
The digital landscape is constantly evolving, and with it, the sophistication of threats against our sensitive information. As we look towards the future, particularly with the advent of quantum computing, the methods we currently use for securing our documents might become obsolete. This shift necessitates a proactive approach to data protection, ensuring our information remains safe not just today, but for decades to come.
Understanding these emerging challenges and the technologies designed to combat them is crucial for anyone handling confidential data. From personal records to corporate intellectual property, the integrity and privacy of our digital assets depend on robust security measures that can withstand future advancements.
Table of Contents
Understanding Current Document Security
For years, we've relied on well-established encryption algorithms like AES and RSA to safeguard our digital documents. These methods have served us well, providing a strong defense against brute-force attacks and unauthorized access. The effectiveness of this document security encryption hinges on the computational difficulty of solving complex mathematical problems.
However, the digital world is not static. Malware, phishing attacks, and insider threats are constant challenges that require vigilant security practices. While current encryption is robust against today's computing power, a new paradigm is on the horizon that threatens to undermine it.
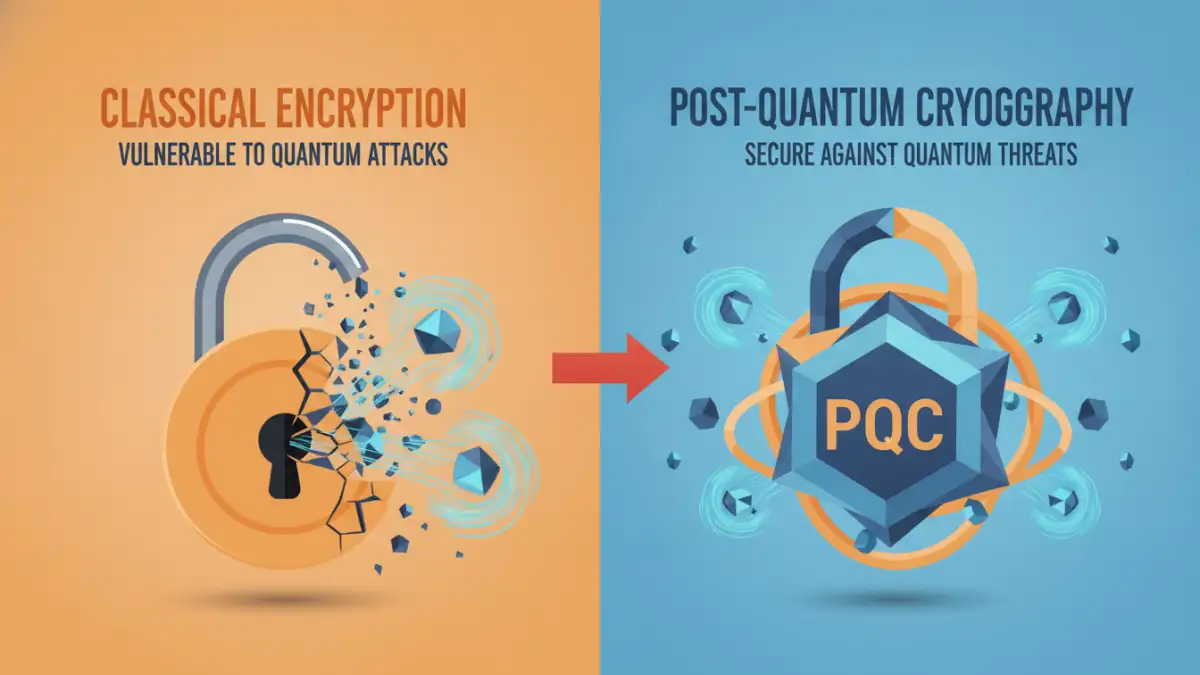
The Limitations of Classical Encryption
Classical encryption algorithms are designed to be resistant to the computational power of today's computers. For instance, breaking RSA encryption would require an infeasible amount of time and resources using current technology. This has made it a reliable cornerstone for protecting sensitive files and communications.
The Quantum Computing Threat

The development of quantum computers represents a significant leap in computational power. Unlike classical computers that use bits representing 0 or 1, quantum computers use qubits that can represent 0, 1, or both simultaneously. This allows them to perform certain calculations exponentially faster.
For cryptography, this is a game-changer. Algorithms like Shor's algorithm, designed to run on a quantum computer, can efficiently factor large numbers, effectively breaking many of the public-key cryptosystems, such as RSA, that underpin our current security infrastructure. This means that documents encrypted today using these vulnerable methods could be decrypted by a sufficiently powerful quantum computer in the future.
Introduction to Quantum Encryption
Quantum encryption, specifically Quantum Key Distribution (QKD), offers a fundamentally different approach to secure communication. Instead of relying on mathematical complexity, QKD leverages the principles of quantum mechanics to ensure that any attempt to eavesdrop on a key exchange will inevitably disturb the quantum state, alerting the legitimate users.
This inherent property of quantum mechanics makes QKD theoretically unhackable. By using photons to transmit cryptographic keys, any interception will cause detectable changes, ensuring the integrity of the key exchange. This provides a level of security that classical encryption cannot match against future threats.
Post-Quantum Cryptography Explained
While QKD is promising, its implementation can be complex and requires specialized hardware. A more immediate and practical solution for many applications is Post-Quantum Cryptography (PQC). PQC refers to cryptographic algorithms that are designed to be secure against both classical and quantum computers.
Researchers are developing new mathematical problems that are believed to be hard for both classical and quantum computers to solve. These include lattice-based cryptography, code-based cryptography, hash-based cryptography, and multivariate polynomial cryptography. The goal is to transition to these new algorithms before quantum computers become powerful enough to break current encryption standards.
Standardization Efforts
Organizations like the National Institute of Standards and Technology (NIST) are actively working to standardize PQC algorithms. This process involves rigorous testing and analysis to identify algorithms that offer the best balance of security, performance, and efficiency for widespread adoption. The successful standardization will pave the way for integrating these new cryptographic methods into our existing systems.
Implementing Future-Proof Security
Securing your documents against future threats requires a multi-faceted approach. While the transition to post-quantum cryptography is underway, you can take immediate steps to enhance your document security. This includes using strong, unique passwords for encrypted files, enabling two-factor authentication where possible, and keeping your software updated.
For businesses, it's essential to stay informed about the latest developments in cryptography and to plan for the eventual migration to PQC algorithms. This proactive stance will ensure that your data remains secure in the face of evolving technological capabilities and potential threats.
Comparison Table: Encryption Approaches
| Method | Security Basis | Vulnerability to Quantum Computing | Implementation Complexity | Primary Use Case |
|---|---|---|---|---|
| Classical Public-Key Cryptography (e.g., RSA) | Mathematical complexity (factoring large numbers) | High (vulnerable to Shor's algorithm) | Moderate | Current secure communication, digital signatures |
| Quantum Key Distribution (QKD) | Principles of quantum mechanics (no-cloning theorem, measurement disturbance) | None (theoretically unhackable) | High (requires specialized hardware) | Secure key exchange for critical infrastructure |
| Post-Quantum Cryptography (PQC) | New mathematical problems believed to be hard for quantum computers | Low (designed to be resistant) | Moderate to High (algorithm dependent) | Future-proofing current encryption standards, wide adoption |