
When dealing with sensitive information, ensuring its security during transit is paramount. This becomes even more complex when those documents need to cross international borders. As a software engineer who's spent over a decade building and securing systems, I've seen firsthand how the legal frameworks surrounding data transmission can be a minefield, especially when encryption is involved.
The challenge isn't just about choosing the right encryption method for your PDF files; it's about understanding the legal obligations tied to sending these encrypted documents to recipients in different countries. Different jurisdictions have varying regulations regarding data privacy, encryption standards, and cross-border data flow. Failing to comply can lead to significant penalties, reputational damage, and loss of trust.
Table of Contents
Understanding the Basics of International Data Transfer
Sending data across borders has always involved navigating a complex web of rules. For encrypted PDF transmissions, this means considering not only the technical security of the file but also the legal standing of the transfer itself. Each country has its own approach to data sovereignty and privacy.
My experience shows that a common oversight is assuming that strong encryption automatically absolves you of all legal responsibility. While encryption is a critical component of security, it doesn't negate the need to understand the regulations governing the movement of data, especially personal or sensitive information.
Cross-Border Data Flow Nuances
The fundamental issue is that data doesn't respect physical borders. When you send an encrypted PDF, the data within it might pass through servers or be subject to laws in multiple countries. Understanding these nuances is the first step toward ensuring lawful and secure transmission.
Key Legal Frameworks and Regulations
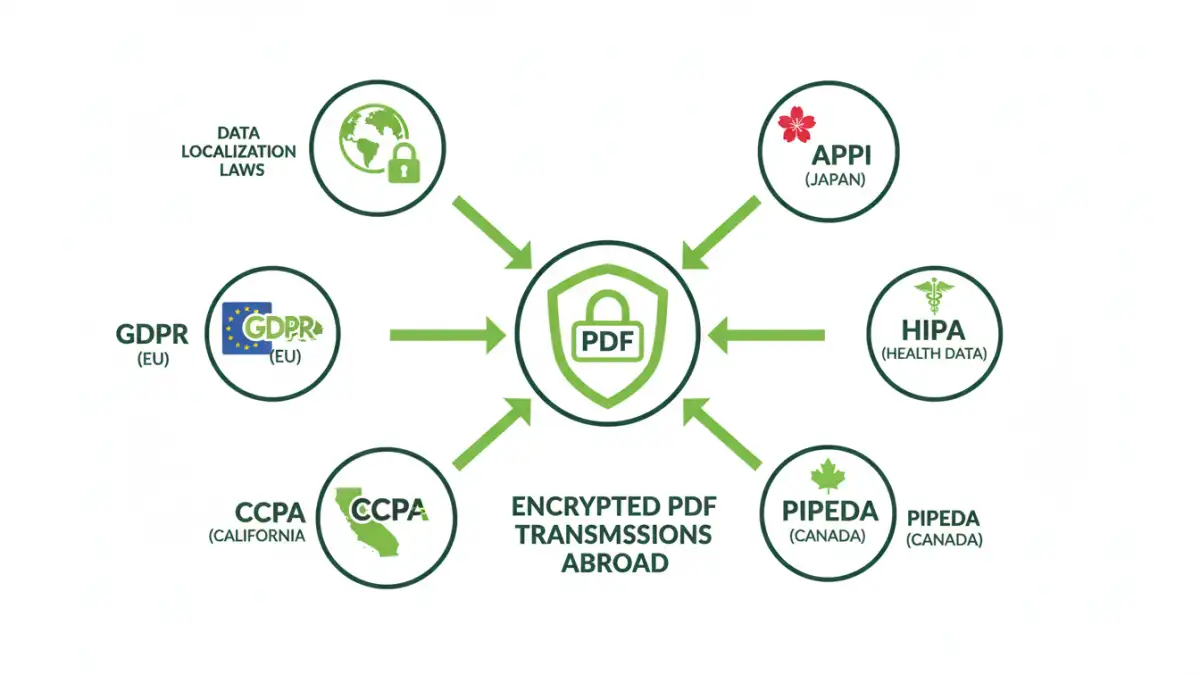
The global landscape of data protection is diverse. Major regulations like GDPR in Europe, CCPA in California, and various national data localization laws create specific obligations for businesses. These often dictate how personal data must be handled, protected, and, crucially, transferred.
For instance, GDPR has strict rules about transferring personal data outside the EU/EEA. While it doesn't outright ban such transfers, it requires specific safeguards, such as adequacy decisions, standard contractual clauses, or binding corporate rules. This directly impacts how you might send an encrypted PDF containing personal data to a European recipient.
Impact of Data Localization Laws
Some countries mandate that certain types of data must remain within their borders. While encrypted PDFs can offer a layer of protection, they don't always bypass these localization requirements. It's essential to know if the recipient's country has such laws and how they apply to your specific data and transmission method.
Encryption Standards and Legal Acceptance
Not all encryption is created equal in the eyes of the law. While robust, end-to-end encryption is generally favored, some jurisdictions might have specific requirements or preferences regarding encryption algorithms and key lengths. This is particularly relevant in industries like finance and healthcare.
I've worked on projects where we had to adapt encryption protocols based on the target regions' legal and industry-specific standards. It's not just about making it unreadable; it's about ensuring the method used is legally recognized and accepted for the type of data being protected.
End-to-End vs. At-Rest Encryption
For transmissions abroad, end-to-end encryption is typically the gold standard, ensuring that only the sender and intended recipient can decrypt the PDF. At-rest encryption protects data while it's stored, but it doesn't necessarily cover the transit phase as robustly. Understanding this distinction is vital for meeting legal requirements for secure digital communication.
Strategies for Ensuring Compliance
Achieving compliance for encrypted PDF transmissions abroad requires a multi-faceted approach. It starts with a thorough risk assessment of the data being sent and the recipient's location. Implementing strong encryption is non-negotiable, but it must be paired with awareness of international data transfer rules.
Leveraging secure platforms that offer built-in compliance features can significantly ease the burden. This might include tools that handle data transfer agreements or provide audit trails for transmissions. Consulting with legal counsel specializing in international data privacy is also a prudent step.
Due Diligence and Documentation
Thorough due diligence on your recipients and their data handling practices is crucial. Maintaining clear documentation of your security measures, encryption methods, and data transfer justifications is essential for demonstrating compliance if audited. This forms a vital part of your pdf data security abroad strategy.
Common Pitfalls to Avoid
One of the most common mistakes is assuming that password protection equals legal compliance for sensitive data transfer. While password-protected PDFs add a layer of security, the password itself needs to be transmitted securely, and the underlying encryption strength matters.
Another pitfall is relying on outdated information. Data privacy laws are constantly evolving. What was compliant last year might not be today. Continuous monitoring and updating of your policies and practices are essential for maintaining ongoing global compliance for pdf documents.
Insecure Password Transmission
If you transmit a password-protected PDF, the method used to send the password must be equally secure. Sending a password via plain text email alongside the encrypted file defeats the purpose of encryption. Separate, secure channels should be used for password exchange.
Comparison Table: Secure PDF Transmission Methods Abroad
| Method | Security Level | Legal Considerations | Ease of Use | Best For |
|---|---|---|---|---|
| Password-Protected PDF (Separate Password Transmission) | High (with strong password & secure channel) | Varies by jurisdiction; ensure password transmission is compliant | Moderate | General sensitive documents |
| End-to-End Encrypted Email Services | Very High | Generally well-accepted; check sender/recipient jurisdiction laws | High | Confidential communications, legal documents |
| Secure File Transfer Services (SFTP/Cloud) | High to Very High | Requires service provider compliance verification (e.g., GDPR, HIPAA) | Moderate to High | Large files, regular transfers, business-critical data |
| Encrypted Cloud Storage with Sharing Links | High (depending on platform security) | Ensure provider's data handling meets legal standards; access controls are key | High | Collaborative work, document sharing |