
Working with sensitive documents often involves a delicate balance between accessibility and security. Sharing critical files, whether contracts, financial records, or intellectual property, requires a robust system that prevents unauthorized access while ensuring legitimate parties can retrieve them efficiently. Traditional methods, relying on email attachments, cloud storage with passwords, or encrypted USB drives, often present vulnerabilities or cumbersome workflows.
The inherent need for trust and verifiability in document exchange has led many to explore advanced solutions. Over my years in software engineering, I've seen firsthand how the limitations of existing systems can hinder collaboration and create security risks. This is where emerging technologies like blockchain offer a compelling alternative, promising a new paradigm for secure document sharing.
Table of Contents
Understanding Blockchain for Secure Sharing
At its core, blockchain is a distributed, immutable ledger that records transactions across many computers. Each block in the chain contains a list of transactions, and once a block is added, it cannot be altered without changing all subsequent blocks. This decentralized and cryptographically secured nature makes it exceptionally resilient to tampering.
Core Principles
The foundational principles of blockchain—decentralization, transparency (where applicable), immutability, and cryptographic security—are precisely what make it ideal for enhancing document sharing. Instead of a single point of failure, data is distributed, and its integrity is maintained through consensus mechanisms and advanced encryption.
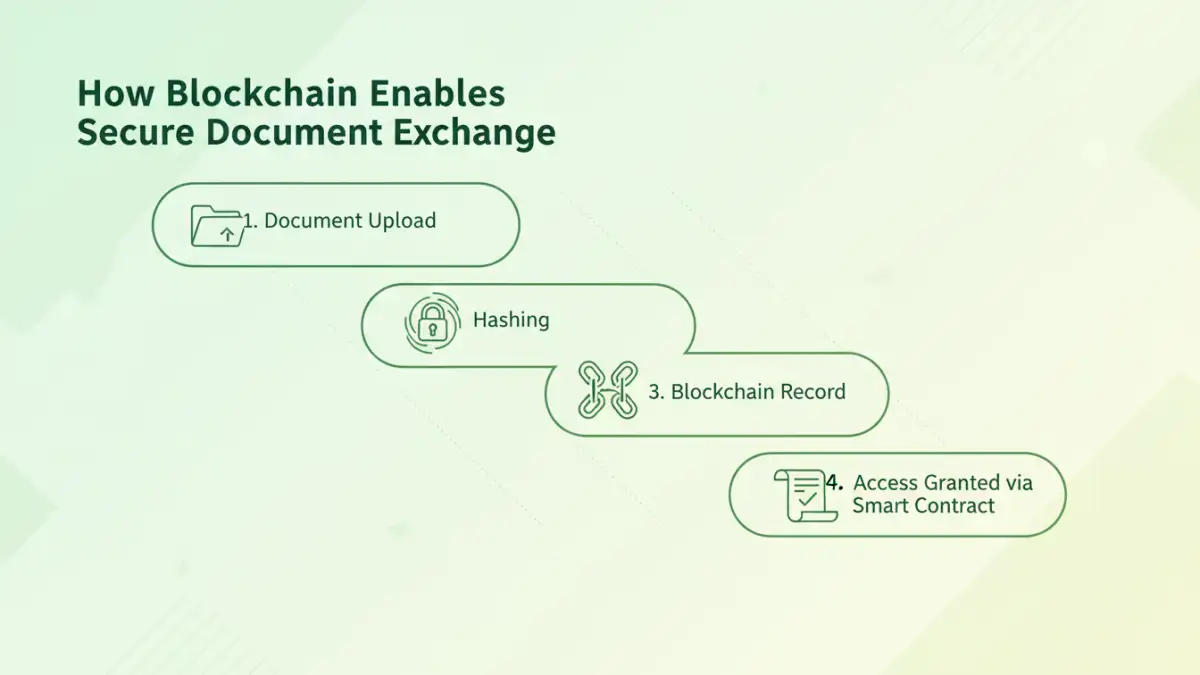
How Blockchain Enables Secure Document Exchange

When applied to document sharing, blockchain doesn't typically store the entire document on the chain itself. Instead, it stores a unique cryptographic hash (a digital fingerprint) of the document, along with metadata such as access permissions and transaction history. This hash acts as a verifiable pointer to the document's integrity.
When a document is shared, a transaction is recorded on the blockchain. This transaction can include information about who uploaded the document, who has permission to access it, and when. Any subsequent access or modification attempts are also recorded, creating a transparent and auditable trail.
Access Control and Permissions
Smart contracts, self-executing contracts with the terms of the agreement directly written into code, play a crucial role. They can automatically manage access permissions based on predefined rules. For instance, a smart contract could grant access to a specific set of users only after certain conditions are met, like payment confirmation or signing of an NDA.
Key Benefits of Blockchain Document Sharing
The advantages of using blockchain for file sharing security are significant. It offers enhanced data integrity, ensuring that documents have not been altered since they were recorded. This is critical for legal documents, financial reports, and any sensitive information where authenticity is paramount.
Another major benefit is improved security against data breaches. Because the data is distributed across a network, there's no central server to hack. The cryptographic hashing and encryption methods employed further bolster protection against unauthorized access. This approach to blockchain secure sharing creates a robust defense mechanism.
Enhanced Transparency and Auditability
Every action related to a document—uploading, sharing, accessing—can be recorded on the blockchain. This creates an immutable audit log that is accessible to authorized parties. This level of transparency is invaluable for compliance, dispute resolution, and maintaining accountability.
Implementing Blockchain Secure Sharing
Implementing blockchain for document sharing can take several forms. One common approach involves using blockchain-based platforms designed for secure file storage and collaboration. These platforms leverage blockchain to manage metadata and access controls while often using distributed storage solutions like IPFS (InterPlanetary File System) for the actual files.
Another method involves integrating blockchain functionalities into existing document management systems. This could mean using blockchain to timestamp documents, verify their integrity, or manage access rights through smart contracts. For developers, building custom solutions using blockchain protocols and smart contract languages like Solidity is also an option, offering maximum flexibility but requiring significant technical expertise.
Choosing the Right Platform
When selecting a solution, consider factors like the type of blockchain being used (public, private, or consortium), the platform's scalability, its user-friendliness, and its adherence to privacy regulations. The best approach often depends on the specific needs and technical capabilities of the organization.
Challenges and Considerations
Despite its advantages, blockchain secure sharing isn't without its challenges. The complexity of the technology can be a barrier to adoption. Implementing and managing blockchain solutions often requires specialized skills, and the initial setup costs can be substantial.
Scalability remains a concern for some blockchain networks, which can affect transaction speeds and costs, especially for public blockchains. Furthermore, while blockchain ensures data integrity, the privacy of the data itself still relies on robust encryption methods. Users must also be mindful of the immutability of the ledger; incorrect data recorded on the blockchain can be difficult to rectify.
Comparison Table
| Feature | Traditional Cloud Storage | Blockchain Secure Sharing | Pros | Cons |
|---|---|---|---|---|
| Data Integrity | Relies on server-side checks, can be compromised | Immutable through cryptographic hashing | High assurance of no tampering | |
| Security Against Breaches | Centralized servers are targets | Decentralized, no single point of failure | Resilient to hacking | |
| Audit Trail | Logged by service provider, can be altered | Immutable, transparent ledger of all actions | Complete and verifiable history | |
| Access Control | Managed by service provider, potential backdoors | Managed via smart contracts, granular permissions | Automated, secure, and customizable | Complexity |
| Cost | Subscription-based, variable | Can involve development/platform costs, transaction fees | Long-term security benefits | Initial investment |