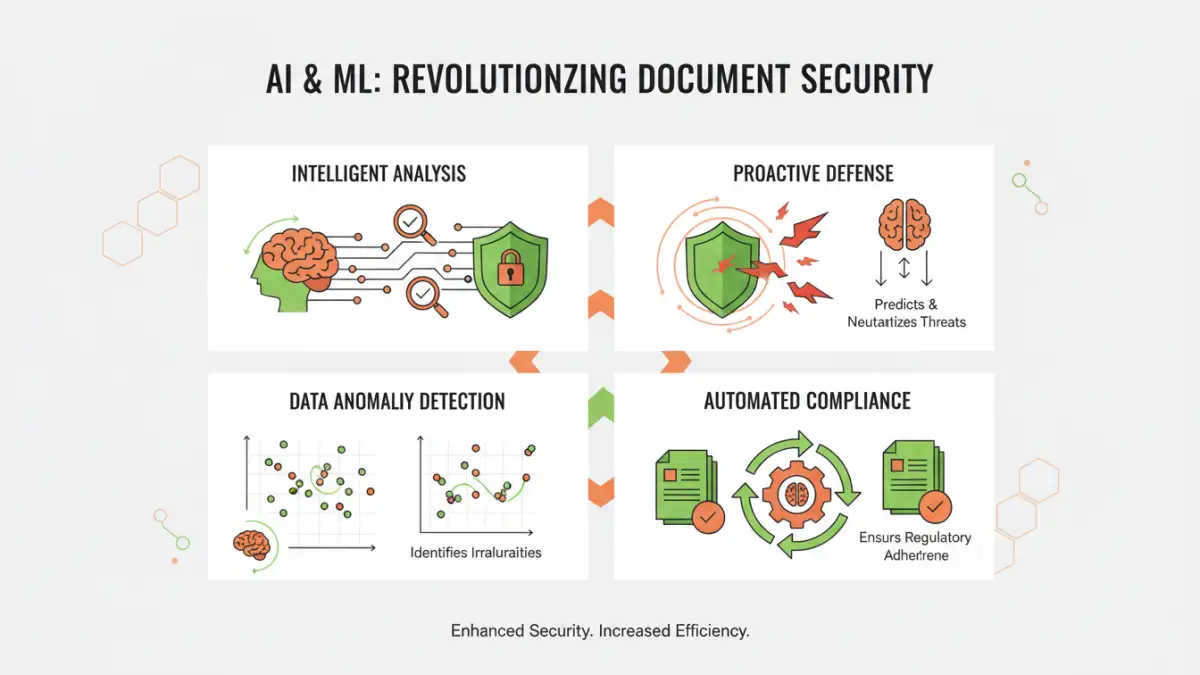
The Impact of AI and Machine Learning

Artificial intelligence and machine learning are revolutionizing many sectors, and document encryption is no exception. AI can enhance threat detection, identifying anomalous access patterns or potential breaches in real-time. It can also automate key management, a notoriously complex aspect of encryption, making it more robust and less prone to human error.
Furthermore, AI can analyze vast datasets to identify vulnerabilities in existing encryption protocols or predict future attack vectors. This proactive approach is vital for staying ahead of sophisticated adversaries. The integration of AI promises more intelligent and adaptive security systems.
AI-Powered Threat Detection
Machine learning algorithms can be trained to recognize patterns indicative of data exfiltration or unauthorized access attempts. This allows security systems to flag suspicious activities far faster than traditional rule-based systems, providing an extra layer of defense for sensitive documents.
Cloud-Native Encryption Strategies
With the widespread adoption of cloud computing, securing data in cloud environments is paramount. Cloud-native encryption strategies focus on integrating security directly into cloud infrastructure and services. This includes client-side encryption, where data is encrypted before it leaves the user's device, ensuring the cloud provider never has access to the plaintext.
Key management services (KMS) offered by cloud providers are also becoming more sophisticated. These services allow for granular control over encryption keys, ensuring that only authorized applications and users can access specific data. The future lies in seamless, integrated encryption that doesn't impede workflow but provides robust protection.
Client-Side vs. Server-Side Encryption
Understanding the difference is crucial. Client-side encryption offers the highest level of privacy as the data is encrypted before upload, meaning the cloud provider cannot decrypt it. Server-side encryption is managed by the provider, offering convenience but with less control for the user over the keys.
Preparing for Quantum Computing
The advent of quantum computing presents a significant challenge to current cryptographic standards. Shor's algorithm, for example, can break widely used public-key cryptosystems like RSA and ECC. This means that data encrypted today could be vulnerable to decryption by a quantum computer in the future.
The transition to post-quantum cryptography (PQC) is a major undertaking. Governments and industry bodies are working to standardize new algorithms that are resistant to quantum attacks. Organizations need to start planning this transition now to ensure long-term data security. The future document encryption landscape will undoubtedly be shaped by this shift.
The NIST PQC Standardization Process
The National Institute of Standards and Technology (NIST) is leading the charge in standardizing PQC algorithms. Their ongoing process involves rigorous evaluation of candidate algorithms from around the world to identify those that are both secure and practical for widespread adoption.
Balancing Security and User Experience
Historically, strong security measures have often come at the cost of user convenience. Complex password policies, multi-factor authentication prompts at every step, and lengthy encryption/decryption processes can frustrate users and lead to workarounds that compromise security. The future of document encryption hinges on finding a better balance.
Biometric authentication, seamless integration with existing workflows, and context-aware security policies are key. For instance, requiring stronger authentication only when accessing highly sensitive data from an untrusted network. The goal is to make robust security feel almost invisible to the end-user.
Biometric Authentication Integration
Fingerprint scanners, facial recognition, and voice biometrics offer a convenient and secure alternative to traditional passwords. Integrating these into document access and encryption workflows can significantly improve both security and user experience.
The Broader Data Security Outlook
The data security outlook is one of increasing complexity and interconnectedness. As more data is generated and stored, the attack surface expands. The future of document protection will involve a multi-layered approach, combining advanced encryption, AI-driven threat intelligence, secure cloud practices, and robust key management.
Regulatory compliance, such as GDPR and CCPA, will continue to drive the need for strong data protection measures. Organizations that proactively adopt advanced encryption technologies and adapt to emerging threats will be best positioned to safeguard their valuable information. The evolution of encryption technology is a continuous journey.
Key Encryption Technologies Comparison
| Technology | Primary Use Case | Security Level | Maturity | Future Potential |
|---|---|---|---|---|
| AES-256 | Symmetric data encryption | Very High | Mature | Standard for current needs |
| RSA/ECC | Asymmetric encryption, key exchange | High (Vulnerable to Quantum) | Mature | Being replaced by PQC |
| Homomorphic Encryption | Computation on encrypted data | High | Emerging | Revolutionary for cloud processing |
| Post-Quantum Cryptography (PQC) | Quantum-resistant encryption | High (Theoretical) | Developing | Essential for future security |
| End-to-End Encryption (E2EE) | Secure communication/storage | Very High | Mature | Core for privacy-focused apps |